Security II: Cryptography
Markus Kuhn
Computer Laboratory, University of Cambridge https://www.cl.cam.ac.uk/teaching/1617/SecurityII/
These notes are provided as an aid for following the lectures, and are not a substitute for attending
Lent 2017 – Part II
security2-slides-4up.pdf 2017-03-24 19:03 e4e8041 1
Related textbooks
Main reference:
◮ Jonathan Katz, Yehuda Lindell:
Introduction to Modern Cryptography Chapman & Hall/CRC, 2nd ed., 2014 Further reading:
◮ Christof Paar, Jan Pelzl:
Understanding Cryptography Springer, 2010
http://www.springerlink.com/content/978-3-642-04100-6/ http://www.crypto-textbook.com/ ◮ Douglas Stinson:
Cryptography – Theory and Practice 3rd ed., CRC Press, 2005
◮ Menezes, van Oorschot, Vanstone:
Handbook of Applied Cryptography CRC Press, 1996
http://www.cacr.math.uwaterloo.ca/hac/
2
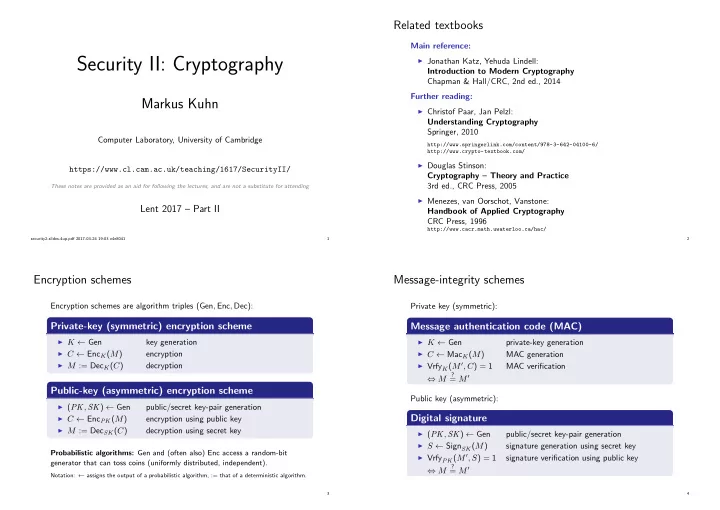
Encryption schemes
Encryption schemes are algorithm triples (Gen, Enc, Dec):
Private-key (symmetric) encryption scheme
◮ K ← Gen
key generation
◮ C ← EncK(M)
encryption
◮ M := DecK(C)
decryption
Public-key (asymmetric) encryption scheme
◮ (PK, SK) ← Gen
public/secret key-pair generation
◮ C ← EncPK(M)
encryption using public key
◮ M := DecSK(C)
decryption using secret key
Probabilistic algorithms: Gen and (often also) Enc access a random-bit generator that can toss coins (uniformly distributed, independent).
Notation: ← assigns the output of a probabilistic algorithm, := that of a deterministic algorithm.
3
Message-integrity schemes
Private key (symmetric):
Message authentication code (MAC)
◮ K ← Gen
private-key generation
◮ C ← MacK(M)
MAC generation
◮ VrfyK(M ′, C) = 1
MAC verification ⇔ M
?
= M ′ Public key (asymmetric):
Digital signature
◮ (PK, SK) ← Gen
public/secret key-pair generation
◮ S ← SignSK(M)
signature generation using secret key
◮ VrfyPK(M ′, S) = 1
signature verification using public key ⇔ M
?
= M ′
4