HASH FUNCTIONS Mihir Bellare UCSD 1 Mihir Bellare UCSD 2 Hash - PowerPoint PPT Presentation
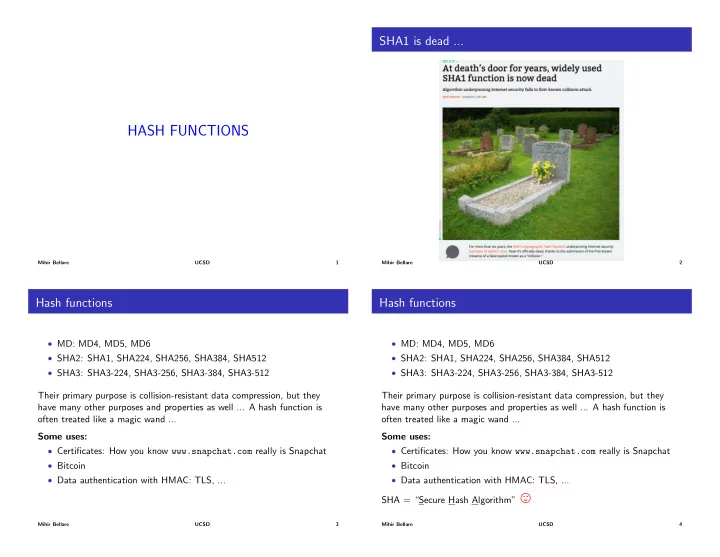
SHA1 is dead ... HASH FUNCTIONS Mihir Bellare UCSD 1 Mihir Bellare UCSD 2 Hash functions Hash functions MD: MD4, MD5, MD6 MD: MD4, MD5, MD6 SHA2: SHA1, SHA224, SHA256, SHA384, SHA512 SHA2: SHA1, SHA224, SHA256, SHA384,
SHA1 is dead ... HASH FUNCTIONS Mihir Bellare UCSD 1 Mihir Bellare UCSD 2 Hash functions Hash functions • MD: MD4, MD5, MD6 • MD: MD4, MD5, MD6 • SHA2: SHA1, SHA224, SHA256, SHA384, SHA512 • SHA2: SHA1, SHA224, SHA256, SHA384, SHA512 • SHA3: SHA3-224, SHA3-256, SHA3-384, SHA3-512 • SHA3: SHA3-224, SHA3-256, SHA3-384, SHA3-512 Their primary purpose is collision-resistant data compression, but they Their primary purpose is collision-resistant data compression, but they have many other purposes and properties as well ... A hash function is have many other purposes and properties as well ... A hash function is often treated like a magic wand ... often treated like a magic wand ... Some uses: Some uses: • Certificates: How you know www.snapchat.com really is Snapchat • Certificates: How you know www.snapchat.com really is Snapchat • Bitcoin • Bitcoin • Data authentication with HMAC: TLS, ... • Data authentication with HMAC: TLS, ... SHA = “Secure Hash Algorithm” , Mihir Bellare UCSD 3 Mihir Bellare UCSD 4
A SHA1 certificate SHA1 certificates no longer Mihir Bellare UCSD 5 Mihir Bellare UCSD 6 Implications for Bitcoin? Collisions A collision for a function h : D ! { 0 , 1 } n is a pair x 1 , x 2 2 D of points such that • h ( x 1 ) = h ( x 2 ), and • x 1 6 = x 2 . If | D | > 2 n then the pigeonhole principle tells us that there must exist a collision for h . Mihir Bellare UCSD 7 Mihir Bellare UCSD 8
Collisions Collisions A collision for a function h : D ! { 0 , 1 } n is a pair x 1 , x 2 2 D of points A collision for a function h : D ! { 0 , 1 } n is a pair x 1 , x 2 2 D of points such that such that • h ( x 1 ) = h ( x 2 ), and • h ( x 1 ) = h ( x 2 ), and • x 1 6 = x 2 . • x 1 6 = x 2 . If | D | > 2 n then the pigeonhole principle tells us that there must exist a If | D | > 2 n then the pigeonhole principle tells us that there must exist a collision for h . collision for h . We want that even though collisions exist, they are hard to find . Mihir Bellare UCSD 9 Mihir Bellare UCSD 10 Collision-resistance of a function family Collision-resistance The formalism considers a family H : Keys ⇥ D ! R of functions, meaning Game CR H procedure Finalize ( x 1 , x 2 ) for each K 2 Keys we have a function H K : D ! R defined by H K ( x ) = If ( x 1 = x 2 ) then return false H ( K , x ). procedure Initialize If ( x 1 62 D or x 2 62 D ) then return false $ K Keys Game CR H Return ( H K ( x 1 ) = H K ( x 2 )) procedure Finalize ( x 1 , x 2 ) Return K If ( x 1 = x 2 ) then return false procedure Initialize The Return statement in Initialize means that the adversary A gets K as If ( x 1 62 D or x 2 62 D ) then return false $ K Keys Return ( H K ( x 1 ) = H K ( x 2 )) input. The key K here is not secret! Return K Adversary A takes K and tries to output a collision x 1 , x 2 for H K . Let h i CR A H ( A ) = Pr H ) true . Adv cr A ’s output is the input to Finalize , and the game returns true if the collision is valid. Mihir Bellare UCSD 11 Mihir Bellare UCSD 12
