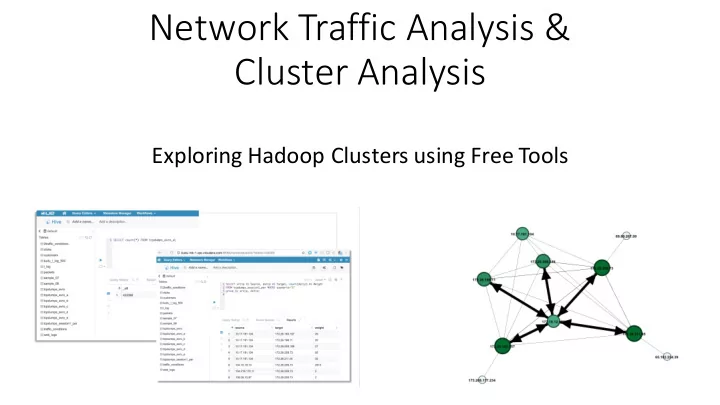
SLIDE 1
Background and Goals:
- Apache Spot was started recently
- DNS, Netflow, PCAP data is analyzed
- The goal is to identify:
”suspicous connections”
- r:
“dangerous activity”.
- What is suspicious?
- Apache Spot uses a topic-model approach, to classify traffic.