SLIDE 1
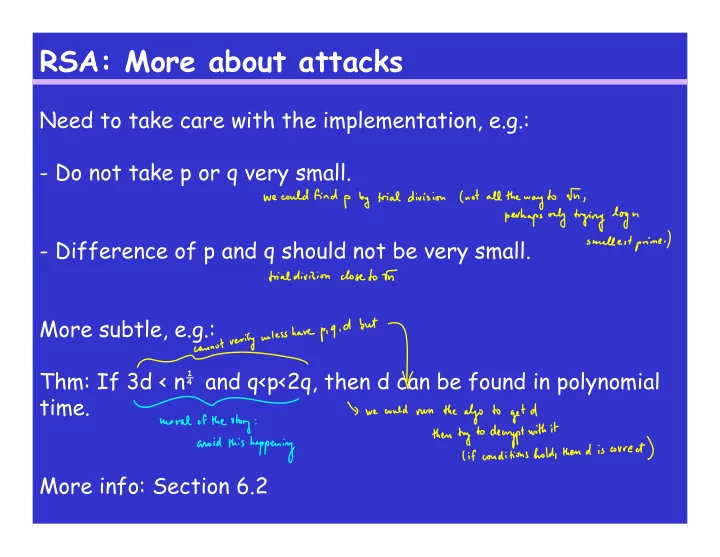
RSA: More about attacks
Need to take care with the implementation, e.g.:
- Do not take p or q very small.
- Difference of p and q should not be very small.