1
11/29/2004 1
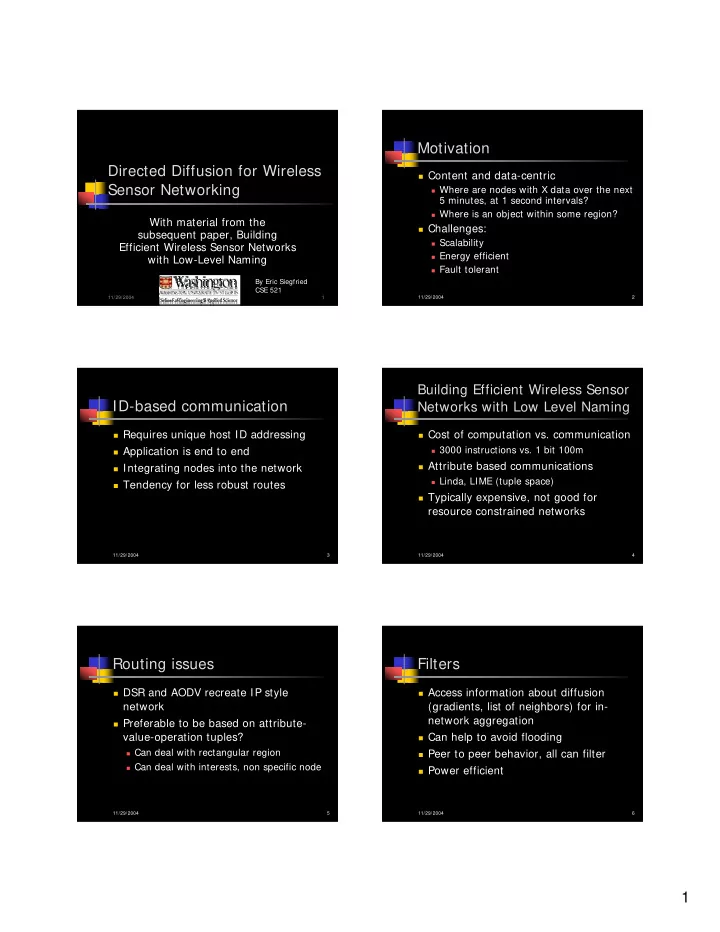
Directed Diffusion for Wireless Sensor Networking
With material from the subsequent paper, Building Efficient Wireless Sensor Networks with Low-Level Naming
By Eric Siegfried CSE 521
11/29/2004 2
Motivation
Content and data-centric
Where are nodes with X data over the next
5 minutes, at 1 second intervals?
Where is an object within some region?
Challenges:
Scalability Energy efficient Fault tolerant
11/29/2004 3
ID-based communication
Requires unique host ID addressing Application is end to end Integrating nodes into the network Tendency for less robust routes
11/29/2004 4
Building Efficient Wireless Sensor Networks with Low Level Naming
Cost of computation vs. communication
3000 instructions vs. 1 bit 100m
Attribute based communications
Linda, LIME (tuple space)
Typically expensive, not good for
resource constrained networks
11/29/2004 5
Routing issues
DSR and AODV recreate IP style
network
Preferable to be based on attribute-
value-operation tuples?
Can deal with rectangular region Can deal with interests, non specific node
11/29/2004 6
Filters
Access information about diffusion
(gradients, list of neighbors) for in- network aggregation
Can help to avoid flooding Peer to peer behavior, all can filter Power efficient