1
Role-based access control
1
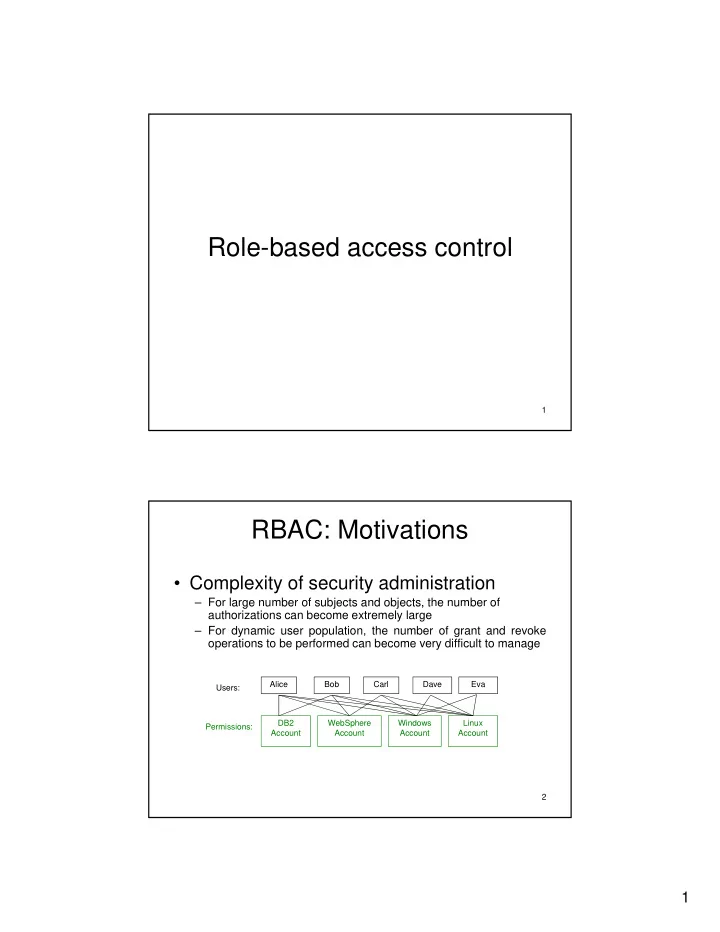
RBAC: Motivations
- Complexity of security administration
– For large number of subjects and objects, the number of
- a ge
u be o subjects a d objects, t e u be o authorizations can become extremely large – For dynamic user population, the number of grant and revoke
- perations to be performed can become very difficult to manage
Alice Bob Carl Dave Eva Users: 2 Windows Account Linux Account WebSphere Account DB2 Account Permissions: