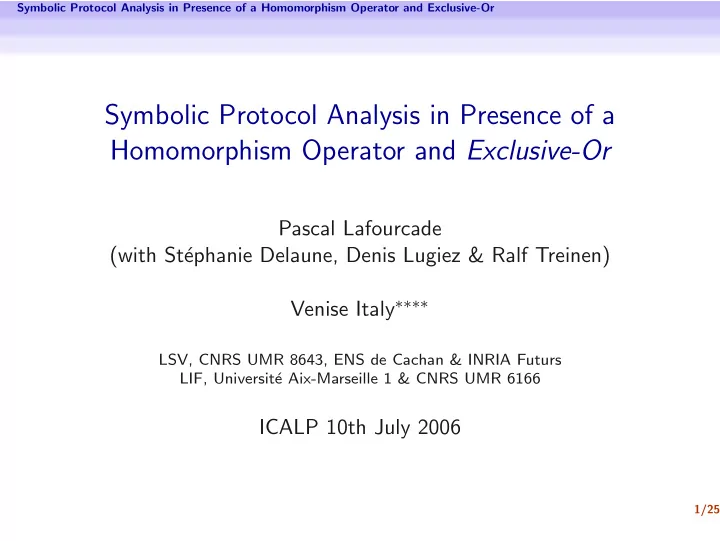
Symbolic Protocol Analysis in Presence of a Homomorphism Operator and - PowerPoint PPT Presentation
Symbolic Protocol Analysis in Presence of a Homomorphism Operator and Exclusive-Or Symbolic Protocol Analysis in Presence of a Homomorphism Operator and Exclusive-Or Pascal Lafourcade (with St ephanie Delaune, Denis Lugiez & Ralf Treinen)
Symbolic Protocol Analysis in Presence of a Homomorphism Operator and Exclusive-Or Symbolic Protocol Analysis in Presence of a Homomorphism Operator and Exclusive-Or Pascal Lafourcade (with St´ ephanie Delaune, Denis Lugiez & Ralf Treinen) Venise Italy ∗∗∗∗ LSV, CNRS UMR 8643, ENS de Cachan & INRIA Futurs LIF, Universit´ e Aix-Marseille 1 & CNRS UMR 6166 ICALP 10th July 2006 1/25
Symbolic Protocol Analysis in Presence of a Homomorphism Operator and Exclusive-Or Motivation Introduction Symbolic approach • Intruder controls the network • Messages represented by terms - { m } k - � m 1 , m 2 � • Number of sessions bounded • Perfect encryption hypothesis 2/25
Symbolic Protocol Analysis in Presence of a Homomorphism Operator and Exclusive-Or Motivation Introduction Symbolic approach • Intruder controls the network • Messages represented by terms - { m } k - � m 1 , m 2 � • Number of sessions bounded • Perfect encryption hypothesis Advantages • Automatic verification • Useful abstraction 2/25
Symbolic Protocol Analysis in Presence of a Homomorphism Operator and Exclusive-Or Motivation Introduction Symbolic approach • Intruder controls the network • Messages represented by terms - { m } k - � m 1 , m 2 � • Number of sessions bounded • Perfect encryption hypothesis + algebraic properties Advantages • Automatic verification • Useful abstraction 2/25
Symbolic Protocol Analysis in Presence of a Homomorphism Operator and Exclusive-Or Motivation Example: Key Exchange TMN Protocol (simplified) TMN Protocol: Distribution of a fresh symmetric key [Tatebayashi, Matsuzuki, Newmann 89]: A S W → : A , W , { N A } Pub S → : S , A ← : W , A , { N W } Pub S ← : S , W , N A ⊕ N W Alice retrieves N W : Using x ⊕ x = 0 and x ⊕ 0 = x , knowing N A 3/25
Symbolic Protocol Analysis in Presence of a Homomorphism Operator and Exclusive-Or Motivation Example: Key Exchange TMN Protocol (simplified) Attack on TMN Protocol [Simmons 89] With homomorphic encryption { a } k ⊕ { b } k = { a ⊕ b } k C S Q → : C , Q , { N W } Pub S ⊕ { N C } Pub S � �� � { N W ⊕ N C } PubS → : S , C ← : Q , C , { N Q } Pub S ← : S , ( N W ⊕ N C ) ⊕ N Q Cheshire Learns: N W Using x ⊕ x = 0 and x ⊕ 0 = x , knowing N C and N Q 4/25
Symbolic Protocol Analysis in Presence of a Homomorphism Operator and Exclusive-Or Motivation Example: Key Exchange TMN Protocol (simplified) Attack on TMN Protocol [Simmons 89] With homomorphic function h ( a ) ⊕ h ( b ) = h ( a ⊕ b ) C S Q → : C , Q , h ( N W ) ⊕ h ( N C ) � �� � h ( N W ⊕ N C ) → : S , C ← : Q , C , h ( N Q ) ← : S , ( N W ⊕ N C ) ⊕ N Q Cheshire Learns: N W Using x ⊕ x = 0 and x ⊕ 0 = x , knowing N C and N Q 5/25
