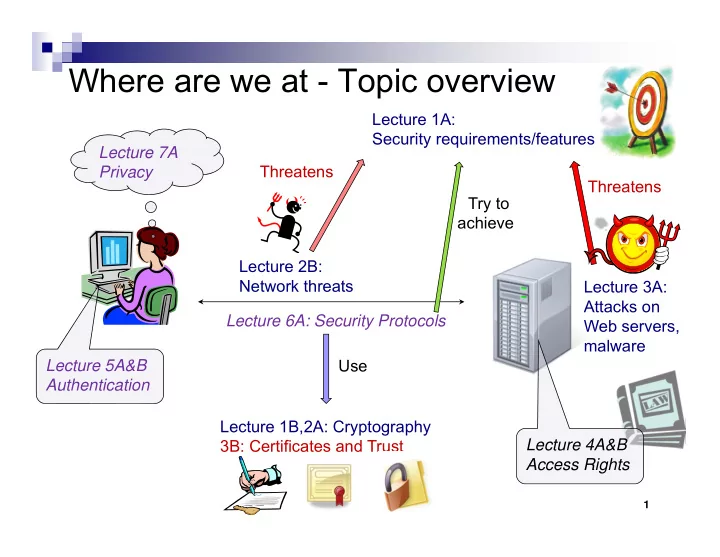
Where are we at - Topic overview
1
Lecture 6A: Security Protocols Lecture 3A: Attacks on Web servers, malware Use Try to achieve Lecture 1A: Security requirements/features Threatens Lecture 1B,2A: Cryptography 3B: Certificates and Trust Lecture 2B: Network threats Threatens Lecture 5A&B Authentication Lecture 7A Privacy Lecture 4A&B Access Rights