Computer Science
Lecture 18, page 1
Security in Distributed Systems
- Introduction
- Cryptography
- Authentication
- Key exchange
Computer Science
Lecture 18, page 2
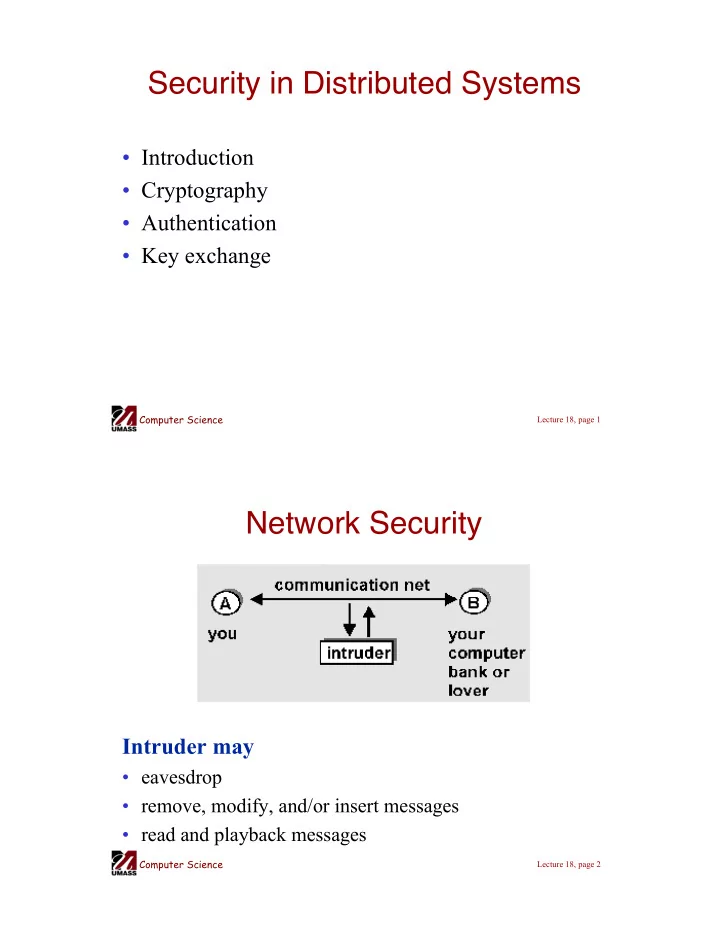
Network Security
Intruder may
- eavesdrop
- remove, modify, and/or insert messages
- read and playback messages