Example Example Let N = 2 256 and define Let N = 2 256 and define H : { 1 , . . . , N } ⇥ { 0 , 1 , 2 , . . . } ! { 0 , 1 , . . . , N � 1 } H : { 1 , . . . , N } ⇥ { 0 , 1 , 2 , . . . } ! { 0 , 1 , . . . , N � 1 } | {z } | {z } | {z } | {z } | {z } | {z } Keys Keys D R D R by by H ( K , x ) = ( x mod K ) . H ( K , x ) = ( x mod K ) . Q: Is H collision resistant? Q: Is H collision resistant? A: NO! Why? ( x + K ) mod K = x mod K adversary A ( K ) x 1 0 ; x 2 K ; Return x 1 , x 2 Adv cr H ( A ) = 1 Mihir Bellare UCSD 13 Mihir Bellare UCSD 14 Example Example Let E : { 0 , 1 } k ⇥ { 0 , 1 } n ! { 0 , 1 } n be a blockcipher. Let E : { 0 , 1 } k ⇥ { 0 , 1 } n ! { 0 , 1 } n be a blockcipher. Let H : { 0 , 1 } k ⇥ { 0 , 1 } 2 n ! { 0 , 1 } n be defined by Let H : { 0 , 1 } k ⇥ { 0 , 1 } 2 n ! { 0 , 1 } n be defined by Alg H ( K , x [1] x [2]) Alg H ( K , x [1] x [2]) y E K ( E K ( x [1]) � x [2]); Return y y E K ( E K ( x [1]) � x [2]); Return y Let’s show that H is not collision-resistant by giving an e ffi cient adversary Let’s show that H is not collision-resistant by giving an e ffi cient adversary A such that Adv cr H ( A ) = 1. A such that Adv cr H ( A ) = 1. Idea: Pick x 1 = x 1 [1] x 1 [2] and x 2 = x 2 [1] x 2 [2] so that E K ( x 1 [1]) � x 1 [2] = E K ( x 2 [1]) � x 2 [2] Mihir Bellare UCSD 15 Mihir Bellare UCSD 16
Example Exercise Let E : { 0 , 1 } k ⇥ { 0 , 1 } l ! { 0 , 1 } l be a blockcipher. Let D be the set of Alg H ( K , x [1] x [2]) all strings whose length is a positive multiple of l . y E K ( E K ( x [1]) � x [2]); Return y Define the hash function H : { 0 , 1 } k ⇥ D ! { 0 , 1 } l as follows: Idea: Pick x 1 = x 1 [1] x 1 [2] and x 2 = x 2 [1] x 2 [2] so that Alg H ( K , M ) E K ( x 1 [1]) � x 1 [2] = E K ( x 2 [1]) � x 2 [2] M [1] M [2] . . . M [ n ] M C [0] 0 l adversary A ( K ) For i = 1 , . . . , n do x 1 0 n 1 n ; x 2 [2] 0 n ; x 2 [1] E − 1 K ( E K ( x 1 [1]) � x 1 [2] � x 2 [2]) B [ i ] E ( K , C [ i � 1] � M [ i ]); C [ i ] E ( K , B [ i ] � M [ i ]) return x 1 , x 2 Return C [ n ] Then Adv cr H ( A ) = 1 and A is e ffi cient, so H is not CR. Show that H is not CR by giving an e ffi cient adversary A such that Adv cr H ( A ) = 1. Note how we used the fact that A knows K and the fact that E is a blockcipher! Mihir Bellare UCSD 17 Mihir Bellare UCSD 18 Keyless hash functions SHA256 The hash function SHA256: { 0 , 1 } < 2 64 ! { 0 , 1 } 256 is keyless , with • Inputs being strings X of any length strictly less than 2 64 • Outputs always having length 256. We say that H : Keys ⇥ D ! R is keyless if Keys = { " } consists of just / | X | < 2 64 Alg SHA256( X ) / one key, the empty string. M shapad( X ) / / | M | mod 512 = 0 In this case we write H ( x ) in place of H ( " , x ) or H ε ( x ). M (1) M (2) · · · M ( n ) M / / Break M into 512 bit blocks Practical hash functions like the MD, SHA2 and SHA3 series are keyless. H (0) 6a09e6677 ; H (0) bb67ae85 ; · · · ; H (0) 5be0cd19 0 1 7 H (0) H (0) 1 H (0) · · · H (0) / | H (0) | = 32, | H (0) | = 256 / 2 7 i For i = 1 , . . . , n do H ( i ) sha256( M ( i ) k H ( i − 1) ) Return H ( n ) sha256: { 0 , 1 } 512+256 ! { 0 , 1 } 256 is the compression function . Mihir Bellare UCSD 19 Mihir Bellare UCSD 20
