80% of Code Red 2 Code Red 2 re-re- Code Red 1 and Code Red 2 - - PowerPoint PPT Presentation
80% of Code Red 2 Code Red 2 re-re- Code Red 1 and Code Red 2 - - PowerPoint PPT Presentation
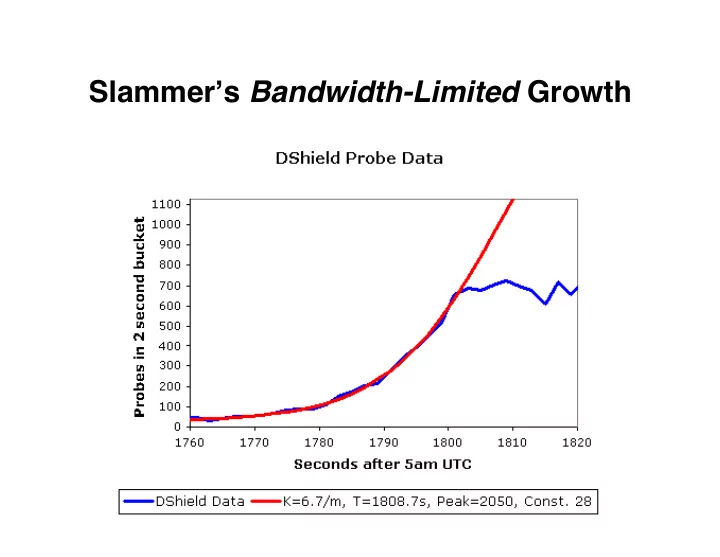
Slammer s Bandwidth-Limited Growth 80% of Code Red 2 Code Red 2 re-re- Code Red 1 and Code Red 2 Code Red 2 re- cleaned up due to released Jan 2004 Nimda endemic dies off released with Oct. onset of Blaster (and 2005; not since
80% of Code Red 2 cleaned up due to
- nset of Blaster
Code Red 2 re- released with Oct. 2003 die-off Code Red 1 and Nimda endemic Code Red 2 re-re- released Jan 2004 (and 2005; not since …?) Code Red 2 dies off again
Code Red 2 re-re- released Jan 2004 (and 2005; not since …?)
Feb 7 2012!
2009 - 2010
2012
2013-2014
Stuxnet: Slowly ramped up centrifuge speeds until they flew apart … … while feeding false readings to control system. Included 4 zero days for spreading
Flame: General information stealer. Includes geolocation from local photos, taking screenshots, microphone access to capture local audio, recording Skype calls, download contacts from nearby BlueTooth devices. Exploited previously unknown MD5 hash collision vulnerability. Built-in autowipe “kill switch”.
Gauss: Specifically targets banking transactions, mainly in Lebanon. Includes trapdoor looking for specific accounts, undeciphered to date.
#!/usr/bin/perl while (<>) { chomp; if ( /^(get|post|options|head|...)(.*)/i ) { # Do not respond if it looks like an exploit last if length > 1000; my $date = gmtime; if ( $1 =~ /get|head/i ) print "HTTP/1.1 200 OK\r\n"; elsif ( $1 =~ /search/i ) print "HTTP/1.1 411 Length Required\r\n"; elsif ( $1 =~ /options/i ) { print "HTTP/1.1 200 OK\r\n"; print "DASL: \r\nDAV: 1, 2\r\n"; print "Public: OPTIONS, TRACE, GET, HEAD, DELETE, ...\r\n"; print "Allow: OPTIONS, TRACE, GET, HEAD, DELETE, ...\r\n"; } elsif ( $1 =~ /propfind/i ) print "HTTP/1.1 207 Multi-Status\r\n"; else print "HTTP/1.1 405 Method Not Allowed\r\n"; } print <<EOF; Server: Microsoft-IIS/5.0 Date: $date GMT Content-Length: 0 Content-Type: text/html Set-Cookie: ASPSESSIONIDACBAABCQ=BHAMAEHAOAIHMOMGJCPFLBGO; path=/ Cache-control: private EOF last; } }
GQ: Building a Large-Scale Honeyfarm
- Honeyfarm: use a network telescope to route scan
traffic to a set of honeypots
- Goal: scale to 100,000s of monitored addresses …
- … at high fidelity
Global Internet
Advertised Dark Space
Physical Honeyfarm Servers
VM VM VM VM VM VM VM VM VM
MGMT Gateway
GRE Tunnels
- r direct routing
GQ: Building a Large-Scale Honeyfarm
- Honeyfarm: use a network telescope to route scan
traffic to a set of honeypots
- Goal: scale to 100,000s of monitored addresses …
- … at high fidelity
Advertised Dark Space
Physical Honeyfarm Servers
VM VM VM VM VM VM VM VM VM
MGMT Gateway
GRE Tunnels
- r direct routing
Dark space: blocks of otherwise unallocated addresses Global Internet
GQ: Building a Large-Scale Honeyfarm
- Honeyfarm: use a network telescope to route scan
traffic to a set of honeypots
- Goal: scale to 100,000s of monitored addresses …
- … at high fidelity
Advertised Dark Space
Physical Honeyfarm Servers
VM VM VM VM VM VM VM VM VM
MGMT Gateway Routers send dark space traffic either via tunnels or direct attachment
GRE Tunnels
- r direct routing
Global Internet
GQ: Building a Large-Scale Honeyfarm
- Honeyfarm: use a network telescope to route scan
traffic to a set of honeypots
- Goal: scale to 100,000s of monitored addresses …
- … at high fidelity
Advertised Dark Space
Physical Honeyfarm Servers
VM VM VM VM VM VM VM VM VM
MGMT Gateway Gateway applies filtering to reduce load, allocates honeypot and mediates communication
GRE Tunnels
- r direct routing
Global Internet
GQ: Building a Large-Scale Honeyfarm
- Honeyfarm: use a network telescope to route scan
traffic to a set of honeypots
- Goal: scale to 100,000s of monitored addresses …
- … at high fidelity
Advertised Dark Space
Physical Honeyfarm Servers
VM VM VM VM VM VM VM VM VM
MGMT Gateway Outbound communication attempted by a honeypot
GRE Tunnels
- r direct routing
Global Internet
GQ: Building a Large-Scale Honeyfarm
- Honeyfarm: use a network telescope to route scan
traffic to a set of honeypots
- Goal: scale to 100,000s of monitored addresses …
- … at high fidelity
Advertised Dark Space
Physical Honeyfarm Servers
VM VM VM VM VM VM VM VM VM
MGMT Gateway Outbound communication attempted by a honeypot can be redirected back to another honeypot
GRE Tunnels
- r direct routing
Global Internet
GQ: Building a Large-Scale Honeyfarm
- Honeyfarm: use a network telescope to route scan
traffic to a set of honeypots
- Goal: scale to 100,000s of monitored addresses …
- … at high fidelity
Advertised Dark Space
Physical Honeyfarm Servers
VM VM VM VM VM VM VM VM VM
MGMT Gateway If redirected traffic again tries to communicate
- utbound, then we have found a worm
GRE Tunnels
- r direct routing
Global Internet
Decryptor
Encrypted Glob of Bits
Key
Jmp ¡
ê
Once running, worm uses an encryptor with a new key to propagate
Decryptor
Main Worm Code
Key
Encryptor
} Decryptor
Different Encrypted Glob of Bits
Key2