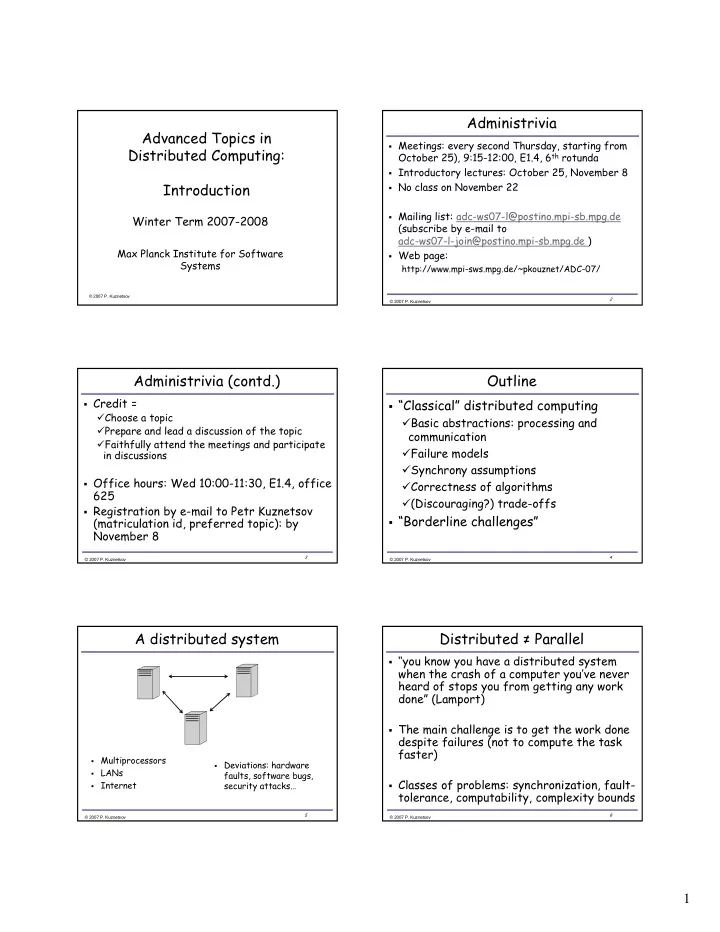
SLIDE 1
1 AdvancedTopicsin DistributedComputing: Introduction
WinterTerm20072008
MaxPlanckInstituteforSoftware Systems
- Administrivia
Meetings:everysecondThursday,startingfrom
October25),9:1512:00,E1.4,6th rotunda
Introductorylectures:October25,November8 NoclassonNovember22 Mailinglist:adcws07l@postino.mpisb.mpg.de
(subscribebyemailto adcws07ljoin@postino.mpisb.mpg.de)
Webpage:
http://www.mpisws.mpg.de/~pkouznet/ADC07/
- Administrivia (contd.)
Credit=
Chooseatopic Prepareandleadadiscussionofthetopic Faithfullyattendthemeetingsandparticipate indiscussions
Officehours:Wed10:0011:30,E1.4,office
625
RegistrationbyemailtoPetrKuznetsov
(matriculationid,preferredtopic):by November8
- Outline
“Classical” distributedcomputing
Basicabstractions:processingand communication Failuremodels Synchronyassumptions Correctnessofalgorithms (Discouraging?)tradeoffs
“Borderlinechallenges”
- Adistributedsystem
Multiprocessors LANs Internet Deviations:hardware
faults,softwarebugs, securityattacks…
- Distributed≠ Parallel