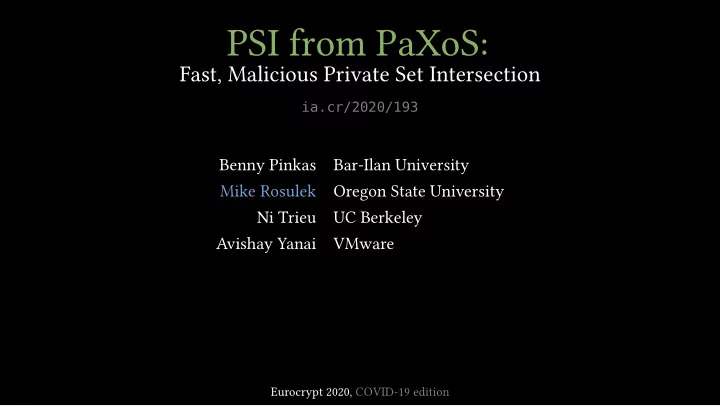
PSI from PaXoS:
Fast, Malicious Private Set Intersection
ia.cr/2020/193
Benny Pinkas Bar-Ilan University Mike Rosulek Oregon State University Ni Trieu UC Berkeley Avishay Yanai VMware
Eurocrypt 2020, COVID-19 edition
PSI from PaXoS: Fast, Malicious Private Set Intersection - - PowerPoint PPT Presentation
PSI from PaXoS: Fast, Malicious Private Set Intersection ia.cr/2020/193 Benny Pinkas Bar-Ilan University Mike Rosulek Oregon State University Ni Trieu UC Berkeley Avishay Yanai VMware Eurocrypt 2020, COVID-19 edition what is private set
ia.cr/2020/193
Benny Pinkas Bar-Ilan University Mike Rosulek Oregon State University Ni Trieu UC Berkeley Avishay Yanai VMware
Eurocrypt 2020, COVID-19 edition
Alice
e u r
r y p t
Bob
c
i d 1 9 s u x
Alice
e u r
r y p t
Bob
c
i d 1 9 s u x
Alice
e u r
r y p t
Bob
c
i d 1 9 s u x
?? ?? ?? ?? ?? ?? ??
Alice
e u r
r y p t
Bob
c
i d 1 9 s u x
?? ?? ?? ?? ?? ??
20 22 24 26 28 210 212 24 26 28 210 212 214
PRTY19 KKRT16 classic DH
insecure hashing running time (s) communication (MB) DKT10 = ia.cr/2010/469 KKRT16 = ia.cr/2016/799 RR17a = ia.cr/2016/746 RR17b = ia.cr/2017/769 PRTY19 = ia.cr/2019/634
20 22 24 26 28 210 212 24 26 28 210 212 214
PRTY19 KKRT16 classic DH RR17b RR17a DKT10
insecure hashing running time (s) communication (MB) DKT10 = ia.cr/2010/469 KKRT16 = ia.cr/2016/799 RR17a = ia.cr/2016/746 RR17b = ia.cr/2017/769 PRTY19 = ia.cr/2019/634
20 22 24 26 28 210 212 24 26 28 210 212 214
this work PRTY19 KKRT16 classic DH RR17b RR17a DKT10
insecure hashing running time (s) communication (MB)
vs prior malicious:
◮ ∼3× faster ◮ 8× less comm
vs semi-honest:
◮ 25% slower ◮ 60–150% more comm
asymptotically:
◮ first O(n) malicious
from OT extension
DKT10 = ia.cr/2010/469 KKRT16 = ia.cr/2016/799 RR17a = ia.cr/2016/746 RR17b = ia.cr/2017/769 PRTY19 = ia.cr/2019/634
what does “PaXoS” mean?
Alice Bob
1 2 3 4 5 6 7 8 9 . . .
Alice Bob
1 2 3 4 5 6 7 8 9 . . .
x1 x2 x3 x4 x5 x6 x7 x8 x9
Alice Bob
1 2 3 4 5 6 7 8 9 . . .
