SLIDE 1
1
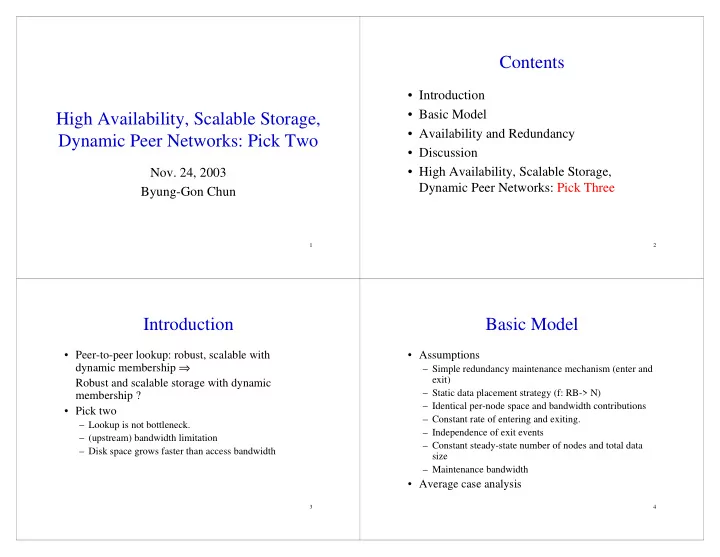
High Availability, Scalable Storage, Dynamic Peer Networks: Pick Two
- Nov. 24, 2003
Byung-Gon Chun
2
Contents
- Introduction
- Basic Model
- Availability and Redundancy
- Discussion
- High Availability, Scalable Storage,
Dynamic Peer Networks: Pick Three
3
Introduction
- Peer-to-peer lookup: robust, scalable with
dynamic membership ⇒ Robust and scalable storage with dynamic membership ?
- Pick two
– Lookup is not bottleneck. – (upstream) bandwidth limitation – Disk space grows faster than access bandwidth
4
Basic Model
- Assumptions
– Simple redundancy maintenance mechanism (enter and exit) – Static data placement strategy (f: RB-> N) – Identical per-node space and bandwidth contributions – Constant rate of entering and exiting. – Independence of exit events – Constant steady-state number of nodes and total data size – Maintenance bandwidth
- Average case analysis