1/24/2012
TCP/IP: ICMP, UDP
Network Security Lecture 5
Recap and overview
- Looking at security of TCP/IP
– IP, Ethernet, ARP
- Sniffing the network and forging packets
– tcpdump, wireshark
- Today: ICMP and UDP
Eike Ritter 1 Network Security - Lecture 5
Internet Control Message Protocol
- Used to exchange control/error messages
about the delivery of IP datagrams
- Encapsulated in IP datagrams
- Messages can be
– Requests – Responses – Error messages
- RFC 792
Eike Ritter Network Security - Lecture 5 2
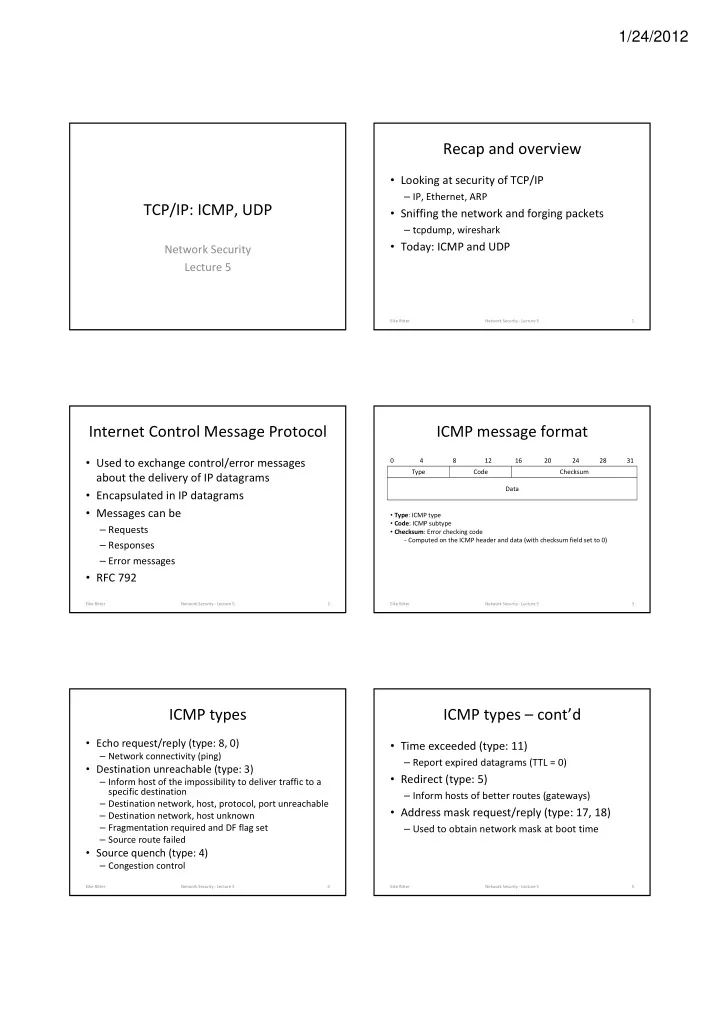
ICMP message format
Type Code Checksum Data
Eike Ritter Network Security - Lecture 5 3
4 8 16 12 31
- Type: ICMP type
- Code: ICMP subtype
- Checksum: Error checking code
- Computed on the ICMP header and data (with checksum field set to 0)
20 24 28
ICMP types
- Echo request/reply (type: 8, 0)
– Network connectivity (ping)
- Destination unreachable (type: 3)
– Inform host of the impossibility to deliver traffic to a specific destination – Destination network, host, protocol, port unreachable – Destination network, host unknown – Fragmentation required and DF flag set – Source route failed
- Source quench (type: 4)
– Congestion control
Eike Ritter Network Security - Lecture 5 4
ICMP types – cont’d
- Time exceeded (type: 11)
– Report expired datagrams (TTL = 0)
- Redirect (type: 5)
– Inform hosts of better routes (gateways)
- Address mask request/reply (type: 17, 18)
– Used to obtain network mask at boot time
Eike Ritter Network Security - Lecture 5 5