1
Giuseppe Bianchi
Lecture 12. Lecture 12. Introduction to Introduction to IP Routing IP Routing
Giuseppe Bianchi
Why introduction? Why introduction?
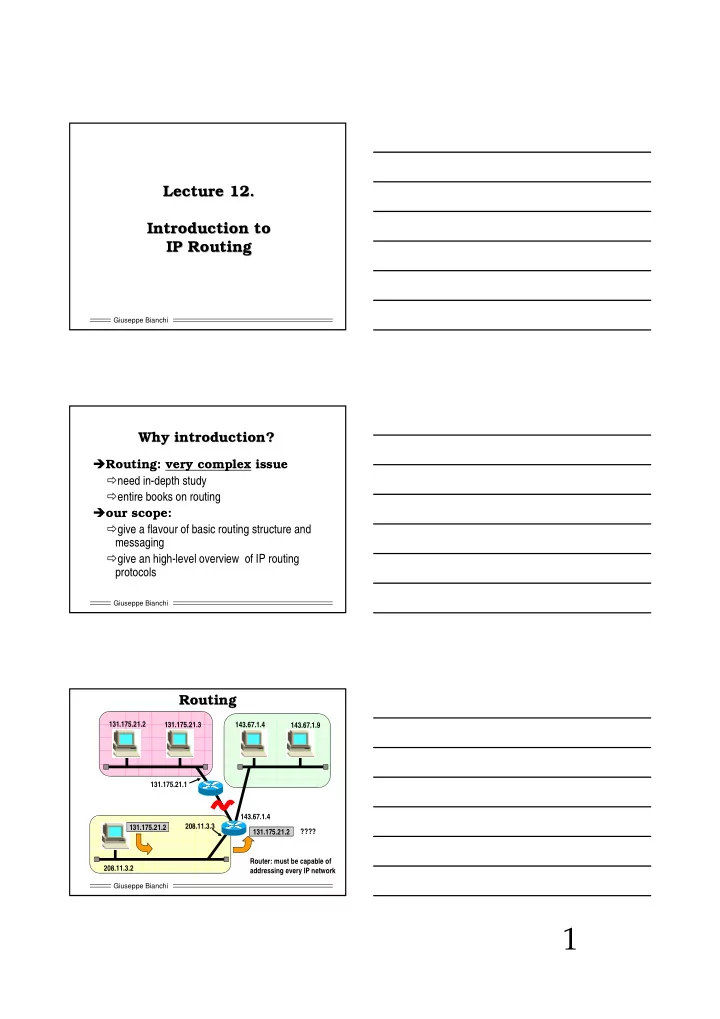
Routing: very complex issue need in-depth study entire books on routing
- ur scope:
give a flavour of basic routing structure and messaging give an high-level overview of IP routing protocols
Giuseppe Bianchi