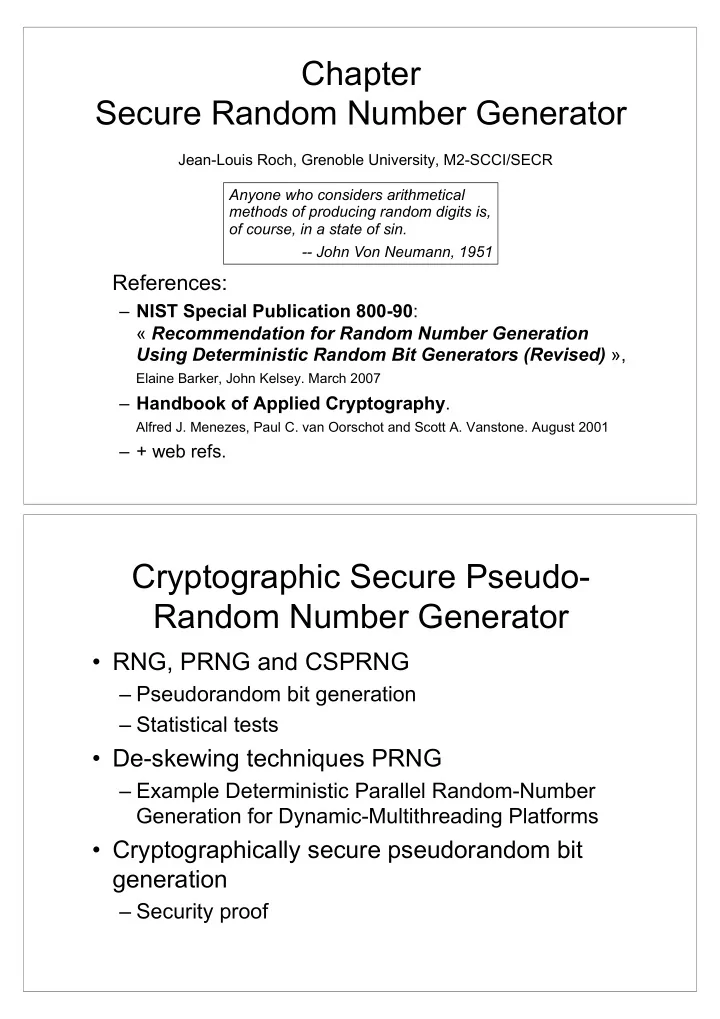
Chapter Secure Random Number Generator Jean-Louis Roch, Grenoble University, M2-SCCI/SECR
References:
– NIST Special Publication 800-90: « Recommendation for Random Number Generation Using Deterministic Random Bit Generators (Revised) »,
Elaine Barker, John Kelsey. March 2007
– Handbook of Applied Cryptography.
Alfred J. Menezes, Paul C. van Oorschot and Scott A. Vanstone. August 2001
– + web refs.
Anyone who considers arithmetical methods of producing random digits is,
- f course, in a state of sin.
- - John Von Neumann, 1951
Cryptographic Secure Pseudo- Random Number Generator
- RNG, PRNG and CSPRNG
– Pseudorandom bit generation – Statistical tests
- De-skewing techniques PRNG
– Example Deterministic Parallel Random-Number Generation for Dynamic-Multithreading Platforms
- Cryptographically secure pseudorandom bit