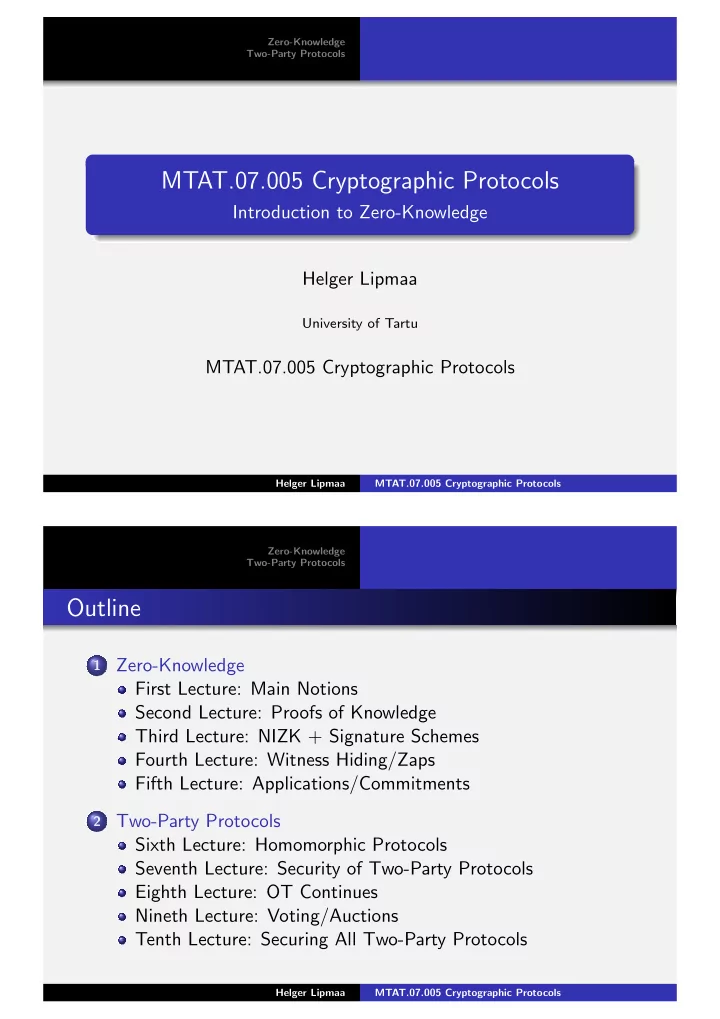
SLIDE 121 Zero-Knowledge Two-Party Protocols Sixth Lecture: Homomorphic Protocols Seventh Lecture: Security of Two-Party Protocols Eighth Lecture: OT Continues Nineth Lecture: Voting/Auctions Tenth Lecture: Securing All Two-Party Protocols
References I
Aiello, W., Ishai, Y., and Reingold, O. (2001). Priced Oblivious Transfer: How to Sell Digital Goods. In Pfitzmann, B., editor, Advances in Cryptology — EUROCRYPT 2001, volume 2045 of Lecture Notes in Computer Science, pages 119–135, Innsbruck, Austria. Springer-Verlag. Damg˚ ard, I. (2000). Efficient Concurrent Zero-Knowledge in the Auxiliary String Model. In Preneel, B., editor, Advances in Cryptology — EUROCRYPT 2000, volume 1807 of Lecture Notes in Computer Science, pages 418–430, Bruges, Belgium. Springer-Verlag. Damg˚ ard, I. and Fujisaki, E. (2002). An Integer Commitment Scheme Based on Groups with Hidden Order. In Zheng, Y., editor, Advances on Cryptology — ASIACRYPT 2002, volume 2501 of Lecture Notes in Computer Science, pages 125–142, Queenstown, New Zealand. Springer-Verlag. Damg˚ ard, I. and Jurik, M. (2001). A Generalisation, a Simplification and Some Applications of Paillier’s Probabilistic Public-Key System. In Kim, K., editor, Public Key Cryptography 2001, volume 1992 of Lecture Notes in Computer Science, pages 119–136, Cheju Island, Korea. Springer-Verlag. Helger Lipmaa MTAT.07.005 Cryptographic Protocols Zero-Knowledge Two-Party Protocols Sixth Lecture: Homomorphic Protocols Seventh Lecture: Security of Two-Party Protocols Eighth Lecture: OT Continues Nineth Lecture: Voting/Auctions Tenth Lecture: Securing All Two-Party Protocols
References II
De Santis, A., Di Crescenzo, G., Ostrovsky, R., Persiano, G., and Sahai, A. (2001). Robust Non-interactive Zero Knowledge. In Kilian, J., editor, Advances in Cryptology — CRYPTO 2001, 21st Annual International Cryptology Conference, volume 2139 of Lecture Notes in Computer Science, pages 566–598, Santa Barbara, USA. Springer-Verlag. Goldreich, O. (2004). Foundations of Cryptography: Basic Applications. Cambridge University Press. Goldwasser, S. and Kalai, Y. T. (2003). On the (In)security of the Fiat-Shamir Paradigm. In 44th Annual Symposium on Foundations of Computer Science, pages 102–113, Cambridge, MA, USA. IEEE, IEEE Computer Society Press. Goldwasser, S., Micali, S., and Rackoff, C. (1989). The Knowledge Complexity of Interactive Proof Systems. SIAM Journal of Computing, 18(1):186–208. Katz, J. and Wang, N. (2003). Efficiency Improvements for Signature Schemes with Tight Security Reductions. In 10th ACM Conference on Computer and Communications Security, pages 155–164, Washington, D.C.,
Helger Lipmaa MTAT.07.005 Cryptographic Protocols