F1(x1) F1(·) F2(x2) F2(·) F3(x3) F3(·) F4(x4) F4(·) F5(x5) F5(·) F6(x6) F6(·) F7(x7) F7(·) F8(x8) F8(·) F9(x9) F9(·)
Alice Bob
1 2 3 4 5 6 7 8 9 . . .
F1(x1) F1(·) F2(x2) F2(·) F3(x3) F3(·) F4(x4) F4(·) F5(x5) F5(·) F6(x6) F6(·) F7(x7) F7(·) F8(x8) F8(·) F9(x9) F9(·) learns nothing about xi’s
Alice Bob
1 2 3 4 5 6 7 8 9 . . .
F1(x1) F1(·) F2(x2) F2(·) F3(x3) F3(·) F4(x4) F4(·) F5(x5) F5(·) F6(x6) F6(·) F7(x7) F7(·) F8(x8) F8(·) F9(x9) F9(·) learns nothing about xi’s all other Fi(x∗) look random
Alice Bob
1 2 3 4 5 6 7 8 9 . . .
F1(x1) F1(·) F2(x2) F2(·) F3(x3) F3(·) F4(x4) F4(·) F5(x5) F5(·) F6(x6) F6(·) F7(x7) F7(·) F8(x8) F8(·) F9(x9) F9(·) learns nothing about xi’s all other Fi(x∗) look random achieved very efficiently from OT extension
Alice Bob
a b c d c d e f
Alice Bob m bins
1 2 3 4 5 6 7 8 9 10
a b c d c d e f
h1, h2 : {0, 1}∗ → [m]
Alice Bob m bins
1 2 3 4 5 6 7 8 9 10
a b c d c d e f
h1(a) h2(a)
h1, h2 : {0, 1}∗ → [m]
Alice Bob m bins
1 2 3 4 5 6 7 8 9 10
a b c d c d e f
h1(b) h2(b)
h1, h2 : {0, 1}∗ → [m]
Alice Bob m bins
1 2 3 4 5 6 7 8 9 10
a b c d c d e f
h1, h2 : {0, 1}∗ → [m]
Alice Bob m bins
1 2 3 4 5 6 7 8 9 10
a b c d c d e f a c d b
h1, h2 : {0, 1}∗ → [m]
bin h1(x) or h2(x)
Alice Bob m bins
1 2 3 4 5 6 7 8 9 10
a b c d c d e f a c d b c, e d e f c, d f
h1, h2 : {0, 1}∗ → [m]
bin h1(x) or h2(x)
bins h1(x) and h2(x)
Alice Bob m bins
1 2 3 4 5 6 7 8 9 10
a b c d c d e f
F2(a) F3(c) F7(d) F9(b)
c, e d e f c, d f
F1(·) F2(·) F3(·) F4(·) F5(·) F6(·) F7(·) F8(·) F9(·) F10(·)
h1, h2 : {0, 1}∗ → [m]
bin h1(x) or h2(x)
bins h1(x) and h2(x)
Alice learns one Fi(x); Bob learns entire Fi(·)
Alice Bob m bins
1 2 3 4 5 6 7 8 9 10
a b c d c d e f
F2(a) F3(c) F7(d) F9(b)
c, e d e f c, d f
F1(·) F2(·) F3(·) F4(·) F5(·) F6(·) F7(·) F8(·) F9(·) F10(·)
h1, h2 : {0, 1}∗ → [m]
bin h1(x) or h2(x)
bins h1(x) and h2(x)
Alice learns one Fi(x); Bob learns entire Fi(·)
Alice Bob m bins
1 2 3 4 5 6 7 8 9 10
a b c d c d e f
F2(a) F3(c) F7(d) F9(b)
c, e d e f c, d f
F1(·) F2(·) F3(·) F4(·) F5(·) F6(·) F7(·) F8(·) F9(·) F10(·)
h1, h2 : {0, 1}∗ → [m]
bin h1(x) or h2(x)
bins h1(x) and h2(x)
Alice learns one Fi(x); Bob learns entire Fi(·)
Alice Bob m bins
1 2 3 4 5 6 7 8 9 10
a b c d c d e f
F2(a) F3(c) F7(d) F9(b)
c, e d e f c, d f
F1(·) F2(·) F3(·) F4(·) F5(·) F6(·) F7(·) F8(·) F9(·) F10(·)
h1, h2 : {0, 1}∗ → [m]
bin h1(x) or h2(x)
