1 Hofstra University - CSC005 11/29/06
Chapter 15
Networks – Part 2
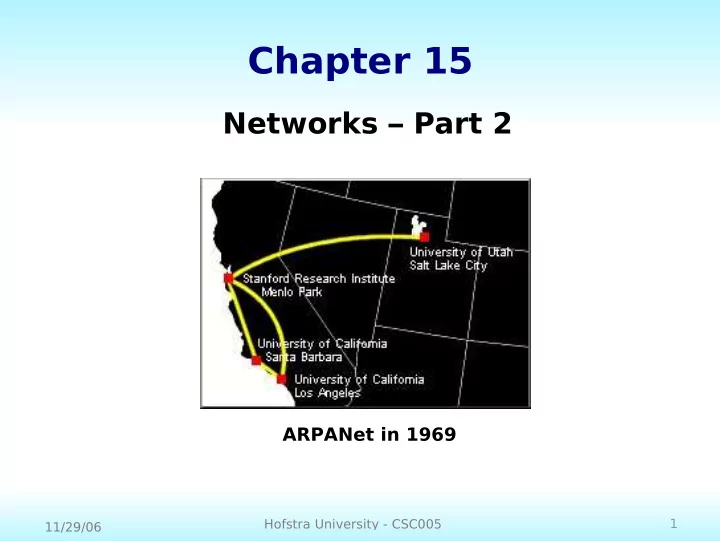
ARPANet in 1969
Chapter 15 Networks Part 2 ARPANet in 1969 1 Hofstra University - - PowerPoint PPT Presentation
Chapter 15 Networks Part 2 ARPANet in 1969 1 Hofstra University - CSC005 11/29/06 Internet Standards and RFCs Internet Architecture Board (IAB) - overall architecture Internet Engineering Task Force (IETF) - engineering and development
1 Hofstra University - CSC005 11/29/06
ARPANet in 1969
2 Hofstra University - CSC005 11/29/06
3 Hofstra University - CSC005 11/29/06
4 Hofstra University - CSC005 11/29/06
5 Hofstra University - CSC005 11/29/06
Internet draft Experimental Informational Proposed standard Draft standard Internet standard Historic IETF IESG < 6 months > 6 months > 4 months two independent implementations
6 Hofstra University - CSC005 11/29/06
7 Hofstra University - CSC005 11/29/06
8 Hofstra University - CSC005 11/29/06
9 Hofstra University - CSC005 11/29/06
10 Hofstra University - CSC005 11/29/06
11 Hofstra University - CSC005 11/29/06
12 Hofstra University - CSC005 11/29/06
13 Hofstra University - CSC005 11/29/06
14 Hofstra University - CSC005 11/29/06
15 Hofstra University - CSC005 11/29/06
16 Hofstra University - CSC005 11/29/06
TCP Header User Data IP Header User Data Network Header User Data User Data Application Byte Stream TCP Segment IP Datagram Network-level Packet
17 Hofstra University - CSC005 11/29/06
18 Hofstra University - CSC005 11/29/06
19 Hofstra University - CSC005 11/29/06
128-bit field 32-bit field QoS max # allowable hops
20 Hofstra University - CSC005 11/29/06
21 Hofstra University - CSC005 11/29/06
22 Hofstra University - CSC005 11/29/06
23 Hofstra University - CSC005 11/29/06
24 Hofstra University - CSC005 11/29/06
25 Hofstra University - CSC005 11/29/06
26 Hofstra University - CSC005 11/29/06
cookie is captured getting a quote business.nytimes.com dns query ACK
27 Hofstra University - CSC005 11/29/06
28 Hofstra University - CSC005 11/29/06
29 Hofstra University - CSC005 11/29/06
30 Hofstra University - CSC005 11/29/06
31 Hofstra University - CSC005 11/29/06
32 Hofstra University - CSC005 11/29/06
33 Hofstra University - CSC005 11/29/06
34 Hofstra University - CSC005 11/29/06
35 Hofstra University - CSC005 11/29/06
36 Hofstra University - CSC005 11/29/06
37 Hofstra University - CSC005 11/29/06
38 Hofstra University - CSC005 11/29/06
39 Hofstra University - CSC005 11/29/06
Figure 15.8 A firewall protecting a LAN
40 Hofstra University - CSC005 11/29/06
41 Hofstra University - CSC005 11/29/06
42 Hofstra University - CSC005 11/29/06
43 Hofstra University - CSC005 11/29/06
44 Hofstra University - CSC005 11/29/06
45 Hofstra University - CSC005 11/29/06
(NB: This is not an endorsement of any product)
46 Hofstra University - CSC005 11/29/06
47 Hofstra University - CSC005 11/29/06
48 Hofstra University - CSC005 11/29/06
49 Hofstra University - CSC005 11/29/06
50 Hofstra University - CSC005 11/29/06
51 Hofstra University - CSC005 11/29/06
52 Hofstra University - CSC005 11/29/06
53 Hofstra University - CSC005 11/29/06
54 Hofstra University - CSC005 11/29/06
“The City” At 1200 Feet In December