2062 IEEE COMMUNICATIONS SURVEYS & TUTORIALS, VOL. 20, NO. 3, THIRD QUARTER 2018
Internet of Things (IoT) Operating Systems Support, Networking Technologies, Applications, and Challenges: A Comparative Review
Farhana Javed, Muhamamd Khalil Afzal, Senior Member, IEEE, Muhammad Sharif, and Byung-Seo Kim , Senior Member, IEEE
Abstract—The Internet of Things (IoT) has become a reality. As the IoT is now becoming a far more common field, the demand for IoT technologies to manage the communication of devices with the rest of the world has increased. The IoT is connect- ing various individual devices called things and wireless sensor networks is also playing an important role. A thing can be defined as an embedded device based on a micro controller that can transmit and receive information. These devices are extremely low in power, memory, and resources. Therefore, the research community has recognized the importance of IoT device operat- ing systems (OSs). An adequate OS with a kernel, networking, real-time capability, and more can make these devices flexible. This review provides a detailed comparison of the OSs designed for IoT devices on the basis of their architecture, scheduling methods, networking technologies, programming models, power and memory management methods, together with other features required for IoT applications. In addition, various applications, challenges, and case studies in the field of IoT research is discussed. Index Terms—Internet of Things, operating system, wireless sensor networks, real-time operating system, IPv6 over low power personal area networks, radio frequency identification.
- I. INTRODUCTION
T
HE INTERNET has changed almost every aspect of
- ur lives: how we work, think, educate, and entertain
- urselves, and now the time has arrived for the Internet of
Things (IoTs). This will connect more devices and impact our lives more than any other aspect of the digital age has done before [1]. IoTs represents the evolution of mobiles, homes and embedded systems. Such an evolution will help to cre- ate a smart world for people because the objects around us will have better knowledge of our likes, wants, and needs.
Manuscript received August 7, 2017; revised December 19, 2017 and February 26, 2018; accepted March 12, 2018. Date of publication March 21, 2018; date of current version August 21, 2018. This work was supported in part by the National Research Foundation of Korea (NRF) grant funded by the Korea Government under Grant 2018R1A2B6002399, and in part by Basic Science Research Program through the NRF funded by the Ministry of Education under Grant 2015R1D1A1A01059186. (Corresponding author: Byung-Seo Kim.)
- F. Javed, M. K. Afzal, and M. Sharif are with the Department of Computer
Science, COMSATS Institute of Information Technology, Islamabad 47040, Pakistan (e-mail: farhana.javed1@gmail.com; khalilafzal@ciitwah.edu.pk; muhammadsharifmalik@yahoo.com). B.-S. Kim is with the Department of Software and Communications Engineering, Hongik University, Sejong 339-701, South Korea (e-mail: snbs@hongik.ac.kr). Digital Object Identifier 10.1109/COMST.2018.2817685
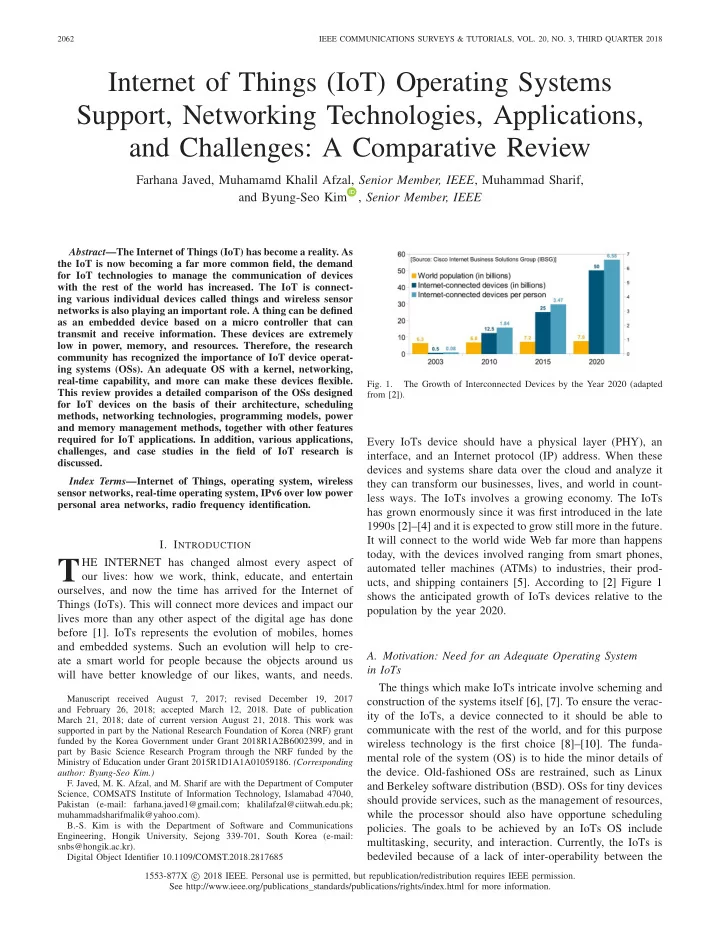
- Fig. 1.
The Growth of Interconnected Devices by the Year 2020 (adapted from [2]).
Every IoTs device should have a physical layer (PHY), an interface, and an Internet protocol (IP) address. When these devices and systems share data over the cloud and analyze it they can transform our businesses, lives, and world in count- less ways. The IoTs involves a growing economy. The IoTs has grown enormously since it was first introduced in the late 1990s [2]–[4] and it is expected to grow still more in the future. It will connect to the world wide Web far more than happens today, with the devices involved ranging from smart phones, automated teller machines (ATMs) to industries, their prod- ucts, and shipping containers [5]. According to [2] Figure 1 shows the anticipated growth of IoTs devices relative to the population by the year 2020.
- A. Motivation: Need for an Adequate Operating System
in IoTs The things which make IoTs intricate involve scheming and construction of the systems itself [6], [7]. To ensure the verac- ity of the IoTs, a device connected to it should be able to communicate with the rest of the world, and for this purpose wireless technology is the first choice [8]–[10]. The funda- mental role of the system (OS) is to hide the minor details of the device. Old-fashioned OSs are restrained, such as Linux and Berkeley software distribution (BSD). OSs for tiny devices should provide services, such as the management of resources, while the processor should also have opportune scheduling
- policies. The goals to be achieved by an IoTs OS include
multitasking, security, and interaction. Currently, the IoTs is bedeviled because of a lack of inter-operability between the
1553-877X c 2018 IEEE. Personal use is permitted, but republication/redistribution requires IEEE permission. See http://www.ieee.org/publications_standards/publications/rights/index.html for more information.