Padding, and initialization vector H (0) Compression function sha256 Compression function sha256: { 0 , 1 } 512+256 ! { 0 , 1 } 256 takes a 512 + 256 = 768 bit input and returns a 256-bit output. Alg shapad( X ) / / | X | < 2 64 Alg sha256( x k v ) / / X =512, v =256 d (447 � | X | ) mod 512 / / Chosen to make | M | a multiple of 512 w E sha256 ( x , v ) Let ` be the 64-bit binary representation of | M | w 0 · · · w 7 w / / Break w into 32-bit words M X k 1 k 0 d k ` / / | M | is a multiple of 512 v 0 . . . v 7 v / / Break v into 32-bit words For j = 0 , . . . , 7 do h j w j + v j return M h h 0 . . . h 7 / / | h | = 256 The 32-bit word H (0) Return h was obtained by taking the first 32 bits of the j fractional part of the square root of the j -th prime number (0 j 7). Here and on next slide, “+” denotes addition modulo 2 32 . E sha256 : { 0 , 1 } 512 ⇥ { 0 , 1 } 256 ! { 0 , 1 } 256 is a block cipher with 512-bit keys and 256-bit blocks. Mihir Bellare UCSD 21 Mihir Bellare UCSD 22 Block cipher E sha256 Internals of block cipher E sha256 Alg E sha256 ( x , v ) / / x is a 512-bit key, v is a 256-bit input x 0 · · · x 15 x / / Break x into 32-bit words For t = 0 , . . . , 15 do W t x t On the previous slide: For t = 16 , . . . , 63 do W t � 1 ( W t − 2 ) + W t − 7 + � 0 ( W t − 15 ) + W t − 16 v 0 · · · v 7 v / / Break v into 32-bit words • � 0 , � 1 , � 0 , � 1 , Ch , Maj are functions not detailed here. For j = 0 , . . . , 7 do S j v j / / Initialize 256-bit state S • C 1 = 428a2f98 , C 2 = 71374491 , . . . , C 63 = c67178f2 are Fot t = 0 , . . . , 63 do / / 64 rounds constants, where C i is the first 32 bits of the fractional part of the T 1 S 7 + � 1 ( S 4 ) + Ch ( S 4 , S 5 , S 6 ) + C t + W t cube root of the i -th prime. T 2 � 0 ( S 0 ) + Maj ( S 0 , S 1 , S 2 ) S 7 S 6 ; S 6 S 5 ; S 5 S 4 ; S 4 S 3 + T 1 S 3 S 2 ; S 2 S 1 ; S 1 S 0 ; S 0 T 1 + T 2 S S 0 · · · S 7 Return S / / 256-bit output Mihir Bellare UCSD 23 Mihir Bellare UCSD 24
SHA256 hash calculator Usage of hash functions http://www.xorbin.com/tools/sha256-hash-calculator Uses include hashing the data before signing in creation of certificates, data authentication with HMAC, key-derivation, Bitcoin, ... These will have to wait, so we illustrate another use, the hashing of passwords. Mihir Bellare UCSD 25 Mihir Bellare UCSD 26 Authentication via passwords Hashed passwords • Client A has a password PW and server stores PW = H ( PW ). • Client A has a password PW that is also stored by server B • A authenticates itself by sending PW to B over a secure channel • A sends PW to B (over a secure channel) and B checks that H ( PW ) = PW (TLS) PW A PW - B PW PW A PW - B PW Server compromise results in attacker getting PW which should not reveal PW as long as H is one-way, which is a consequence of collision-resistance. Problem: The password will be found by an attacker who compromises the server. But we will revisit this when we consider dictionary attacks! These types of server compromises are common and often in the news: This is how client authentication is done on the Internet, for example login Yahoo, Equifax, ... to gmail.com . Mihir Bellare UCSD 27 Mihir Bellare UCSD 28
Recommend
More recommend
Explore More Topics
Stay informed with curated content and fresh updates.