bins h1(x) and h2(x)
Alice learns one Fi(x); Bob learns entire Fi(·)
Alice Bob m bins
1 2 3 4 5 6 7 8 9 10
a b c d c d e f
F2(a) F3(c) F7(d) F9(b)
c, e d e f c, d f
F1(·) F2(·) F3(·) F4(·) F5(·) F6(·) F7(·) F8(·) F9(·) F10(·)
h1, h2 : {0, 1}∗ → [m]
bin h1(x) or h2(x)
bins h1(x) and h2(x)
Alice learns one Fi(x); Bob learns entire Fi(·)
Alice Bob m bins
1 2 3 4 5 6 7 8 9 10
a b c d c d e f
F2(a) F3(c) F7(d) F9(b)
c, e d e f c, d f
F1(·) F2(·) F3(·) F4(·) F5(·) F6(·) F7(·) F8(·) F9(·) F10(·)
h1, h2 : {0, 1}∗ → [m]
bin h1(x) or h2(x)
bins h1(x) and h2(x)
Alice learns one Fi(x); Bob learns entire Fi(·)
Alice Bob
1 2 3 4 5 6 7 8 9 10
c d e f c, e d e f c, d f
F1(·) F2(·) F3(·) F4(·) F5(·) F6(·) F7(·) F8(·) F9(·) F10(·)
Alice Bob
1 2 3 4 5 6 7 8 9 10
c d e f c, e d e f c, d f
F1(·) F2(·) F3(·) F4(·) F5(·) F6(·) F7(·) F8(·) F9(·) F10(·)
F-values per item
Alice Bob
1 2 3 4 5 6 7 8 9 10
c d e f c, e d e f c, d f
F1(·) F2(·) F3(·) F4(·) F5(·) F6(·) F7(·) F8(·) F9(·) F10(·)
F-values per item , what if he sends only one?
Alice Bob
1 2 3 4 5 6 7 8 9 10
c
F-values per item , what if he sends only one? Alice has c; does she include it in output?
Alice Bob
1 2 3 4 5 6 7 8 9 10
c
F3(c)
F-values per item , what if he sends only one? Alice has c; does she include it in output?
Alice Bob
1 2 3 4 5 6 7 8 9 10
c
F3(c)
F-values per item , what if he sends only one? Alice has c; does she include it in output?
Alice Bob
1 2 3 4 5 6 7 8 9 10
c
F7(c)
F-values per item , what if he sends only one? Alice has c; does she include it in output?
Alice Bob
1 2 3 4 5 6 7 8 9 10
c
F7(c)
Bob should send two F-values per item , what if he sends only one? Alice has c; does she include it in output? Only if c placed in bin 3!
Alice Bob
1 2 3 4 5 6 7 8 9 10
c
F-values per item , what if he sends only one? Alice has c; does she include it in output? Only if c placed in bin 3!
◮ Depends on Alice’s
entire input! ⇒ can’t simulate!
Alice Bob
1 2 3 4 5 6 7 8 9 . . .
F1(x1) F1(·) F2(x2) F2(·) F3(x3) F3(·) F4(x4) F4(·) F5(x5) F5(·) F6(x6) F6(·) F7(x7) F7(·) F8(x8) F8(·) F9(x9) F9(·)
Alice Bob
1 2 3 4 5 6 7 8 9 . . .
F1(x1) F1(·) F2(x2) F2(·) F3(x3) F3(·) F4(x4) F4(·) F5(x5) F5(·) F6(x6) F6(·) F7(x7) F7(·) F8(x8) F8(·) F9(x9) F9(·) State of the art malicious batch OPRF [OOS17]
◮ essentially same cost as semi-honest
Alice Bob
1 2 3 4 5 6 7 8 9 . . .
F1(x1) F1(·) F2(x2) F2(·) F3(x3) F3(·) F4(x4) F4(·) F5(x5) F5(·) F6(x6) F6(·) F7(x7) F7(·) F8(x8) F8(·) F9(x9) F9(·) State of the art malicious batch OPRF [OOS17]
◮ essentially same cost as semi-honest ◮ consistency check relies on an additive homomorphism:
∗: a gross oversimplification
Alice Bob
1 2 3 4 5 6 7 8 9 10
a b c d c d e f
Alice Bob
1 2 3 4 5 6 7 8 9 10
a b c d c d e f
Alice Bob
1 2 3 4 5 6 7 8 9 10
a b c d
s2 ⊕ s7 =
c d e f
s2 s7 Alice secret-shares x into bins h1(x) and h2(x)
Alice Bob
1 2 3 4 5 6 7 8 9 10
a b c d
s2 ⊕ s7 =
c d e f
s2 s7 Alice secret-shares x into bins h1(x) and h2(x)
Alice Bob
1 2 3 4 5 6 7 8 9 10
a b c d
s2 ⊕ s7 = s3 ⊕ s9 =
c d e f
s2 s7 s3 s9 Alice secret-shares x into bins h1(x) and h2(x)
Alice Bob
1 2 3 4 5 6 7 8 9 10
a b c d
s2 ⊕ s7 = s3 ⊕ s9 = s3 ⊕ s7 = s4 ⊕ s7 =
c d e f
s2 s7 s3 s9 s1 s4 s5 s6 s8 s10 Alice secret-shares x into bins h1(x) and h2(x)
Alice Bob
1 2 3 4 5 6 7 8 9 10
a b c d
s2 ⊕ s7 = s3 ⊕ s9 = s3 ⊕ s7 = s4 ⊕ s7 =
c d e f
F1(s1) F2(s2) F3(s3) F4(s4) F5(s5) F6(s6) F7(s7) F8(s8) F9(s9) F10(s10) F1(·) F2(·) F3(·) F4(·) F5(·) F6(·) F7(·) F8(·) F9(·) F10(·) Alice secret-shares x into bins h1(x) and h2(x)
Alice Bob
1 2 3 4 5 6 7 8 9 10
a b c d
s2 ⊕ s7 = s3 ⊕ s9 = s3 ⊕ s7 = s4 ⊕ s7 =
c d e f
F1(s1) F2(s2) F3(s3) F4(s4) F5(s5) F6(s6) F7(s7) F8(s8) F9(s9) F10(s10) F2(s2) ⊕ F7(s7) = F27(a) F1(·) F2(·) F3(·) F4(·) F5(·) F6(·) F7(·) F8(·) F9(·) F10(·) Alice secret-shares x into bins h1(x) and h2(x)
Alice Bob
1 2 3 4 5 6 7 8 9 10
a b c d
s2 ⊕ s7 = s3 ⊕ s9 = s3 ⊕ s7 = s4 ⊕ s7 =
c d e f
F1(s1) F2(s2) F3(s3) F4(s4) F5(s5) F6(s6) F7(s7) F8(s8) F9(s9) F10(s10) F2(s2) ⊕ F7(s7) = F27(a) F3(s3) ⊕ F9(s9) = F39(b) F1(·) F2(·) F3(·) F4(·) F5(·) F6(·) F7(·) F8(·) F9(·) F10(·) Alice secret-shares x into bins h1(x) and h2(x)
Alice Bob
1 2 3 4 5 6 7 8 9 10
a b c d
s2 ⊕ s7 = s3 ⊕ s9 = s3 ⊕ s7 = s4 ⊕ s7 =
c d e f
F1(s1) F2(s2) F3(s3) F4(s4) F5(s5) F6(s6) F7(s7) F8(s8) F9(s9) F10(s10) F2(s2) ⊕ F7(s7) = F27(a) F3(s3) ⊕ F9(s9) = F39(b) F3(s3) ⊕ F7(s7) = F37(c) F4(s4) ⊕ F7(s7) = F47(d) F1(·) F2(·) F3(·) F4(·) F5(·) F6(·) F7(·) F8(·) F9(·) F10(·) Alice secret-shares x into bins h1(x) and h2(x)
Alice Bob
1 2 3 4 5 6 7 8 9 10
a b c d
s2 ⊕ s7 = s3 ⊕ s9 = s3 ⊕ s7 = s4 ⊕ s7 =
c d e f
F1(s1) F2(s2) F3(s3) F4(s4) F5(s5) F6(s6) F7(s7) F8(s8) F9(s9) F10(s10) F2(s2) ⊕ F7(s7) = F27(a) F3(s3) ⊕ F9(s9) = F39(b) F3(s3) ⊕ F7(s7) = F37(c) F4(s4) ⊕ F7(s7) = F47(d) F1(·) F2(·) F3(·) F4(·) F5(·) F6(·) F7(·) F8(·) F9(·) F10(·) Alice secret-shares x into bins h1(x) and h2(x)
Alice Bob
1 2 3 4 5 6 7 8 9 10
a b c d
s2 ⊕ s7 = s3 ⊕ s9 = s3 ⊕ s7 = s4 ⊕ s7 =
c d e f
F1(s1) F2(s2) F3(s3) F4(s4) F5(s5) F6(s6) F7(s7) F8(s8) F9(s9) F10(s10) F2(s2) ⊕ F7(s7) = F27(a) F3(s3) ⊕ F9(s9) = F39(b) F3(s3) ⊕ F7(s7) = F37(c) F4(s4) ⊕ F7(s7) = F47(d) F1(·) F2(·) F3(·) F4(·) F5(·) F6(·) F7(·) F8(·) F9(·) F10(·)
bins h1(x) and h2(x)
Alice Bob
1 2 3 4 5 6 7 8 9 10
a b c d
s2 ⊕ s7 = s3 ⊕ s9 = s3 ⊕ s7 = s4 ⊕ s7 =
c d e f
F1(s1) F2(s2) F3(s3) F4(s4) F5(s5) F6(s6) F7(s7) F8(s8) F9(s9) F10(s10) F2(s2) ⊕ F7(s7) = F27(a) F3(s3) ⊕ F9(s9) = F39(b) F3(s3) ⊕ F7(s7) = F37(c) F4(s4) ⊕ F7(s7) = F47(d) F1(·) F2(·) F3(·) F4(·) F5(·) F6(·) F7(·) F8(·) F9(·) F10(·)
bins h1(x) and h2(x)
Alice Bob
1 2 3 4 5 6 7 8 9 10
a b c d
s2 ⊕ s7 = s3 ⊕ s9 = s3 ⊕ s7 = s4 ⊕ s7 =
c d e f
F1(s1) F2(s2) F3(s3) F4(s4) F5(s5) F6(s6) F7(s7) F8(s8) F9(s9) F10(s10) F2(s2) ⊕ F7(s7) = F27(a) F3(s3) ⊕ F9(s9) = F39(b) F3(s3) ⊕ F7(s7) = F37(c) F4(s4) ⊕ F7(s7) = F47(d) F1(·) F2(·) F3(·) F4(·) F5(·) F6(·) F7(·) F8(·) F9(·) F10(·)
bins h1(x) and h2(x) Bob sends only one F-value per item
Alice Bob
1 2 3 4 5 6 7 8 9 10
a b c d
s2 ⊕ s7 = s3 ⊕ s9 = s3 ⊕ s7 = s4 ⊕ s7 =
c d e f
F1(s1) F2(s2) F3(s3) F4(s4) F5(s5) F6(s6) F7(s7) F8(s8) F9(s9) F10(s10) F2(s2) ⊕ F7(s7) = F27(a) F3(s3) ⊕ F9(s9) = F39(b) F3(s3) ⊕ F7(s7) = F37(c) F4(s4) ⊕ F7(s7) = F47(d) F1(·) F2(·) F3(·) F4(·) F5(·) F6(·) F7(·) F8(·) F9(·) F10(·)
bins h1(x) and h2(x) Bob sends only one F-value per item
s1 s2 s3 s4 s5 s6 s7 s8 s9 s10
a b c d
s2 ⊕ s7 = s3 ⊕ s9 = s3 ⊕ s7 = s4 ⊕ s7 =
– – – – – – – – – –
a b c d
s2 ⊕ s7 = s3 ⊕ s9 = s3 ⊕ s7 = s4 ⊕ s7 =
– s2 – – – – – – – –
a b c d
s2 ⊕ s7 = s3 ⊕ s9 = s3 ⊕ s7 = s4 ⊕ s7 = algorithm: set one location arbitrarily
– s2 – – – – – – – –
a b c d
s2 ⊕ s7 = s3 ⊕ s9 = s3 ⊕ s7 = s4 ⊕ s7 = algorithm: set one location arbitrarily find item with one unset location
– s2 – – – – s7 – – –
a b c d
s2 ⊕ s7 = s3 ⊕ s9 = s3 ⊕ s7 = s4 ⊕ s7 = algorithm: set one location arbitrarily find item with one unset location solve for that unset location
– s2 – – – – s7 – – –
a b c d
s2 ⊕ s7 = s3 ⊕ s9 = s3 ⊕ s7 = s4 ⊕ s7 = algorithm: set one location arbitrarily repeat: find item with one unset location solve for that unset location
– s2 s3 – – – s7 – – –
a b c d
s2 ⊕ s7 = s3 ⊕ s9 = s3 ⊕ s7 = s4 ⊕ s7 = algorithm: set one location arbitrarily repeat: find item with one unset location solve for that unset location
– s2 s3 – – – s7 – – –
a b c d
s2 ⊕ s7 = s3 ⊕ s9 = s3 ⊕ s7 = s4 ⊕ s7 = algorithm: set one location arbitrarily repeat: find item with one unset location solve for that unset location
– s2 s3 – – – s7 – s9 –
a b c d
s2 ⊕ s7 = s3 ⊕ s9 = s3 ⊕ s7 = s4 ⊕ s7 = algorithm: set one location arbitrarily repeat: find item with one unset location solve for that unset location
– s2 s3 – – – s7 – s9 –
a b c d
s2 ⊕ s7 = s3 ⊕ s9 = s3 ⊕ s7 = s4 ⊕ s7 = algorithm: set one location arbitrarily repeat: find item with one unset location solve for that unset location
– s2 s3 s4 – – s7 – s9 –
a b c d
s2 ⊕ s7 = s3 ⊕ s9 = s3 ⊕ s7 = s4 ⊕ s7 = algorithm: set one location arbitrarily repeat: find item with one unset location solve for that unset location
s1 s2 s3 s4 s5 s6 s7 s8 s9 s10
a b c d
s2 ⊕ s7 = s3 ⊕ s9 = s3 ⊕ s7 = s4 ⊕ s7 = algorithm: set one location arbitrarily repeat: find item with one unset location solve for that unset location
s1 s2 s3 s4 s5 s6 s7 s8 s9 s10
a b c d
s2 ⊕ s7 = s3 ⊕ s9 = s3 ⊕ s7 = s4 ⊕ s7 =
algorithm: set one location arbitrarily repeat: find item with one unset location solve for that unset location
s1 s2 s3 s4 s5 s6 s7 s8 s9 s10
a b c d
s2 ⊕ s7 = s3 ⊕ s9 = s3 ⊕ s7 = s4 ⊕ s7 =
s1 s2 s3 s4 s5 s6 s7 s8 s9 s10
a b c d
Encode encode so that for all x:
s1 s2 s3 s4 s5 s6 s7 s8 s9 s10
a b c d
Encode encode so that for all x:
s1 s2 s3 s4 s5 s6 s7 s8 s9 s10
a b c d
Encode encode so that for all x:
s1 s2 s3 s4 s5 s6 s7 s8 s9 s10
a b c d
Encode encode so that for all x:
s| = number of OPRFs = communication cost of PSI, ideally O(# items)
s1 s2 s3 s4 s5 s6 s7 s8 s9 s10
a b c d
Encode encode so that for all x:
s| = number of OPRFs = communication cost of PSI, ideally O(# items)
s.
