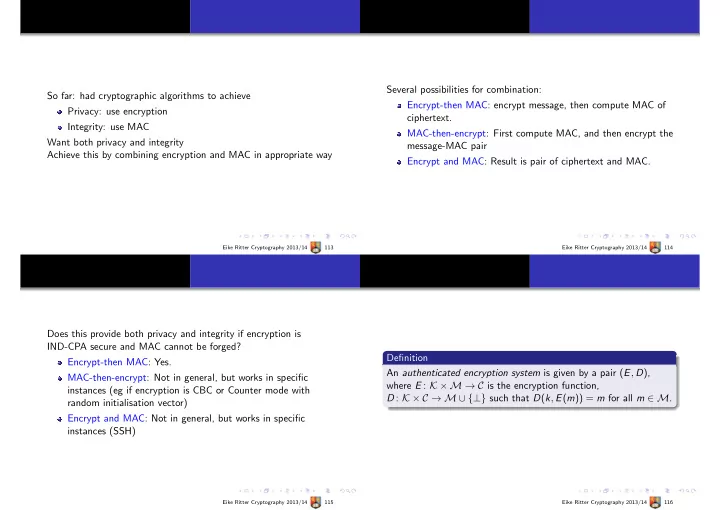
So far: had cryptographic algorithms to achieve Privacy: use encryption Integrity: use MAC Want both privacy and integrity Achieve this by combining encryption and MAC in appropriate way
Eike Ritter Cryptography 2013/14 113
Several possibilities for combination: Encrypt-then MAC: encrypt message, then compute MAC of ciphertext. MAC-then-encrypt: First compute MAC, and then encrypt the message-MAC pair Encrypt and MAC: Result is pair of ciphertext and MAC.
Eike Ritter Cryptography 2013/14 114
Does this provide both privacy and integrity if encryption is IND-CPA secure and MAC cannot be forged? Encrypt-then MAC: Yes. MAC-then-encrypt: Not in general, but works in specific instances (eg if encryption is CBC or Counter mode with random initialisation vector) Encrypt and MAC: Not in general, but works in specific instances (SSH)
Eike Ritter Cryptography 2013/14 115
Definition An authenticated encryption system is given by a pair (E, D), where E : K × M → C is the encryption function, D : K × C → M ∪ {⊥} such that D(k, E(m)) = m for all m ∈ M.
Eike Ritter Cryptography 2013/14 116