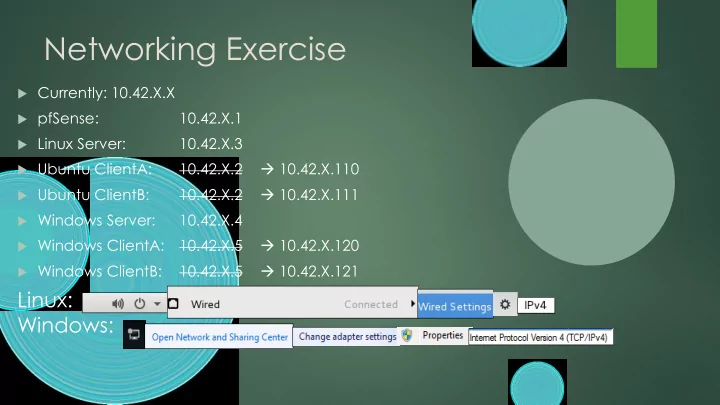
Networking Exercise
Currently: 10.42.X.X pfSense:
10.42.X.1
Linux Server:
10.42.X.3
Ubuntu ClientA:
10.42.X.2 10.42.X.110
Ubuntu ClientB:
10.42.X.2 10.42.X.111
Windows Server:
10.42.X.4
Windows ClientA:
10.42.X.5 10.42.X.120
Windows ClientB:
10.42.X.5 10.42.X.121