@HISA_HIC #HIC18
Mr Laurie Joyce
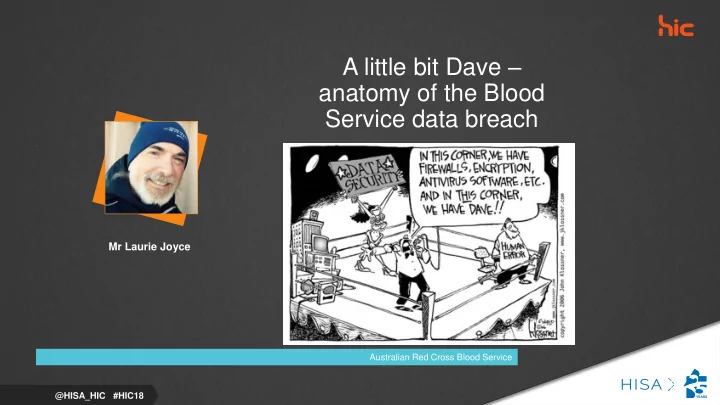
A little bit Dave – anatomy of the Blood Service data breach
Australian Red Cross Blood Service
A little bit Dave anatomy of the Blood Service data breach Mr - - PowerPoint PPT Presentation
A little bit Dave anatomy of the Blood Service data breach Mr Laurie Joyce Australian Red Cross Blood Service @HISA_HIC #HIC18 Blood Service Data Breach Laurie Joyce IT Security and Compliance Manager Headlines Introduction In
@HISA_HIC #HIC18
Mr Laurie Joyce
Australian Red Cross Blood Service
What happened How we responded to the incident The reviews undertaken How we responded to the need to rapidly improve our Information
The Australian Red Cross Blood Service is entrusted with the supply of Australia’s
1.3 million blood donations annually 500,000 active donors 3500 staff 80+ facilities Federal Government Critical Infrastructure Classification
A second war room was also quickly established consisting of the Chief Executive, other relevant department Executive Directors and SMES from legal, government relations and communications.
Board was briefed.
Our governing body the National Blood Authority was notified
Government was also briefed including Health Minister and Prime Ministers Department.
Throughout the day the investigation and analysis continued.
We were in contact with the person who found it via a third party.
File was created on 5th September by a vendor staff member and dropped on the file server that day. So had been exposed for roughly 6 weeks
Forensic analysis of the server and the file showed it was touched 4 times and we could account for all of them
Day 2
Database rebuilt
Independent risk assessment on the nature of the information exposed found that there was a “low risk of future direct misuse”
Communications Plan established
Day 3
Midday Press Conference
SMS and emails released Day 4 +
3000 responses required to enquiries come Saturday morning
Formulation of a broader security review was underway
External – websites outside IT control
Internal – detect and monitor capability uplift
Data – where is it and who has it
Governance – policy and procedure review
Impact on BAU activities and resources
Program of works defined
Acquired extra staff
Extreme & High Priority ICT Items – Mitigation Status
Time Period 0 - 3 months 4 - 6 months 7 - 12 months 12 - 18 months Total Audit Target 22 13 15 50 Agreed Target 24 12 10 6 52 Completed 24 12 10 5 51
Medium & Low Priority ICT Items – Mitigation Status
Time Period 0 - 3 months 4 - 6 months 7 - 12 months 12 - 18 months Total Audit Target 13 17 27 8 65 Agreed Target 14 6 38 7 65 Completed 14 6 38 3 61
The root cause of the incident was a one-off human error on the part of a Precedent employee. The data breach
Precedent’s contractual obligations to the Blood Service. As such, the Blood Service did not disclose the information in question within the meaning of Australian Privacy Principle (APP) 6.
Furthermore, the Blood Service had in place policies and practices to protect personal information as required by APP 11.1, including documented information security policies and regular staff training. Nevertheless, there were two matters within the Blood Service’s control that were a contributing factor to the data breach and which constituted breaches of the Privacy Act. In particular, it appears that the incident would not have occurred but for:
measures for personal information held for it by the relevant third party contractor, in breach of APP 11.1
a. the Blood Service’s compliance with its Third Party Management
b. the effectiveness of the Policy and Procedure
Maintain a register of vendors who handle Personally Identifiable Information on our behalf of
Includes
Conduct annual Information Security and Privacy assessments of each of them
Develop our Information Security Strategy and Roadmap Complete the delivery of the program to date
Vulnerability management Managed Security Service (MSS) Data Loss Prevention (DLP) Cloud Access Security Broker (CASB) Roll out new endpoint protection Complete the roll out of Windows 10 Ensure all websites behind our Web Application Firewall (WAF) Privileged Access Management
Get control of shadow IT Know what data is stored outside your corporate network Know who has access to it Know what the Privacy Commissioner defines as reasonable steps
Review your Cyber Security Incident Response and Crisis