SCARE of Secret Ciphers with SPN Structures Matthieu Rivain Joint - PowerPoint PPT Presentation
SCARE of Secret Ciphers with SPN Structures Matthieu Rivain Joint work with Thomas Roche (ANSSI) ASIACRYPT 2013 December 3rd Outline 1 Introduction 2 Substitution-Permutation Networks 3 Basic SCARE of Classical SPN Structures 4
SCARE of Secret Ciphers with SPN Structures Matthieu Rivain Joint work with Thomas Roche (ANSSI) ASIACRYPT 2013 – December 3rd
Outline 1 � Introduction 2 � Substitution-Permutation Networks 3 � Basic SCARE of Classical SPN Structures 4 � SCARE in the Presence of Noisy Leakage 5 � Attack Experiments
Outline 1 � Introduction 2 � Substitution-Permutation Networks 3 � Basic SCARE of Classical SPN Structures 4 � SCARE in the Presence of Noisy Leakage 5 � Attack Experiments
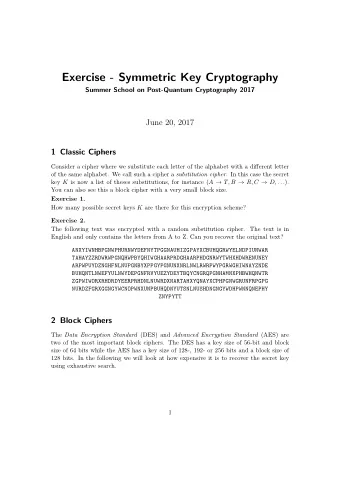
Introduction SCARE : Side-Channel Analysis for Reverse Engineering • private code recovery • secret crypto design recovery
Introduction SCARE : Side-Channel Analysis for Reverse Engineering • private code recovery • secret crypto design recovery ⇐ This paper
Introduction SCARE : Side-Channel Analysis for Reverse Engineering • private code recovery • secret crypto design recovery ⇐ This paper • usual in mobile SIM / pay-TV cards
Previous works [Novak. ACNS 2003] • secret instance of the GSM A3/A8 algorithm • side-channel assumption: detection of colliding s-boxes • recovery of one secret s-box [Clavier. ePrint 2004/ICISS 2007] • recovery of the two s-boxes and the secret key
Limitations • Target: specific cipher structure • Assumption: idealized leakage model ⇒ perfect collision detection Our work • Consider a generic class of ciphers: Substitution-Permutation Networks (SPN) • Relax the idealized leakage assumption ◮ consider noisy leakages ◮ experiments in a practical leakage model
Further works [Daudigny et al. ACNS 2005] (DES) [R´ eal et al. CARDIS 2008] (hardware Feistel) [Guilley et al. LATINCRYPT 2010] (stream ciphers) [Clavier et al. INDOCRYPT 2013] (modified AES)
Outline 1 � Introduction 2 � Substitution-Permutation Networks 3 � Basic SCARE of Classical SPN Structures 4 � SCARE in the Presence of Noisy Leakage 5 � Attack Experiments
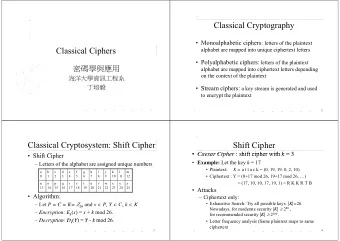
Substitution-Permutation Networks k 1 k 2 k r ... p ρ ρ ρ c We consider two types of round functions: • Classical SPN structures • Feistel structures
Substitution-Permutation Networks k 1 k 2 k r ... p ρ ρ ρ c We consider two types of round functions: • Classical SPN structures ⇐ This talk • Feistel structures
Classical SPN Structure k i S • State: n × m bits S • n s-box computations λ • m -bits s-box inputs S x 1 a 1 , 1 a 1 , 2 a 1 ,n x 1 · · · x 2 a 2 , 1 a 2 , 2 a 2 ,n x 2 · · · λ : with a i,j ∈ F 2 m . �→ . . . · . ... . . . . . . . . . . x n a n, 1 a n, 2 a n,n x n · · ·
Outline 1 � Introduction 2 � Substitution-Permutation Networks 3 � Basic SCARE of Classical SPN Structures 4 � SCARE in the Presence of Noisy Leakage 5 � Attack Experiments
Attacker Model Basic assumption: Colliding s-box computations can be detected from the side-channel leakage. Specifically, we assume that the attacker is able to (i) identify the s-box computations in the side-channel leakage trace and extract the leakage corresponding to each s-box computation, (ii) decide whether two s-box computations y 1 ← S ( x 1 ) and y 2 ← S ( x 2 ) are such that x 1 = x 2 or not from their respective leakages.
