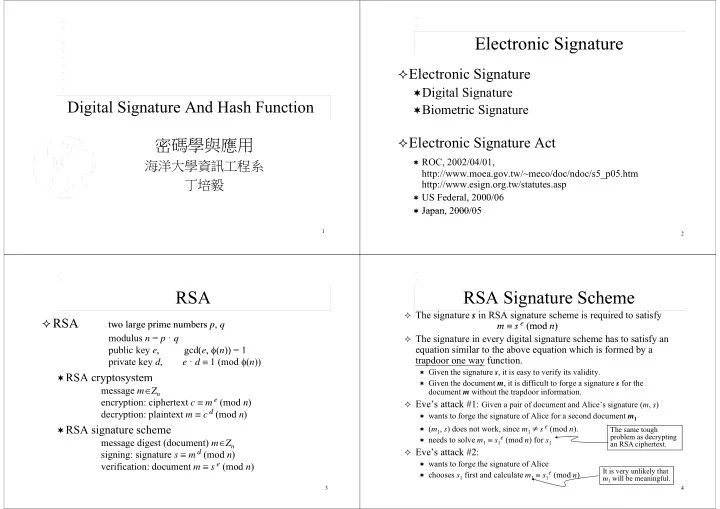
Digital Signature And Hash Function 密碼學與應用
海洋大學資訊工程系 丁培毅 丁培毅
1
Electronic Signature Electronic Signature
El
t i Si t
Electronic Signature
Digital Signature Biometric Signature
Electronic Signature Act
ROC, 2002/04/01,
http://www.moea.gov.tw/~meco/doc/ndoc/s5_p05.htm http://www esign org tw/statutes asp http://www.esign.org.tw/statutes.asp
US Federal, 2000/06 Japan 2000/05
2
Japan, 2000/05
RSA RSA
RSA
two large prime numbers p q
RSA
two large prime numbers p, q modulus n = p ꞏ q public key e, gcd(e, (n)) = 1 p y , g ( , ( )) private key d, e ꞏ d 1 (mod (n))
RSA cryptosystem
S yp y
message mZn encryption: ciphertext c m e (mod n)
d
decryption: plaintext m c d (mod n)
RSA signature scheme
message digest (document) mZn signing: signature s m d (mod n) ifi ti d t
e (
d )
3
verification: document m s e (mod n)
RSA Signature Scheme RSA Signature Scheme
The signature s in RSA signature scheme is required to satisfy
m s e (mod n) m s (mod n)
The signature in every digital signature scheme has to satisfy an
equation similar to the above equation which is formed by a q q y trapdoor one way function.
Given the signature s, it is easy to verify its validity. Gi
th d t it i diffi lt t f i t f th
Given the document m, it is difficult to forge a signature s for the
document m without the trapdoor information. Eve’s attack #1: Given a pair of document and Alice’s signature (m, s)
wants to forge the signature of Alice for a second document m1 (m1, s) does not work, since m1 s e (mod n).
d l
e (
d ) f
The same tough problem as decrypting
needs to solve m1 s1e (mod n) for s1
Eve’s attack #2:
wants to forge the signature of Alice
problem as decrypting an RSA ciphertext.
4
wants to forge the signature of Alice chooses s1 first and calculate m1 s1e (mod n)
It is very unlikely that m1 will be meaningful.