3/27/2013shankar
- authenticationslide1
- ComputerandNetworkSecurity
CMSC414
- AUTHENTICATION
- UdayaShankar
shankar@cs.umd.edu
- 3/27/2013shankar
- authenticationslide2
AuthenticationOverview(NSchapter9)
- Largesetofprincipalsattachedtoanopenchannel(eg,Internet).
- Eachprincipalrepeatedly
- attemptstoinitiateaconnection(i.e.,session)withaspecifiedprincipal
- uponsuccessfulconnectionestablishment,exchangesmessages
- closestheconnection
- waitsforanarbitrary(butbounded)time
- WhenaprincipalAassumesitisconnectedtoaprincipalB,
AisindeedexchangingmessageswithB,andnotsomeattackerC.
- WhenprincipalAassumesconfidentiality/integrityofthemessageexchange,
thisisindeedthecase.
- Programscanusesecrets(eg,fromspaceof2128)
- Humanprincipalsarerestrictedtosecrets(eg,spaceof232)
andcannotdocryptographicoperations.
- WhenwesayaprogramprincipalAitisconnectedtoB,
wemeanthatA’sprogram’svariablesindicatethatAisconnectedtoB.
3/27/2013shankar
- authenticationslide3
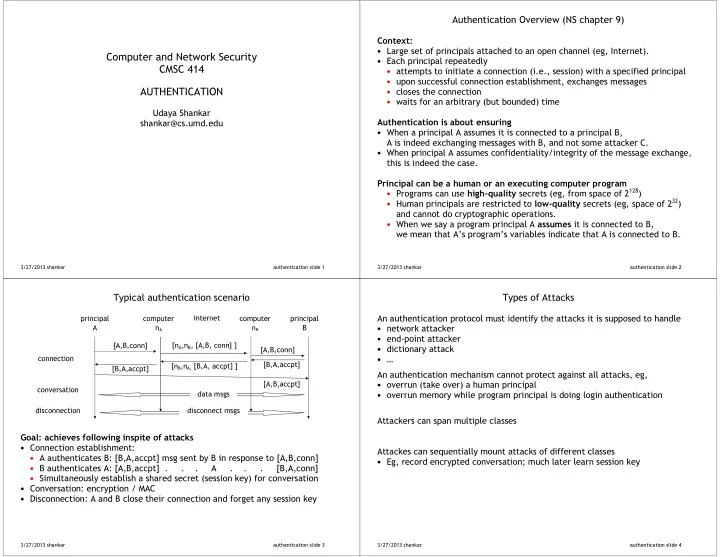
Typicalauthenticationscenario
- Connectionestablishment:
- AauthenticatesB:[B,A,accpt]msgsentbyBinresponseto[A,B,conn]
- BauthenticatesA:[A,B,accpt]...A...[B,A,conn]
- Simultaneouslyestablishasharedsecret(sessionkey)forconversation
- Conversation:encryption/MAC
- Disconnection:AandBclosetheirconnectionandforgetanysessionkey
- connection
conversation disconnection [nB,nA,[B,A,accpt]] [B,A,accpt] datamsgs disconnectmsgs computer nB Internet computer nA principal A [B,A,accpt] [nA,nB,[A,B,conn]] [A,B,conn] [A,B,conn] principal B [A,B,accpt]
3/27/2013shankar
- authenticationslide4
TypesofAttacks
- Anauthenticationprotocolmustidentifytheattacksitissupposedtohandle
- networkattacker
- end;pointattacker
- dictionaryattack
- …
Anauthenticationmechanismcannotprotectagainstallattacks,eg,
- overrun(takeover)ahumanprincipal
- overrunmemorywhileprogramprincipalisdoingloginauthentication
- Attackerscanspanmultipleclasses
- Attackescansequentiallymountattacksofdifferentclasses
- Eg,recordencryptedconversation;muchlaterlearnsessionkey