Chaskey ARX Cryptanalysis Improved Differential-Linear Conclusion
Improved Differential-Linear Cryptanalysis
- f 7-round Chaskey with Partitioning
Gaëtan Leurent
Inria, Paris
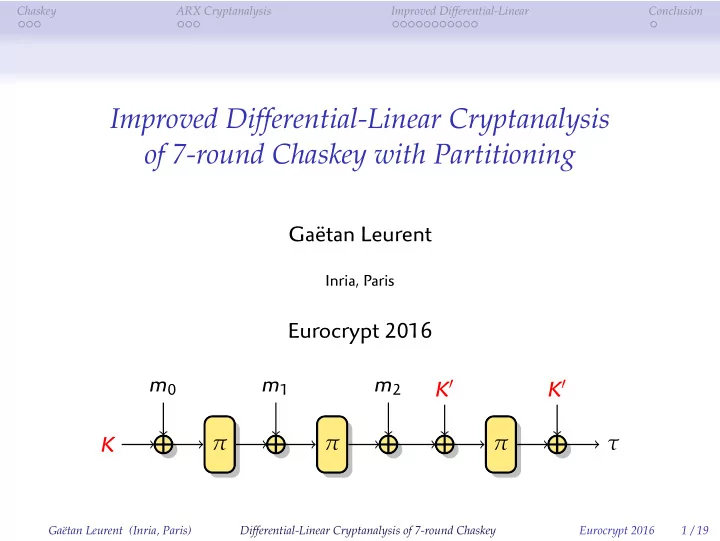
Eurocrypt 2016 K m0 π m1 π m2 K′ π K′ τ
Gaëtan Leurent (Inria, Paris) Differential-Linear Cryptanalysis of 7-round Chaskey Eurocrypt 2016 1 / 19