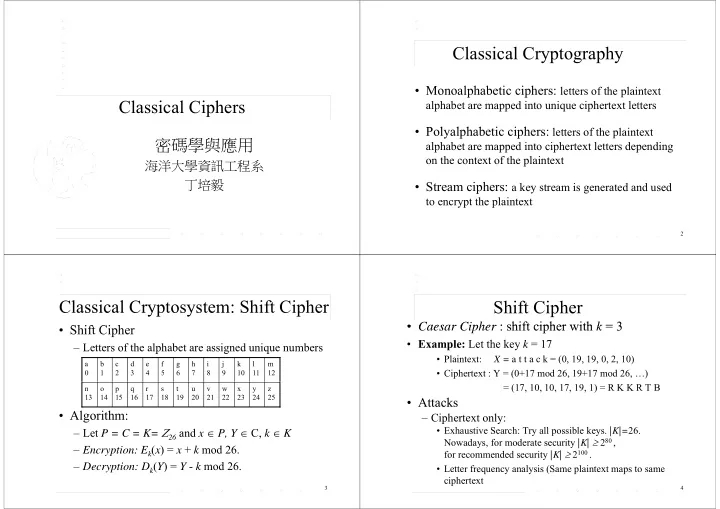
Classical Ciphers
密碼學與應用
海洋大學資訊工程系 丁培毅 丁培毅
Classical Cryptography
- Monoalphabetic ciphers: letters of the plaintext
alphabet are mapped into unique ciphertext letters
P l l h b i i h
- Polyalphabetic ciphers: letters of the plaintext
alphabet are mapped into ciphertext letters depending
- n the context of the plaintext
St i h
k i d d d
- Stream ciphers: a key stream is generated and used
to encrypt the plaintext
2
Classical Cryptosystem: Shift Cipher
Shif Ci h
- Shift Cipher
– Letters of the alphabet are assigned unique numbers p g q
m 12 l 11 k 10 j 9 i 8 h 7 g 6 f 5 e 4 d 3 c 2 b 1 a z 25 y 24 x 23 w 22 v 21 u 20 t 19 s 18 r 17 q 16 p 15
- 14
n 13
- Algorithm:
– Let P = C = K= 26 and x P, Y C, k K
26
, , – Encryption: Ek(x) = x + k mod 26. Decryption: D (Y) = Y k mod 26
3
– Decryption: Dk(Y) = Y - k mod 26.
Shift Cipher
- Caesar Cipher : shift cipher with k = 3
- Caesar Cipher : shift cipher with k = 3
- Example: Let the key k = 17
- Plaintext: X = a t t a c k = (0, 19, 19, 0, 2, 10)
- Ciphertext : Y = (0+17 mod 26, 19+17 mod 26, …)
= (17, 10, 10, 17, 19, 1) = R K K R T B
- Attacks
– Ciphertext only:
- Exhaustive Search: Try all possible keys. |K|=26.
Nowadays, for moderate security |K| 280 , for recommended security |K| 2100 . f l i ( l i
4
- Letter frequency analysis (Same plaintext maps to same