1
4/10 - 05 Distributed systems - Jonny Pettersson, UmU 1
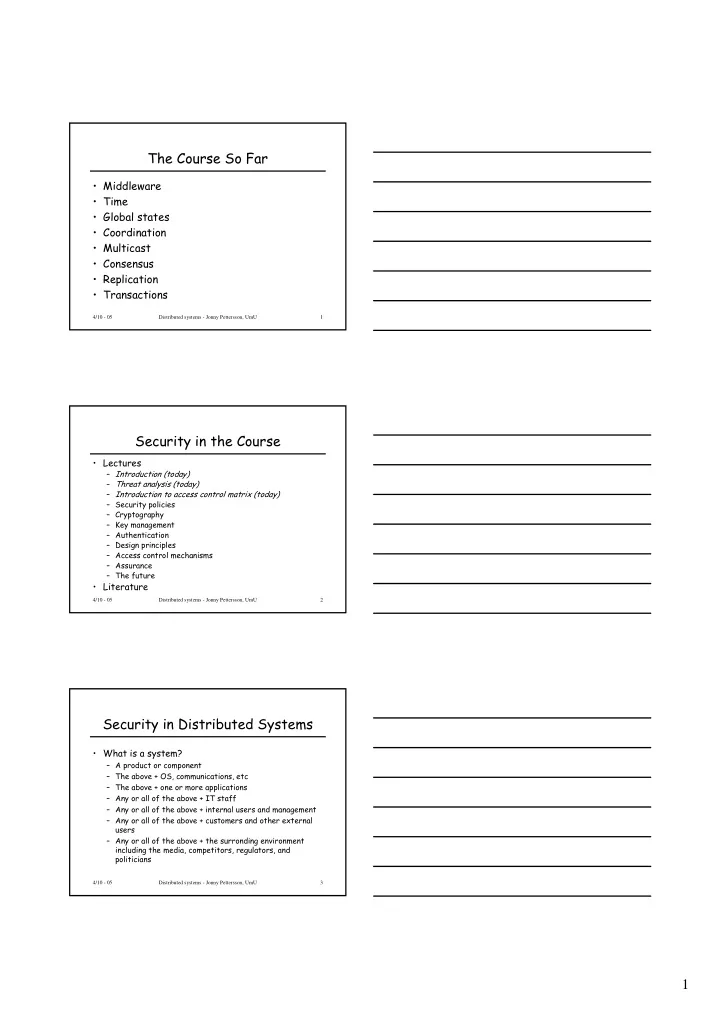
The Course So Far
- Middleware
- Time
- Global states
- Coordination
- Multicast
- Consensus
- Replication
- Transactions
4/10 - 05 Distributed systems - Jonny Pettersson, UmU 2
Security in the Course
- Lectures
– Introduction (today) – Threat analysis (today) – Introduction to access control matrix (today) – Security policies – Cryptography – Key management – Authentication – Design principles – Access control mechanisms – Assurance – The future
- Literature
4/10 - 05 Distributed systems - Jonny Pettersson, UmU 3
Security in Distributed Systems
- What is a system?