x86-32 and x86-64 Assembly (Part 2) (I know Kung-Fu !) Emmanuel - PowerPoint PPT Presentation
x86-32 and x86-64 Assembly (Part 2) (I know Kung-Fu !) Emmanuel Fleury <emmanuel.fleury@u-bordeaux.fr> LaBRI, Universit de Bordeaux, France October 8, 2019 Emmanuel Fleury (LaBRI, France) x86-32 and x86-64 Assembly (Part 2) October
x86-32 and x86-64 Assembly (Part 2) (I know Kung-Fu !) Emmanuel Fleury <emmanuel.fleury@u-bordeaux.fr> LaBRI, Université de Bordeaux, France October 8, 2019 Emmanuel Fleury (LaBRI, France) x86-32 and x86-64 Assembly (Part 2) October 8, 2019 1 / 32
Overview Stack Management 1 Application Binary Interfaces 2 References 3 Emmanuel Fleury (LaBRI, France) x86-32 and x86-64 Assembly (Part 2) October 8, 2019 2 / 32
Overview Stack Management 1 Application Binary Interfaces 2 References 3 Emmanuel Fleury (LaBRI, France) x86-32 and x86-64 Assembly (Part 2) October 8, 2019 3 / 32
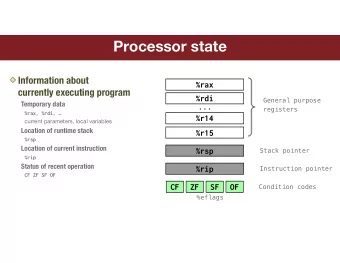
Program Overview Highest Address argument2 argument1 Stack Registers –––––––––––- var1 var2 SP (Stack Pointer) ; SP PC (Program Counter) ; var3 PC Heap var4 GPR (General Purpose Register) . var5 GPR0 var6 Address-space Data var7 GPR1 var8 Stack GPR2 Heap main() Registers instr1 Data Code instr2 foo() Code ... Lowest Address Address-space Emmanuel Fleury (LaBRI, France) x86-32 and x86-64 Assembly (Part 2) October 8, 2019 4 / 32
Program Overview Highest Address argument2 argument1 Stack Registers –––––––––––- var1 var2 SP (Stack Pointer) ; SP PC (Program Counter) ; var3 PC Heap var4 GPR (General Purpose Register) . var5 GPR0 var6 Address-space Data var7 GPR1 var8 Stack GPR2 Heap main() Registers instr1 Data Code instr2 foo() Code ... Lowest Address Address-space Emmanuel Fleury (LaBRI, France) x86-32 and x86-64 Assembly (Part 2) October 8, 2019 4 / 32
Stack Instructions Managing Stack Data Mnemonic Operand Operation push src Push the content of ’src’ on the stack dst Pop the content from the stack to ’dst’ pop Managing Stack Frames Mnemonic Operation enter Create a new stack-frame Restore the previous stack-frame leave Managing Call Stack Mnemonic Operand Operation call addr Save eip and jump to a function at ’addr’ – Restore saved eip and return from a function ret Emmanuel Fleury (LaBRI, France) x86-32 and x86-64 Assembly (Part 2) October 8, 2019 5 / 32
Stack (Basic Principle) L ast I n F irst O ut ( LIFO ) Only two operations: push 17 Push an item on the stack. 6 pop 11 Pop an item from the stack. 21 Emmanuel Fleury (LaBRI, France) x86-32 and x86-64 Assembly (Part 2) October 8, 2019 6 / 32
Stack (Basic Principle) 34 L ast I n F irst O ut ( LIFO ) Only two operations: push 17 Push an item on the stack. 6 pop 11 Pop an item from the stack. 21 Emmanuel Fleury (LaBRI, France) x86-32 and x86-64 Assembly (Part 2) October 8, 2019 6 / 32
Stack (Basic Principle) 34 L ast I n F irst O ut ( LIFO ) push Only two operations: 34 push 17 Push an item on the stack. 6 pop 11 Pop an item from the stack. 21 Emmanuel Fleury (LaBRI, France) x86-32 and x86-64 Assembly (Part 2) October 8, 2019 6 / 32
