S-38.2121 / Fall-2007 / RKa, NB Multicast1-1
Multicast routing principles in Internet
Motivation Recap on graphs Principles and algorithms
S-38.2121 / Fall-2007 / RKa, NB Multicast1-2
Multicast routing principles in Internet Motivation Recap on graphs - - PDF document
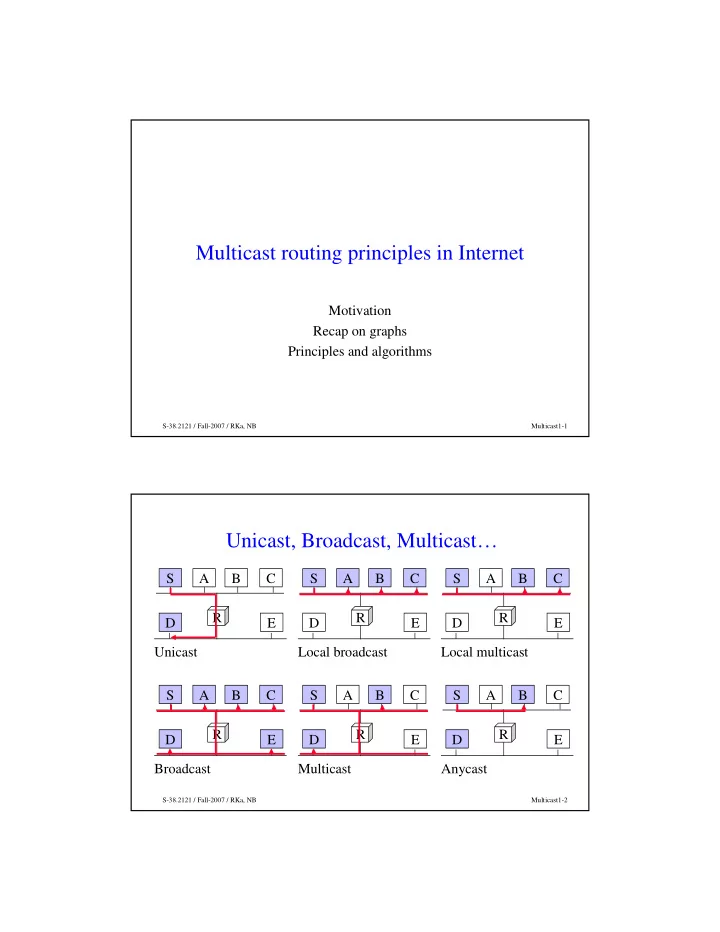
Multicast routing principles in Internet Motivation Recap on graphs Principles and algorithms S-38.2121 / Fall-2007 / RKa, NB Multicast1-1 Unicast, Broadcast, Multicast S A B C S A B C S A B C R R R D E D E D E Unicast
S-38.2121 / Fall-2007 / RKa, NB Multicast1-1
S-38.2121 / Fall-2007 / RKa, NB Multicast1-2
S-38.2121 / Fall-2007 / RKa, NB Multicast1-3
S-38.2121 / Fall-2007 / RKa, NB Multicast1-4
S-38.2121 / Fall-2007 / RKa, NB Multicast1-5
S-38.2121 / Fall-2007 / RKa, NB Multicast1-6
S-38.2121 / Fall-2007 / RKa, NB Multicast1-7
S-38.2121 / Fall-2007 / RKa, NB Multicast1-8
S-38.2121 / Fall-2007 / RKa, NB Multicast1-9
S-38.2121 / Fall-2007 / RKa, NB Multicast1-10
S-38.2121 / Fall-2007 / RKa, NB Multicast1-11
S-38.2121 / Fall-2007 / RKa, NB Multicast1-12
S-38.2121 / Fall-2007 / RKa, NB Multicast1-13
S-38.2121 / Fall-2007 / RKa, NB Multicast1-14
S-38.2121 / Fall-2007 / RKa, NB Multicast1-15
S-38.2121 / Fall-2007 / RKa, NB Multicast1-16
S-38.2121 / Fall-2007 / RKa, NB Multicast1-17
S-38.2121 / Fall-2007 / RKa, NB Multicast1-18
S-38.2121 / Fall-2007 / RKa, NB Multicast1-19
S-38.2121 / Fall-2007 / RKa, NB Multicast1-20
S-38.2121 / Fall-2007 / RKa, NB Multicast1-21
S-38.2121 / Fall-2007 / RKa, NB Multicast1-22
S-38.2121 / Fall-2007 / RKa, NB Multicast1-23
S-38.2121 / Fall-2007 / RKa, NB Multicast1-25
S-38.2121 / Fall-2007 / RKa, NB Multicast1-26
S-38.2121 / Fall-2007 / RKa, NB Multicast1-27
S-38.2121 / Fall-2007 / RKa, NB Multicast1-28
S-38.2121 / Fall-2007 / RKa, NB Multicast1-29
S-38.2121 / Fall-2007 / RKa, NB Multicast1-30
S-38.2121 / Fall-2007 / RKa, NB Multicast1-31
S-38.2121 / Fall-2007 / RKa, NB Multicast1-32
S-38.2121 / Fall-2007 / RKa, NB Multicast1-33
S-38.2121 / Fall-2007 / RKa, NB Multicast1-34
S-38.2121 / Fall-2007 / RKa, NB Multicast1-35
S-38.2121 / Fall-2007 / RKa, NB Multicast1-36
S-38.2121 / Fall-2007 / RKa, NB Multicast1-37
S-38.2121 / Fall-2007 / RKa, NB Multicast1-38
S-38.2121 / Fall-2007 / RKa, NB Multicast1-39
S-38.2121 / Fall-2007 / RKa, NB Multicast1-40
S-38.2121 / Fall-2007 / RKa, NB Multicast1-41
S-38.2121 / Fall-2007 / RKa, NB Multicast1-42
S-38.2121 / Fall-2007 / RKa, NB Multicast1-43
G1 G1 S2
S1
G1 S3
S-38.2121 / Fall-2007 / RKa, NB Multicast1-44
G1 G1
S1 G1 192.7.1/24
G1 G1 S2
S3
G1
G1 G1 S2
G1
S-38.2121 / Fall-2007 / RKa, NB Multicast1-45
G1 G1 S2
S1
G1 S3