Zero-Knowledge Two-Party Protocols
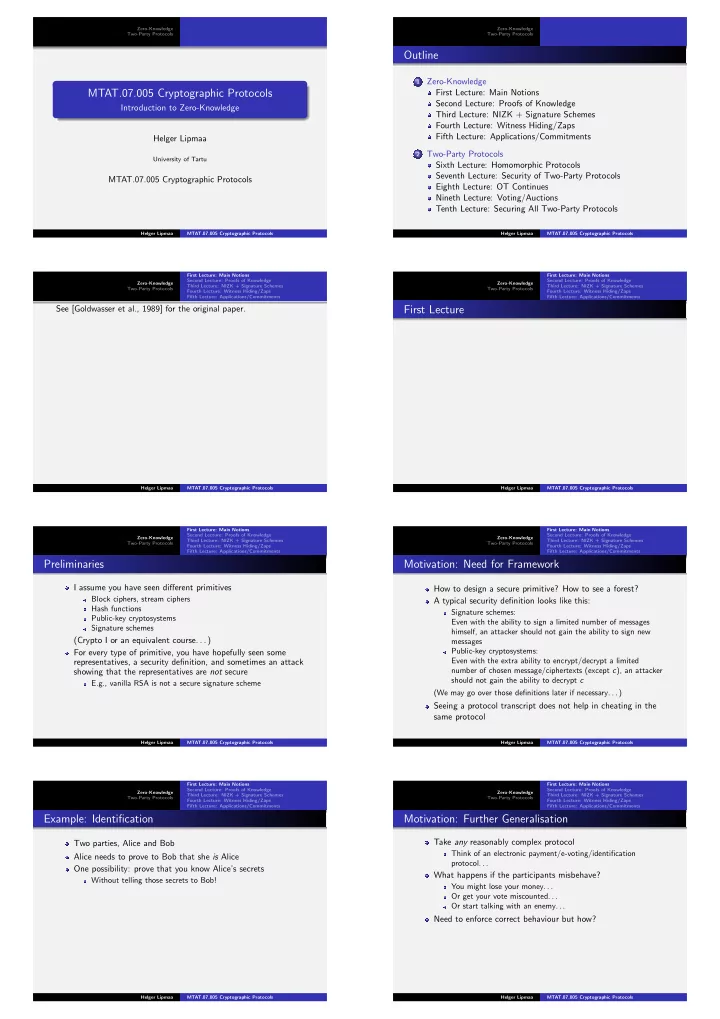
MTAT.07.005 Cryptographic Protocols
Introduction to Zero-Knowledge Helger Lipmaa
University of Tartu
MTAT.07.005 Cryptographic Protocols
Helger Lipmaa MTAT.07.005 Cryptographic Protocols Zero-Knowledge Two-Party Protocols
Outline
1 Zero-Knowledge
First Lecture: Main Notions Second Lecture: Proofs of Knowledge Third Lecture: NIZK + Signature Schemes Fourth Lecture: Witness Hiding/Zaps Fifth Lecture: Applications/Commitments
2 Two-Party Protocols
Sixth Lecture: Homomorphic Protocols Seventh Lecture: Security of Two-Party Protocols Eighth Lecture: OT Continues Nineth Lecture: Voting/Auctions Tenth Lecture: Securing All Two-Party Protocols
Helger Lipmaa MTAT.07.005 Cryptographic Protocols Zero-Knowledge Two-Party Protocols First Lecture: Main Notions Second Lecture: Proofs of Knowledge Third Lecture: NIZK + Signature Schemes Fourth Lecture: Witness Hiding/Zaps Fifth Lecture: Applications/Commitments
See [Goldwasser et al., 1989] for the original paper.
Helger Lipmaa MTAT.07.005 Cryptographic Protocols Zero-Knowledge Two-Party Protocols First Lecture: Main Notions Second Lecture: Proofs of Knowledge Third Lecture: NIZK + Signature Schemes Fourth Lecture: Witness Hiding/Zaps Fifth Lecture: Applications/Commitments
First Lecture
Helger Lipmaa MTAT.07.005 Cryptographic Protocols Zero-Knowledge Two-Party Protocols First Lecture: Main Notions Second Lecture: Proofs of Knowledge Third Lecture: NIZK + Signature Schemes Fourth Lecture: Witness Hiding/Zaps Fifth Lecture: Applications/Commitments
Preliminaries
I assume you have seen different primitives
Block ciphers, stream ciphers Hash functions Public-key cryptosystems Signature schemes
(Crypto I or an equivalent course. . . ) For every type of primitive, you have hopefully seen some representatives, a security definition, and sometimes an attack showing that the representatives are not secure
E.g., vanilla RSA is not a secure signature scheme
Helger Lipmaa MTAT.07.005 Cryptographic Protocols Zero-Knowledge Two-Party Protocols First Lecture: Main Notions Second Lecture: Proofs of Knowledge Third Lecture: NIZK + Signature Schemes Fourth Lecture: Witness Hiding/Zaps Fifth Lecture: Applications/Commitments
Motivation: Need for Framework
How to design a secure primitive? How to see a forest? A typical security definition looks like this:
Signature schemes: Even with the ability to sign a limited number of messages himself, an attacker should not gain the ability to sign new messages Public-key cryptosystems: Even with the extra ability to encrypt/decrypt a limited number of chosen message/ciphertexts (except c), an attacker should not gain the ability to decrypt c (We may go over those definitions later if necessary. . . )
Seeing a protocol transcript does not help in cheating in the same protocol
Helger Lipmaa MTAT.07.005 Cryptographic Protocols Zero-Knowledge Two-Party Protocols First Lecture: Main Notions Second Lecture: Proofs of Knowledge Third Lecture: NIZK + Signature Schemes Fourth Lecture: Witness Hiding/Zaps Fifth Lecture: Applications/Commitments
Example: Identification
Two parties, Alice and Bob Alice needs to prove to Bob that she is Alice One possibility: prove that you know Alice’s secrets
Without telling those secrets to Bob!
Helger Lipmaa MTAT.07.005 Cryptographic Protocols Zero-Knowledge Two-Party Protocols First Lecture: Main Notions Second Lecture: Proofs of Knowledge Third Lecture: NIZK + Signature Schemes Fourth Lecture: Witness Hiding/Zaps Fifth Lecture: Applications/Commitments
Motivation: Further Generalisation
Take any reasonably complex protocol
Think of an electronic payment/e-voting/identification
- protocol. . .
What happens if the participants misbehave?
You might lose your money. . . Or get your vote miscounted. . . Or start talking with an enemy. . .
Need to enforce correct behaviour but how?
Helger Lipmaa MTAT.07.005 Cryptographic Protocols