Symbolic Protocol Analysis in Presence of a Homomorphism Operator and Exclusive-Or State of the Art Intruder Capabilities Deduction System: Extended Dolev-Yao T ⊢ � u , v � u ∈ T (A) (UL) T ⊢ u T ⊢ u (UR) T ⊢ � u , v � T ⊢ u T ⊢ v (P) T ⊢ � u , v � T ⊢ v T ⊢ { u } v T ⊢ v T ⊢ u T ⊢ v (C) (D) T ⊢ { u } v T ⊢ u T ⊢ u 1 · · · T ⊢ u n ( M E ) C is an context made with { h , ⊕} T ⊢ C [ u 1 , . . . , u n ] ↓ Example for M E T ⊢ a ⊕ h ( a ) T ⊢ bT ⊢ a ⊕ h 2 ( a ) ⊕ h ( b ) C [ u 1 , u 2 ] = u 1 ⊕ h ( u 1 ) ⊕ h ( u 2 ) 6/25
Symbolic Protocol Analysis in Presence of a Homomorphism Operator and Exclusive-Or State of the Art Intruder Deduction Problem Passive Intruder with homomorphisme and Xor Theorem of Locality [LLT’05,Del’05] A minimal proof P of T ⊢ u contains only computable terms. Complexity of Intruder Deduction [Del’05] T ⊢ u (for T , u ground) is decidable in PTIME The proof uses • McAllester’s locality theorem • linear equation solving over Z / 2 Z [ h ] 7/25
Symbolic Protocol Analysis in Presence of a Homomorphism Operator and Exclusive-Or State of the Art Security Problem Some Results to Active Intruder XOR : ACUN [Rusinowitch & al 03] [Comon-Shmatikov 03] • ( x ⊕ y ) ⊕ z = x ⊕ ( y ⊕ z ) Associativity • x ⊕ y = y ⊕ x Commutativity • x ⊕ 0 = x Unity • x ⊕ x = 0 Nilpotency Abelian Group and Exponential : AG [Millen-Shmatikov 05] • ( x ⊕ y ) ⊕ z = x ⊕ ( y ⊕ z ) Associativity • x ⊕ y = y ⊕ x Commutativity • x ⊕ 0 = x Unity • x ⊕ I ( x ) = 0 Inversion 8/25
Symbolic Protocol Analysis in Presence of a Homomorphism Operator and Exclusive-Or State of the Art Security Problem Our contribution Homomorphism over XOR : ACUNh • h ( x ⊕ y ) = h ( x ) ⊕ h ( y ) • ( x ⊕ y ) ⊕ z = x ⊕ ( y ⊕ z ) Associativity • x ⊕ y = y ⊕ x Commutativity • x ⊕ 0 = x Unity • x ⊕ x = 0 Nilpotency Theorem The security problem with a bounded number of sessions is decidable with ACUNh. 9/25
Symbolic Protocol Analysis in Presence of a Homomorphism Operator and Exclusive-Or State of the Art Security Problem Outline 1 Motivation Introduction Example: Key Exchange TMN Protocol (simplified) 2 State of the Art Intruder Capabilities Intruder Deduction Problem Security Problem 3 Modelisation of Protocols (Active Attacker) Constraints System Well-defined Constraints System 4 From Well-defined Constraints System to System of Equations 5 Conclusion 10/25
Symbolic Protocol Analysis in Presence of a Homomorphism Operator and Exclusive-Or Modelisation of Protocols (Active Attacker) Outline 1 Motivation Introduction Example: Key Exchange TMN Protocol (simplified) 2 State of the Art Intruder Capabilities Intruder Deduction Problem Security Problem 3 Modelisation of Protocols (Active Attacker) Constraints System Well-defined Constraints System 4 From Well-defined Constraints System to System of Equations 5 Conclusion 11/25
Symbolic Protocol Analysis in Presence of a Homomorphism Operator and Exclusive-Or Modelisation of Protocols (Active Attacker) Constraints System Modelisation of a protocol in a system of constraint The Intruder is the network, he can listen, built, send and replay messages. recv ( u 1 ); send ( v 1 ) recv ( u 2 ); send ( v 2 ) := P . . . recv ( u n ); send ( v n ) T 0 Intruder initial knowledge. T 0 � u 1 T 0 , v 1 � u 2 C := . . . T 0 , v 1 , . . . , v n � s If this system has a solution σ then the secret s can be obtain by the Intruder. 12/25
