1
Diagnosis using Bounded Search Diagnosis using Bounded Search and Symbolic Inference and Symbolic Inference
Martin Sachenbacher and Brian C. Williams MIT CSAIL
Overview Overview
Soft Constraints Framework Characterizing Structure in Soft Constraints Exploiting Structure in Soft Constraints
– Set-based Search – Decomposition-based Search – Hybrids
Overview Overview
Soft Constraints Framework Characterizing Structure in Soft Constraints Exploiting Structure in Soft Constraints
– Set-based Search – Decomposition-based Search – Hybrids
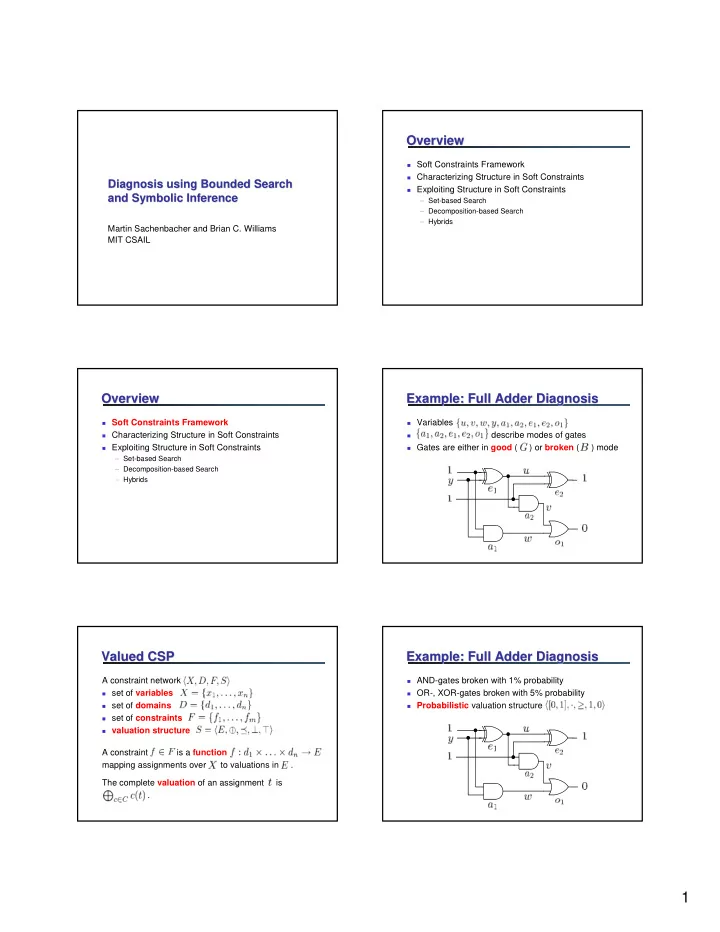
Example: Full Adder Diagnosis Example: Full Adder Diagnosis
Variables
- describe modes of gates
Gates are either in good ( ) or broken ( ) mode
Valued CSP Valued CSP
A constraint network
set of variables set of domains set of constraints valuation structure
A constraint is a function mapping assignments over to valuations in . The complete valuation of an assignment is .
Example: Full Adder Diagnosis Example: Full Adder Diagnosis
AND-gates broken with 1% probability OR-, XOR-gates broken with 5% probability Probabilistic valuation structure