Stack (Basic Principle) L ast I n F irst O ut ( LIFO ) Only two operations: 34 push 17 Push an item on the stack. 6 pop 11 Pop an item from the stack. 21 Emmanuel Fleury (LaBRI, France) x86-32 and x86-64 Assembly (Part 2) October 8, 2019 6 / 32
Stack (Basic Principle) 34 L ast I n F irst O ut ( LIFO ) pop Only two operations: 34 push 17 Push an item on the stack. 6 pop 11 Pop an item from the stack. 21 Emmanuel Fleury (LaBRI, France) x86-32 and x86-64 Assembly (Part 2) October 8, 2019 6 / 32
Stack (Basic Principle) 34 L ast I n F irst O ut ( LIFO ) Only two operations: push 17 Push an item on the stack. 6 pop 11 Pop an item from the stack. 21 Emmanuel Fleury (LaBRI, France) x86-32 and x86-64 Assembly (Part 2) October 8, 2019 6 / 32
Stack (In Memory) Higher Memory Memory area is managed as a stack. Bottom of Addresses the Stack It grows toward lower addresses. 0x145fea 0xffd4b8 Register esp (stack-pointer) contains: Address of the stack’s top element. 0x6970db 0xffd4b4 Lowest address of the memory area. 0xffd474 0xffd4b0 esp 0xffd3c8 0xffd4ac 0xffd4a8 Top of Lower Memory the Stack Addresses Emmanuel Fleury (LaBRI, France) x86-32 and x86-64 Assembly (Part 2) October 8, 2019 7 / 32
push Higher Memory push <src> Bottom of Addresses the Stack Actions performed: 0x145fea 0xffd4b8 1 Fetch operand from src ; 2 esp = esp-4 (32 bits) 0x6970db 0xffd4b4 esp = esp-8 (64 bits); 0xffd474 0xffd4b0 3 Write operand to (esp) . esp 0xffd3c8 0xffd4ac src 0x804842 0xffd4a8 Top of Lower Memory the Stack Addresses Emmanuel Fleury (LaBRI, France) x86-32 and x86-64 Assembly (Part 2) October 8, 2019 8 / 32
push Higher Memory push <src> Bottom of Addresses the Stack Actions performed: 0x145fea 0xffd4b8 1 Fetch operand from src ; 2 esp = esp-4 (32 bits) 0x6970db 0xffd4b4 esp = esp-8 (64 bits); 0xffd474 0xffd4b0 3 Write operand to (esp) . esp 0xffd3c8 0xffd4ac src push 0x804842 0xffd4a8 Top of Lower Memory the Stack Addresses Emmanuel Fleury (LaBRI, France) x86-32 and x86-64 Assembly (Part 2) October 8, 2019 8 / 32
push Higher Memory push <src> Bottom of Addresses the Stack Actions performed: 0x145fea 0xffd4b8 1 Fetch operand from src ; 2 esp = esp-4 (32 bits) 0x6970db 0xffd4b4 esp = esp-8 (64 bits); 0xffd474 0xffd4b0 3 Write operand to (esp) . esp 0xffd3c8 0xffd4ac src push − 4 0x804842 0xffd4a8 Top of Lower Memory the Stack Addresses Emmanuel Fleury (LaBRI, France) x86-32 and x86-64 Assembly (Part 2) October 8, 2019 8 / 32
push Higher Memory push <src> Bottom of Addresses the Stack Actions performed: 0x145fea 0xffd4b8 1 Fetch operand from src ; 2 esp = esp-4 (32 bits) 0x6970db 0xffd4b4 esp = esp-8 (64 bits); 0xffd474 0xffd4b0 3 Write operand to (esp) . 0xffd3c8 0xffd4ac src push − 4 esp 0x804842 0xffd4a8 Top of Lower Memory the Stack Addresses Emmanuel Fleury (LaBRI, France) x86-32 and x86-64 Assembly (Part 2) October 8, 2019 8 / 32
push Higher Memory push <src> Bottom of Addresses the Stack Actions performed: 0x145fea 0xffd4b8 1 Fetch operand from src ; 2 esp = esp-4 (32 bits) 0x6970db 0xffd4b4 esp = esp-8 (64 bits); 0xffd474 0xffd4b0 3 Write operand to (esp) . 0xffd3c8 0xffd4ac src push esp 0x804842 0x804842 0xffd4a8 Top of Lower Memory the Stack Addresses Emmanuel Fleury (LaBRI, France) x86-32 and x86-64 Assembly (Part 2) October 8, 2019 8 / 32