Symbolic Protocol Analysis in Presence of a Homomorphism Operator and Exclusive-Or Modelisation of Protocols (Active Attacker) Well-defined Constraints System System of Constraints Well-formed [Millen-Shmatikov 03] C = { T i � u i } 1 ≤ i ≤ k is well-formed if: • monotonicity : The knowledge of the intruder is increasing. T 1 ⊆ T 2 ⊆ . . . ⊆ T k • origination : Variables appear first on right side: x ∈ vars ( T i ) ⇒ ∃ j < i such that : x ∈ vars ( u j ) System of Constraints Well-defined [Millen-Shmatikov 03] C is well-defined if for every substitution θ , C θ is well-formed. 13/25
Symbolic Protocol Analysis in Presence of a Homomorphism Operator and Exclusive-Or Modelisation of Protocols (Active Attacker) Well-defined Constraints System System of Constraints Well-formed [Millen-Shmatikov 03] C = { T i � u i } 1 ≤ i ≤ k is well-formed if: • monotonicity : The knowledge of the intruder is increasing. T 1 ⊆ T 2 ⊆ . . . ⊆ T k • origination : Variables appear first on right side: x ∈ vars ( T i ) ⇒ ∃ j < i such that : x ∈ vars ( u j ) System of Constraints Well-defined [Millen-Shmatikov 03] C is well-defined if for every substitution θ , C θ is well-formed. 13/25
Symbolic Protocol Analysis in Presence of a Homomorphism Operator and Exclusive-Or Modelisation of Protocols (Active Attacker) Well-defined Constraints System Well-Definedness: Example � T 0 X ⊕ Y � C := T 0 , X c � 14/25
Symbolic Protocol Analysis in Presence of a Homomorphism Operator and Exclusive-Or Modelisation of Protocols (Active Attacker) Well-defined Constraints System Well-Definedness: Example � T 0 X ⊕ Y � C := T 0 , X c � Monotonicity OK ! 14/25
Symbolic Protocol Analysis in Presence of a Homomorphism Operator and Exclusive-Or Modelisation of Protocols (Active Attacker) Well-defined Constraints System Well-Definedness: Example � T 0 X ⊕ Y � C := T 0 , X c � Monotonicity OK ! Origination OK ! 14/25
Symbolic Protocol Analysis in Presence of a Homomorphism Operator and Exclusive-Or Modelisation of Protocols (Active Attacker) Well-defined Constraints System Well-Definedness: Example � T 0 X ⊕ Y � C := T 0 , X c � Monotonicity OK ! Origination OK ! But NOT well-defined ! θ = { Y → X } and C θ is not well-formed: � T 0 0 � C θ := T 0 , X c � 14/25
Symbolic Protocol Analysis in Presence of a Homomorphism Operator and Exclusive-Or From Well-defined Constraints System to System of Equations Outline 1 Motivation Introduction Example: Key Exchange TMN Protocol (simplified) 2 State of the Art Intruder Capabilities Intruder Deduction Problem Security Problem 3 Modelisation of Protocols (Active Attacker) Constraints System Well-defined Constraints System 4 From Well-defined Constraints System to System of Equations 5 Conclusion 15/25
Recommend
More recommend
Explore More Topics
Stay informed with curated content and fresh updates.