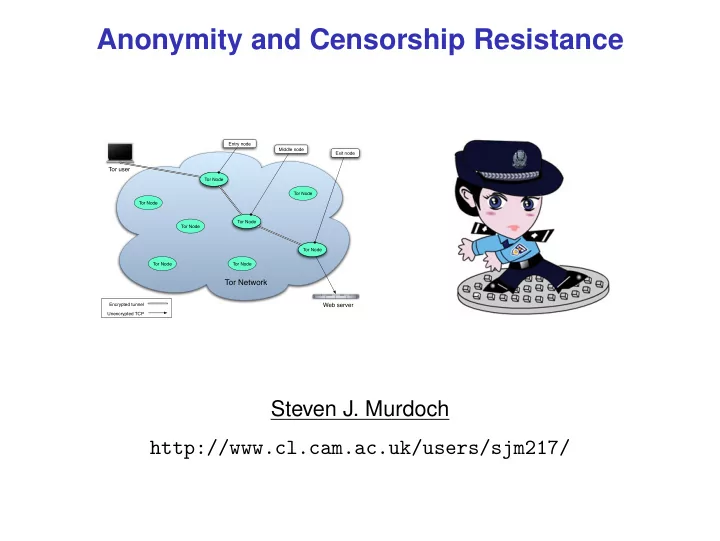
Anonymity and Censorship Resistance
Tor Node Tor Node Tor Node Tor Node Tor Node Tor Node Tor Node Tor Node
Tor Network
Web server Tor user
Encrypted tunnel Unencrypted TCP Tor Node Tor Node Tor Node Exit node Entry node Middle node
Anonymity and Censorship Resistance Entry node Middle node Exit - - PowerPoint PPT Presentation
Anonymity and Censorship Resistance Entry node Middle node Exit node Tor user Tor Node Tor Node Tor Node Tor Node Tor Node Tor Node Tor Node Tor Node Tor Node Tor Node Tor Node Tor Network Encrypted tunnel Web server Unencrypted
Tor Node Tor Node Tor Node Tor Node Tor Node Tor Node Tor Node Tor Node
Tor Network
Web server Tor user
Encrypted tunnel Unencrypted TCP Tor Node Tor Node Tor Node Exit node Entry node Middle node
UAE, Iran, Bahrain)
Arabia, UAE, Iran, Bahrain, Singapore, Burma, . . . )
UAE, Iran, Bahrain)
Arabia, UAE, Iran, Bahrain, Singapore, Burma, . . . )
UAE, Iran, Bahrain)
Arabia, UAE, Iran, Bahrain, Singapore, Burma, . . . )
WEB BROWSER ISP INTERNET
User DNS Server DNS Server Web Server
Router
normal_no proxy.indd 1 3/19/07 8:56:55 PM
Diagram: Jane Gowan
WEB BROWSER ISP INTERNET
User DNS Server DNS Server Web Server
Router
DNS_tampering.indd 1 3/19/07 8:56:18 PM
Diagram: Jane Gowan
WEB BROWSER ISP INTERNET
User DNS Server DNS Server Web Server
Router
IP blocking.indd 1 3/19/07 8:56:32 PM
Diagram: Jane Gowan
webpages
Photograph: David Gaya
For Mix 2
For D
Kpub 2 Mix 1 Kpriv 1 Mix 2 Kpriv 2 Mix 3 Kpriv 3
For C
Kpub 3
For Mix 3
Kpub 1 Kpub 3
Mix
Mix
Mix
Mix
Mix
Mix
Mix
7% 3% 2% 9% 100% ...
messages received by Bob messages received in total
Mix
5% 2% 1% 8% 100% ... 4% 15% 20% 7% 100% ... Alice Alice not sending Alice sending Rounds when:
Tor Node Tor Node Tor Node Tor Node Tor Node Tor Node Tor Node Tor Node
Tor Network
Web server Tor user
Diagram: Robert Watson
Tor Node Tor Node Tor Node Tor Node Tor Node Tor Node Tor Node Tor Node
Tor Network
Web server Tor user
Tor Node Tor Node Tor Node Exit node Entry node Middle node
Diagram: Robert Watson
Tor Node Tor Node Tor Node Tor Node Tor Node Tor Node Tor Node Tor Node
Tor Network
Web server Tor user
Encrypted tunnel Unencrypted TCP Tor Node Tor Node Tor Node Exit node Entry node Middle node
Diagram: Robert Watson
Entry Middle Exit
Data
User
1d ae cd 59 ... e4 50 de 5a ... 00 02 28 be ...
Entry Middle Exit
Data
User
1d ae cd 59 ... e4 50 de 5a ... 00 02 28 be ...
Entry Middle Exit
Data
User
1d ae cd 59 ... e4 50 de 5a ... 00 02 28 be ...
Mix
5% 2% 1% 8% 100% ... 4% 15% 20% 7% 100% ... Alice Alice not sending Alice sending Rounds when: