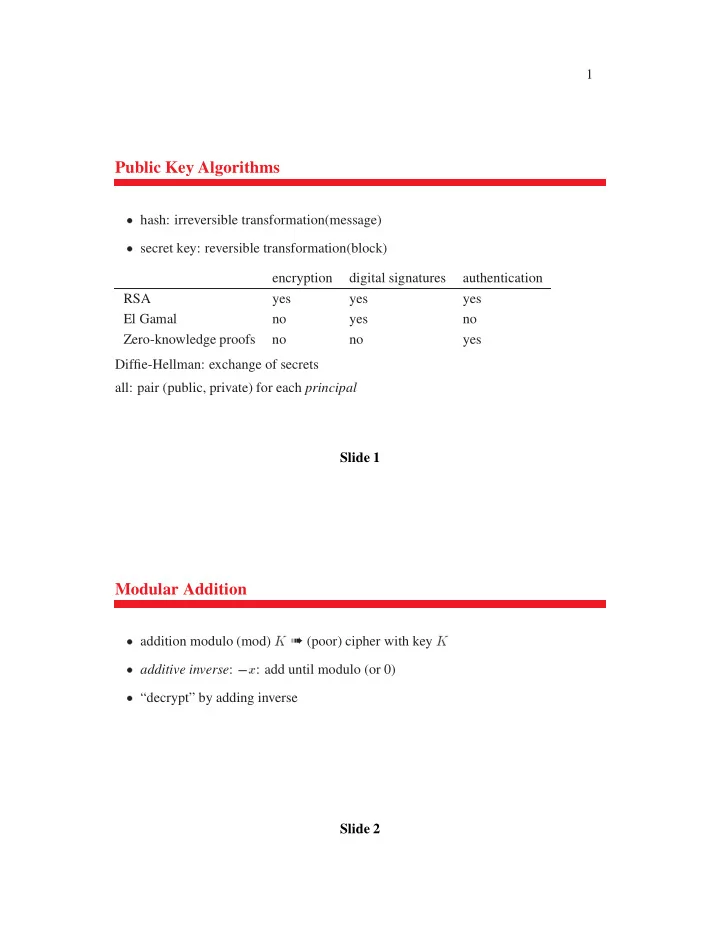
SLIDE 1
2
Modular Multiplication
- 1
2 3 4 5 6 7 8 9 1 1 2 3 4 5 6 7 8 9 2 2 4 6 8 2 4 6 8 3 3 6 9 2 5 8 1 4 7
multiplication by 1, 3, 7, 9 works as cipher multiplicative inverse x 1: y- x
- nly 1, 3, 7, 9 have multiplicative inverses (e.g., 7
Slide 3
Totient Function
- x;
– if
n prime, f1; 2; : : : ; n- 1g are rp ➠
- 1
– if
n = p- q,
- 1)(q
- 1):
- n
- 1g; exclude non-rp
- p multiples of
- 1 numbers – don’t count 0 twice
- (pq
- (p
- 1)
- 1)(q
- 1)