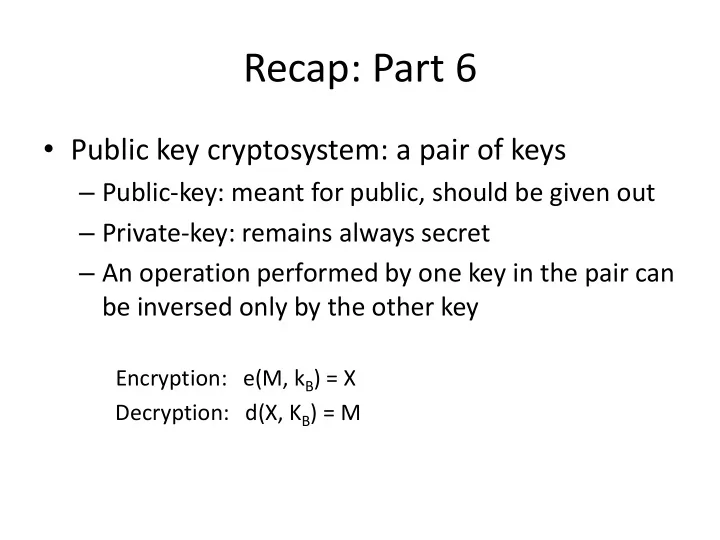
Recap: Part 6
- Public key cryptosystem: a pair of keys
Recap: Part 6 Public key cryptosystem: a pair of keys Public-key: - - PowerPoint PPT Presentation
Recap: Part 6 Public key cryptosystem: a pair of keys Public-key: meant for public, should be given out Private-key: remains always secret An operation performed by one key in the pair can be inversed only by the other key
KPS KSS KPA KSA KPB KSB (KPA KPB … )
KPS KSS KPA KSA KPB KSB (KPA KPB … )
KAS KBS (KAS KBS … )
{NA}KAB {NA - 1}KAB
KAS KBS
{NA}KAB {NA - 1}KAB
g, p, b
{NA}KAB {NA - 1}KAB
g, p, a
KPS KSS KPA, KSA, KPS, g, p, a KPB, KSB, KPS, g, p, b (KPA KPB … )
Alice wants to send a huge message M to Bob with the following properties: Authentication, integrity, non-repudiation, confidentiality Alice and Bob trust TTP Sam Symmetric key encryption is multiple orders cheaper than asymmetric key encryption List out the steps involved in transferring M from Alice to Bob