CS 251 Fall 2019 Principles of Programming Languages
Ben Wood
λ
CS 240 Spring 2020
Foundations of Computer Systems
Ben Wood https://cs.wellesley.edu/~cs240/s20/
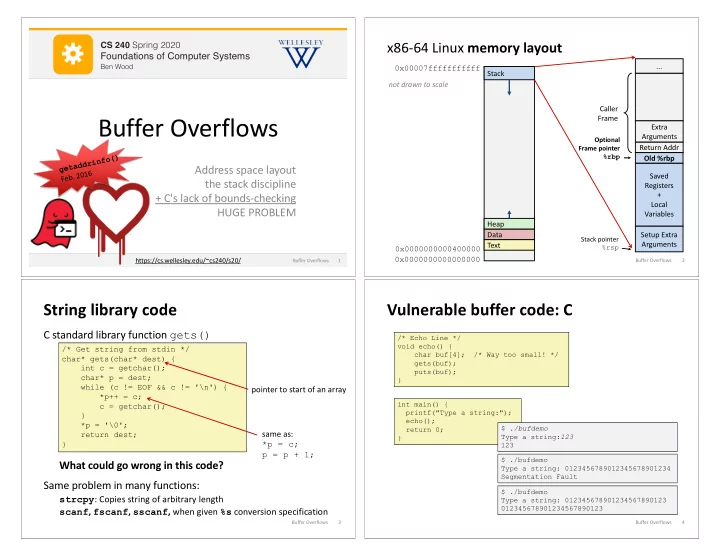
Buffer Overflows
Address space layout the stack discipline + C's lack of bounds-checking HUGE PROBLEM
g e t a d d r i n f
- (
) F e b . 2 1 6
Buffer Overflows 1
x86-64 Linux memory layout
2
0x00007fffffffffff 0x0000000000000000 Stack Text Data Heap 0x0000000000400000 not drawn to scale Return Addr Saved Registers + Local Variables Setup Extra Arguments Old %rbp Extra Arguments Caller Frame
Optional Frame pointer %rbp Stack pointer %rsp
... ...
Buffer Overflows
String library code
C standard library function gets() What could go wrong in this code? Same problem in many functions:
strcpy: Copies string of arbitrary length scanf, fscanf, sscanf, when given %s conversion specification
3
/* Get string from stdin */ char* gets(char* dest) { int c = getchar(); char* p = dest; while (c != EOF && c != '\n') { *p++ = c; c = getchar(); } *p = '\0'; return dest; }
pointer to start of an array same as: *p = c; p = p + 1;
Buffer Overflows
Vulnerable buffer code: C
4
int main() { printf("Type a string:"); echo(); return 0; } /* Echo Line */ void echo() { char buf[4]; /* Way too small! */ gets(buf); puts(buf); } $ ./bufdemo Type a string:123 123 $ ./bufdemo Type a string: 0123456789012345678901234 Segmentation Fault $ ./bufdemo Type a string: 012345678901234567890123 012345678901234567890123
Buffer Overflows