Mihir Bellare, UCSD
1
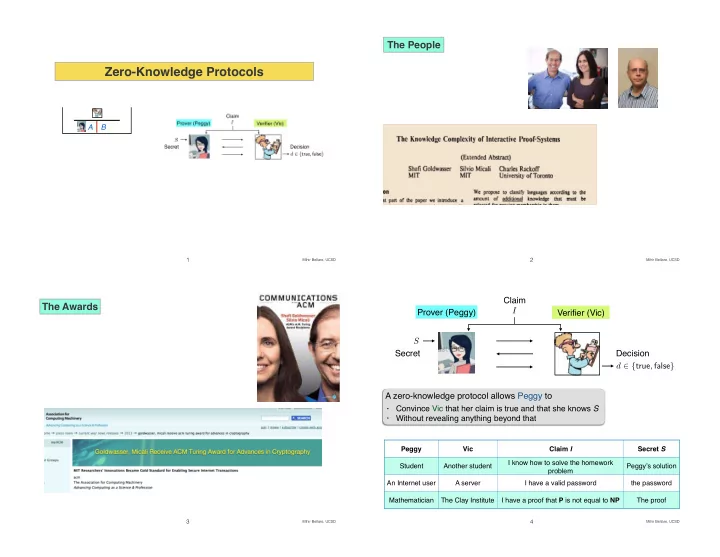
Zero-Knowledge Protocols
A B
Mihir Bellare, UCSD
2
The People
Mihir Bellare, UCSD
3
The Awards
Mihir Bellare, UCSD
4
A zero-knowledge protocol allows Peggy to
- Convince Vic that her claim is true and that she knows S
- Without revealing anything beyond that