Equivalent Representations One cipher has several representations 1 . Change the s-box: S ′ ( x ) = S ( x ⊕ δ ) and the round keys: k ′ i = ( k i, 1 ⊕ δ, k i, 2 ⊕ δ, . . . , k i,n ⊕ δ )
Equivalent Representations One cipher has several representations 1 . Change the s-box: S ′ ( x ) = S ( x ⊕ δ ) and the round keys: k ′ i = ( k i, 1 ⊕ δ, k i, 2 ⊕ δ, . . . , k i,n ⊕ δ ) 2 . Change the s-box: S ′ ( x ) = α · S ( x ) i,j = a i,j and the matrix coefficients: a ′ α
Equivalent Representations One cipher has several representations 1 . Change the s-box: S ′ ( x ) = S ( x ⊕ δ ) and the round keys: k ′ i = ( k i, 1 ⊕ δ, k i, 2 ⊕ δ, . . . , k i,n ⊕ δ ) 2 . Change the s-box: S ′ ( x ) = α · S ( x ) i,j = a i,j and the matrix coefficients: a ′ α The attack can recover the cipher up to equivalent representations
Equivalent Representations One cipher has several representations 1 . Change the s-box: S ′ ( x ) = S ( x ⊕ δ ) and the round keys: k ′ i = ( k i, 1 ⊕ δ, k i, 2 ⊕ δ, . . . , k i,n ⊕ δ ) 2 . Change the s-box: S ′ ( x ) = α · S ( x ) i,j = a i,j and the matrix coefficients: a ′ α The attack can recover the cipher up to equivalent representations We fix a representation by setting k 1 , 1 = 0 and a 1 , 1 = 1
Stage 1: Recovering k 1 k 1 k 1 p 1 p 0 S S 1 p 2 p 0 S S 2 p 0 p n S S n
Stage 1: Recovering k 1 k 1 k 1 p 1 p 0 S S 1 p 2 p 0 S S 2 collision p 0 p n S S n
Stage 1: Recovering k 1 k 1 k 1 p 1 p 0 S S 1 p 2 p 0 S S 2 collision p 0 p n S S n p 1 ⊕ k 1 , 1 = p ′ 2 ⊕ k 1 , 2
Stage 1: Recovering k 1 k 1 k 1 p 1 p 0 S S 1 p 2 p 0 S S 2 collision p 0 p n S S n p 1 ⊕ k 1 , 1 = p ′ 2 ⊕ k 1 , 2
Stage 1: Recovering k 1 k 1 k 1 p 1 p 0 S S 1 p 2 p 0 S S 2 collision p 0 p n S S n p 1 ⊕ k 1 , 1 = p ′ k 1 , 2 = p 1 ⊕ p ′ 2 ⊕ k 1 , 2 2 ⊕ k 1 , 1 ⇒
Stage 1: Recovering k 1 k 1 k 1 p 1 p 0 S S 1 p 2 p 0 S S 2 collision p 0 p n S S n p 1 ⊕ k 1 , 1 = p ′ k 1 , 2 = p 1 ⊕ p ′ 2 ⊕ k 1 , 2 2 ⊕ k 1 , 1 ⇒
Stage 1: Recovering k 1 k 1 k 1 p 1 p 0 S S 1 p 2 p 0 S S 2 collision p 0 p n S S n p 1 ⊕ k 1 , 1 = p ′ k 1 , 2 = p 1 ⊕ p ′ 2 ⊕ k 1 , 2 2 ⊕ k 1 , 1 ⇒ p 2 ⊕ k 1 , 2 = p ′ n ⊕ k 1 ,n
Stage 1: Recovering k 1 k 1 k 1 p 1 p 0 S S 1 p 2 p 0 S S 2 collision p 0 p n S S n p 1 ⊕ k 1 , 1 = p ′ k 1 , 2 = p 1 ⊕ p ′ 2 ⊕ k 1 , 2 2 ⊕ k 1 , 1 ⇒ p 2 ⊕ k 1 , 2 = p ′ n ⊕ k 1 ,n
Stage 1: Recovering k 1 k 1 k 1 p 1 p 0 S S 1 p 2 p 0 S S 2 collision p 0 p n S S n p 1 ⊕ k 1 , 1 = p ′ k 1 , 2 = p 1 ⊕ p ′ 2 ⊕ k 1 , 2 2 ⊕ k 1 , 1 ⇒ p 2 ⊕ k 1 , 2 = p ′ k 1 ,n = p 1 ⊕ p ′ n ⊕ k 1 ,n n ⊕ k 1 , 2 ⇒ and so on ...