push Higher Memory push <src> Bottom of Addresses the Stack Actions performed: 0x145fea 0xffd4b8 1 Fetch operand from src ; 2 esp = esp-4 (32 bits) 0x6970db 0xffd4b4 esp = esp-8 (64 bits); 0xffd474 0xffd4b0 3 Write operand to (esp) . 0xffd3c8 0xffd4ac esp 0x804842 0xffd4a8 Top of Lower Memory the Stack Addresses Emmanuel Fleury (LaBRI, France) x86-32 and x86-64 Assembly (Part 2) October 8, 2019 8 / 32
pop Higher Memory pop <dst> Bottom of Addresses the Stack Actions performed: 0x145fea 0xffd4b8 1 Fetch operand from esp ; 2 Write operand to dst . 0x6970db 0xffd4b4 3 esp = esp+4 (32 bits) 0xffd474 0xffd4b0 esp = esp+8 (64 bits); 0xffd3c8 0xffd4ac esp 0x804842 0xffd4a8 Top of Lower Memory the Stack Addresses Emmanuel Fleury (LaBRI, France) x86-32 and x86-64 Assembly (Part 2) October 8, 2019 9 / 32
pop Higher Memory pop <dst> Bottom of Addresses the Stack Actions performed: 0x145fea 0xffd4b8 1 Fetch operand from esp ; 2 Write operand to dst . 0x6970db 0xffd4b4 3 esp = esp+4 (32 bits) 0xffd474 0xffd4b0 esp = esp+8 (64 bits); 0xffd3c8 0xffd4ac pop esp 0x804842 0xffd4a8 Top of Lower Memory the Stack Addresses Emmanuel Fleury (LaBRI, France) x86-32 and x86-64 Assembly (Part 2) October 8, 2019 9 / 32
pop Higher Memory pop <dst> Bottom of Addresses the Stack Actions performed: 0x145fea 0xffd4b8 1 Fetch operand from esp ; 2 Write operand to dst . 0x6970db 0xffd4b4 3 esp = esp+4 (32 bits) 0xffd474 0xffd4b0 esp = esp+8 (64 bits); 0xffd3c8 0xffd4ac dst pop esp 0x804842 0x804842 0xffd4a8 Top of Lower Memory the Stack Addresses Emmanuel Fleury (LaBRI, France) x86-32 and x86-64 Assembly (Part 2) October 8, 2019 9 / 32
pop Higher Memory pop <dst> Bottom of Addresses the Stack Actions performed: 0x145fea 0xffd4b8 1 Fetch operand from esp ; 2 Write operand to dst . 0x6970db 0xffd4b4 3 esp = esp+4 (32 bits) 0xffd474 0xffd4b0 esp = esp+8 (64 bits); 0xffd3c8 0xffd4ac dst pop + 4 esp 0x804842 0x804842 0xffd4a8 Top of Lower Memory the Stack Addresses Emmanuel Fleury (LaBRI, France) x86-32 and x86-64 Assembly (Part 2) October 8, 2019 9 / 32
pop Higher Memory pop <dst> Bottom of Addresses the Stack Actions performed: 0x145fea 0xffd4b8 1 Fetch operand from esp ; 2 Write operand to dst . 0x6970db 0xffd4b4 3 esp = esp+4 (32 bits) 0xffd474 0xffd4b0 esp = esp+8 (64 bits); esp 0xffd3c8 0xffd4ac dst pop + 4 0x804842 0x804842 0xffd4a8 Top of Lower Memory the Stack Addresses Emmanuel Fleury (LaBRI, France) x86-32 and x86-64 Assembly (Part 2) October 8, 2019 9 / 32
pop Higher Memory pop <dst> Bottom of Addresses the Stack Actions performed: 0x145fea 0xffd4b8 1 Fetch operand from esp ; 2 Write operand to dst . 0x6970db 0xffd4b4 3 esp = esp+4 (32 bits) 0xffd474 0xffd4b0 esp = esp+8 (64 bits); esp 0xffd3c8 0xffd4ac dst 0x804842 0x804842 0xffd4a8 Top of Lower Memory the Stack Addresses Emmanuel Fleury (LaBRI, France) x86-32 and x86-64 Assembly (Part 2) October 8, 2019 9 / 32
Recommend
More recommend
Explore More Topics
Stay informed with curated content and fresh updates.