Stream Cipher
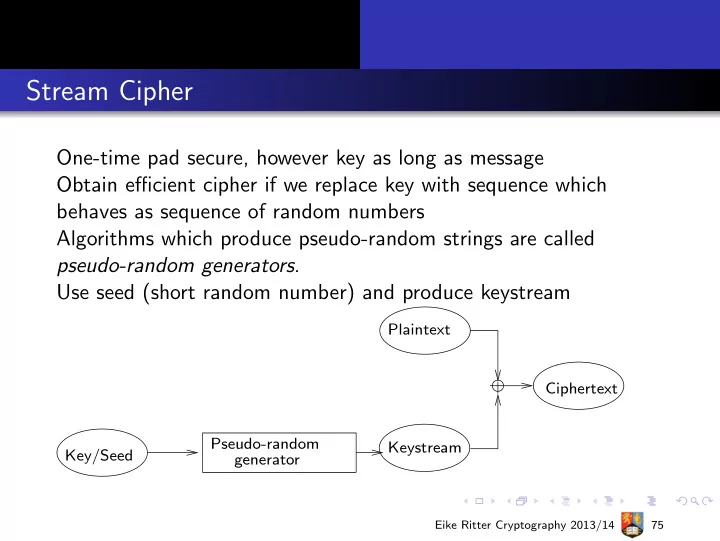
One-time pad secure, however key as long as message Obtain efficient cipher if we replace key with sequence which behaves as sequence of random numbers Algorithms which produce pseudo-random strings are called pseudo-random generators. Use seed (short random number) and produce keystream
Key/Seed generator Pseudo-random Keystream Plaintext Ciphertext
Eike Ritter Cryptography 2013/14 75