Stage 2: Recovering λ , S and k 2 0 S leakage basis
Stage 2: Recovering λ , S and k 2 0 S 1 S leakage basis
Stage 2: Recovering λ , S and k 2 0 S 1 S 2 S 2 m − 1 S leakage basis
Stage 2: Recovering λ , S and k 2 k 2 0 S w 1 S 1 S w 2 S 2 S w n 2 m − 1 S S leakage basis 2nd round
Stage 2: Recovering λ , S and k 2 k 2 0 S w 1 S collision 1 S w 2 S 2 S w n 2 m − 1 S S leakage basis 2nd round
Stage 2: Recovering λ , S and k 2 k 2 0 S w 1 S S 1 w 2 S collision S 2 w n 2 m − 1 S S leakage basis 2nd round
Stage 2: Recovering λ , S and k 2 k 2 0 S w 1 S S 1 w 2 S S 2 collision w n 2 m − 1 S S leakage basis 2nd round
Stage 2: Recovering λ , S and k 2 k 2 0 S w 1 S 1 S w 2 S 2 S w n 2 m − 1 S S leakage basis 2nd round
Stage 2: Recovering λ , S and k 2 k 2 0 S w 1 S collision w 1 ⊕ k 2 , 1 = β 1 1 S w 2 S 2 S w n 2 m − 1 S S leakage basis 2nd round
Stage 2: Recovering λ , S and k 2 k 2 0 S w 1 S w 1 ⊕ k 2 , 1 = β 1 S 1 w 2 S w 2 ⊕ k 2 , 2 = β 2 collision S 2 w n 2 m − 1 S S leakage basis 2nd round
Stage 2: Recovering λ , S and k 2 k 2 0 S w 1 S w 1 ⊕ k 2 , 1 = β 1 S 1 w 2 S w 2 ⊕ k 2 , 2 = β 2 . S 2 . . collision w n ⊕ k 2 ,n = β n w n 2 m − 1 S S leakage basis 2nd round
Stage 2: Recovering λ , S and k 2 We have w 1 k 2 , 1 β 1 w 2 k 2 , 2 β 2 = . . ⊕ . . . . . . . w n k 2 ,n β n
Stage 2: Recovering λ , S and k 2 We have w 1 k 2 , 1 β 1 a 1 , 1 a 1 , 2 a 1 ,n S ( p 1 ⊕ k 1 , 1 ) · · · w 2 k 2 , 2 β 2 a 2 , 1 a 2 , 2 a 2 ,n S ( p 2 ⊕ k 1 , 2 ) · · · = = . . ⊕ . . . . · . ... . . . . . . . . . . . . . . w n k 2 ,n β n a n, 1 a n, 2 a n,n S ( p n ⊕ k 1 ,n ) · · ·
Stage 2: Recovering λ , S and k 2 We have w 1 k 2 , 1 β 1 a 1 , 1 a 1 , 2 a 1 ,n S ( p 1 ⊕ k 1 , 1 ) · · · w 2 k 2 , 2 β 2 a 2 , 1 a 2 , 2 a 2 ,n S ( p 2 ⊕ k 1 , 2 ) · · · = = . . ⊕ . . . . · . ... . . . . . . . . . . . . . . w n k 2 ,n β n a n, 1 a n, 2 a n,n S ( p n ⊕ k 1 ,n ) · · ·
Recommend
More recommend
Explore More Topics
Stay informed with curated content and fresh updates.