11/1/15 1
MOBILE COMPUTING
CSE 40814/60814 Fall 2015
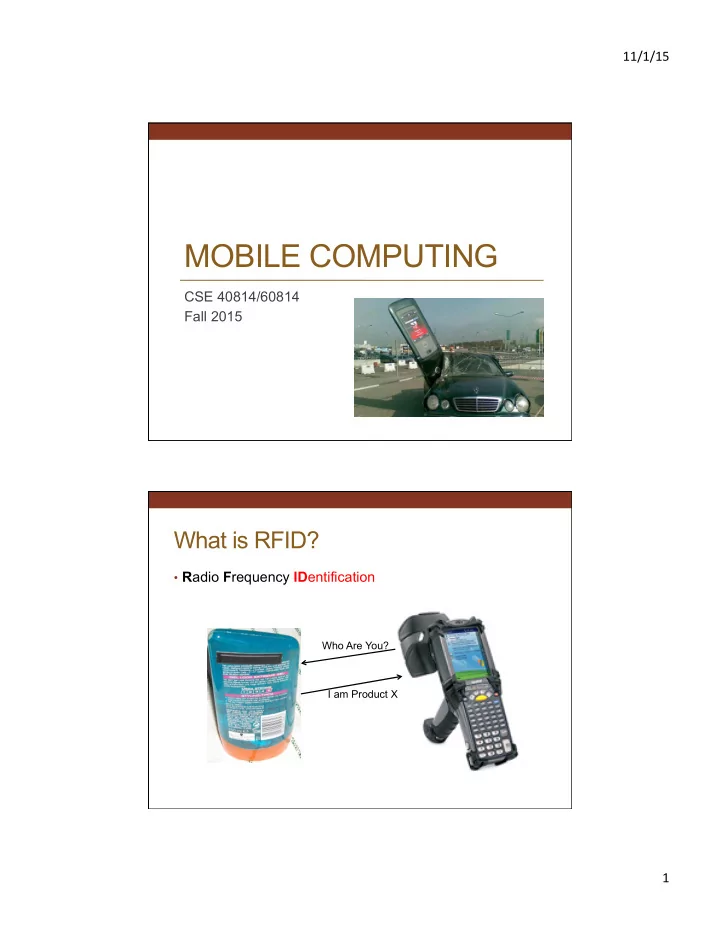
What is RFID?
- Radio Frequency IDentification
Who Are You? I am Product X
MOBILE COMPUTING CSE 40814/60814 Fall 2015 What is RFID? R adio F - - PDF document
11/1/15 MOBILE COMPUTING CSE 40814/60814 Fall 2015 What is RFID? R adio F requency ID entification Who Are You? I am Product X 1 11/1/15 RFID ADC (automated data collection) technology that uses radio-frequency waves to transfer
11/1/15 1
CSE 40814/60814 Fall 2015
Who Are You? I am Product X
11/1/15 2
technology that uses radio-frequency waves to transfer data between a reader and a movable item to identify, categorize, track...
physical sight or contact between reader/ scanner and the tagged item
technology
“intelligent” than sensor nodes
technologies is blurring
bombers during World War II
introduced by Harry Stockman
patented an “inductively coupled transmitter- responder” (2 antennas)
device” which combined both antennas into one
Livermore Laboratory (LLL) build a handheld receiver stimulated by RF power for secure access to nuclear facilities
11/1/15 3
Main components:
and waits for response
Variations:
many tags at a time
11/1/15 4
11/1/15 5
Active RFID Passive RFID Tag Power Source
Internal to tag Energy transferred using RF from reader
Tag Battery
Yes No
Required signal strength
Very Low Very High
Range
Up to 100m Up to 3-5m, usually less
Multi-tag reading
1000’s of tags recognized – up to 100mph Few hundred within 3m of reader, about 3 sec per read => at most 3 mph.
Data Storage
Up to 512 KB 16 bits – 1 KB
11/1/15 6
11/1/15 7
11/1/15 8
Computer Science and Engineering - University of Notre Dame
11/1/15 9
Transmitting EPCs Creating EPCs
11/1/15 10
11/1/15 11
protocols
(can reduce occurrence of collisions)
tag ID and that tag will not send anymore)
11/1/15 12
people, e.g., Alzheimer patients
Computer Science and Engineering - University of Notre Dame
11/1/15 13
between 1 and 1.5cm long
neck
“Chip to remove shopping blues”
—Post-Courier, January 1994 “Tiny microchip identifies groceries in seconds.”
—Chicago Tribune
“Checkout in one minute”
—The Times, London
“Scanning range of four yards”
—NY Times
“1.5¢ electronic bar code announced”
—San Francisco Chronicle
11/1/15 14
Visibility Time
Technology Trigger Peak of Inflated Expectations Trough of Disillusionment Slope of Enlightenment Plateau of Productivity RFID Today!
11/1/15 15
with a Radio Frequency Identification (RFID) supplier requirement when it announced a pallet and case level tagging initiative. Currently, over 600 suppliers are participating in the initiative. Today, Walmart requires that its top suppliers must be RFID compliant, at the pallet and
notified regarding their target compliance dates. As time progresses RFID benefits will continue to surface as well as the technology will become cheaper and easier to integrate.
11/1/15 16
technology, NFC offers safe yet simple communication between electronic devices.
distance of 4 cm or less.
kbit/s to 848 kbit/s.
31
field induction between electronic devices in close proximity.
must have an NFC reader/writer and one must have an NFC tag. The tag is essentially an integrated circuit containing data, connected to an antenna, that can be read
11/1/15 17
IEC14443 proximity-card standard (contactless card, RFID) that combines the interface of a smartcard and a reader into a single device
ISO/IEC14443 smartcards and readers, as well as with other NFC devices, and is thereby compatible with contactless infrastructure already in use for public transportation and payment
(estimate that 5% are used at least once a month)
There are currently three main uses of NFC:
existing contactless card
passive RFID tag, for example for interactive advertising
and exchanging information
11/1/15 18
network connections such as Bluetooth or Wi-Fi
35
11/1/15 19
advantages)
information
11/1/15 20