1
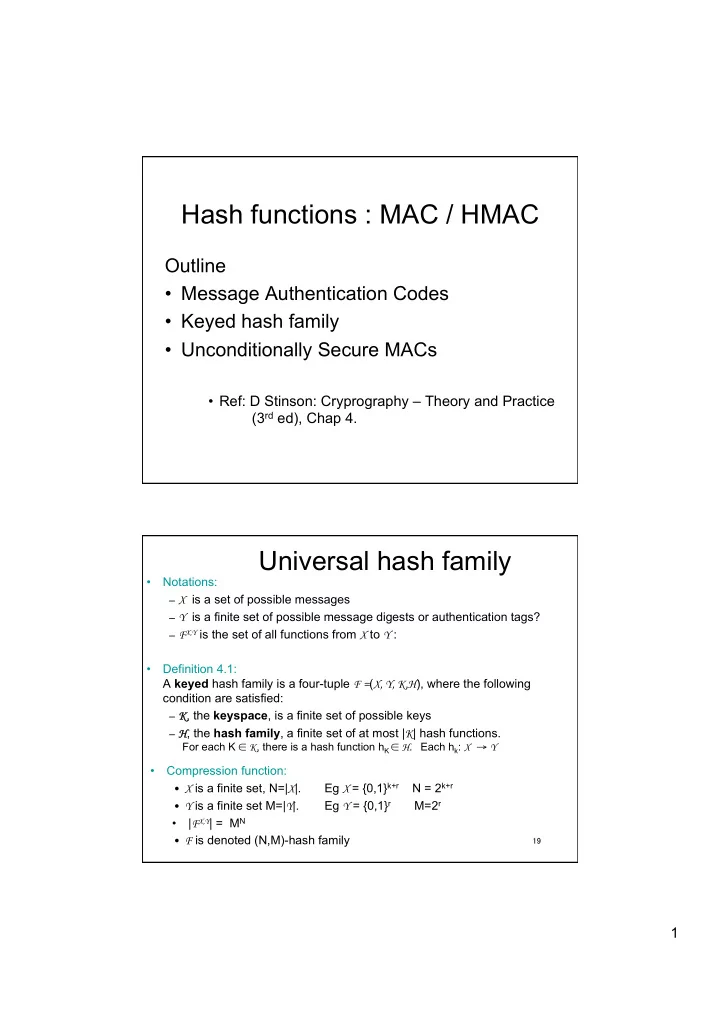
Hash functions : MAC / HMAC
Outline
- Message Authentication Codes
- Keyed hash family
- Unconditionally Secure MACs
- Ref: D Stinson: Cryprography – Theory and Practice
(3rd ed), Chap 4.
19
Universal hash family
- Notations:
– X is a set of possible messages – Y is a finite set of possible message digests or authentication tags? – FX,Y is the set of all functions from X to Y :
- Definition 4.1:
A keyed hash family is a four-tuple F =(X, Y, K,H), where the following condition are satisfied: – K, the keyspace, is a finite set of possible keys – H, the hash family, a finite set of at most |K| hash functions.
For each K ∈ K, there is a hash function hK ∈ H. Each hk: X → Y
- Compression function:
- X is a finite set, N=|X|.
Eg X = {0,1}k+r N = 2k+r
- Y is a finite set M=|Y|.
Eg Y = {0,1}r M=2r
- |FX,Y| = MN
- F is denoted (N,M)-hash family