secret-shared cuckoo idea:
◮ requires acyclic cuckoo graph ◮ failure probability too high
secret-shared cuckoo idea:
◮ requires acyclic cuckoo graph ◮ failure probability too high
probe each position with probability 0.5:
◮ n items vector of size n + λ ◮ expensive O(n3) encoding
secret-shared cuckoo idea:
◮ requires acyclic cuckoo graph ◮ failure probability too high
probe each position with probability 0.5:
◮ n items vector of size n + λ ◮ expensive O(n3) encoding
garbled bloom filter [DCW13]:
◮ n items vector of size λn
secret-shared cuckoo idea:
◮ requires acyclic cuckoo graph ◮ failure probability too high
probe each position with probability 0.5:
◮ n items vector of size n + λ ◮ expensive O(n3) encoding
garbled bloom filter [DCW13]:
◮ n items vector of size λn
new garbled cuckoo PaXoS:
◮ n items vector of size ∼ 2.4n ◮ fast encoding: O(nλ)
s1 s2 s3 s4 s5 s6 s7 s8 s9 s10
a b c d e
for each item x:
◮ probe positions h1(x) and h2(x)
s1 s2 s3 s4 s5 s6 s7 s8 s9 s10
a b c d e
for each item x:
◮ probe positions h1(x) and h2(x)
s1 s2 s3 s4 s5 s6 s7 s8 s9 s10 s11 s12 . . . s10+k k aux positions
a b c d e
for each item x:
◮ probe positions h1(x) and h2(x)
s1 s2 s3 s4 s5 s6 s7 s8 s9 s10 s11 s12 . . . s10+k k aux positions
a b c d e
for each item x:
◮ probe positions h1(x) and h2(x) ◮ probe random subset of aux positions
s1 s2 s3 s4 s5 s6 s7 s8 s9 s10 s11 s12 . . . s10+k k
b c d e
for each item x:
◮ probe positions h1(x) and h2(x) ◮ probe random subset of aux positions
s1 s2 s3 s4 s5 s6 s7 s8 s9 s10 s11 s12 . . . s10+k k
b c d e
for each item x:
◮ probe positions h1(x) and h2(x) ◮ probe random subset of aux positions
s1 s2 s3 s4 s5 s6 s7 s8 s9 s10 s11 s12 . . . s10+k k
b c d e
for each item x:
◮ probe positions h1(x) and h2(x) ◮ probe random subset of aux positions
◮ solve linear system for the cycle items
s1 s2 s3 s4 s5 s6 s7 s8 s9 s10 s11 s12 . . . s10+k k
b c d e
for each item x:
◮ probe positions h1(x) and h2(x) ◮ probe random subset of aux positions
◮ solve linear system for the cycle items ◮ solution exists whp if k > [# cycle items] + λ
s1 s2 s3 s4 s5 s6 s7 s8 s9 s10 s11 s12 . . . s10+k k
b c d e
◮ probe positions h1(x) and h2(x) ◮ probe random subset of aux positions
◮ solve linear system for the cycle items ◮ solution exists whp if k > [# cycle items] + λ ◮ can be found in [# cycle items]3 time
s1 s2 s3 s4 s5 s6 s7 s8 s9 s10 s11 s12 . . . s10+k k
b c d e
◮ probe positions h1(x) and h2(x) ◮ probe random subset of aux positions
◮ solve linear system for the cycle items ◮ solution exists whp if k > [# cycle items] + λ ◮ can be found in [# cycle items]3 time
s1 s2 s3 s4 s5 s6 s7 s8 s9 s10 s11 s12 . . . s10+k k
b c d e
◮ probe positions h1(x) and h2(x) ◮ probe random subset of aux positions
◮ solve linear system for the cycle items ◮ solution exists whp if k > [# cycle items] + λ ◮ can be found in [# cycle items]3 time
s1 s2 s3 s4 s5 s6 s7 s8 s9 s10 s11 s12 . . . s10+k k
b c d e
◮ probe positions h1(x) and h2(x) ◮ probe random subset of aux positions
◮ solve linear system for the cycle items ◮ solution exists whp if k > [# cycle items] + λ ◮ can be found in [# cycle items]3 time
◮ remaining cuckoo graph is acyclic
s1 s2 s3 s4 s5 s6 s7 s8 s9 s10 s11 s12 . . . s10+k k
b c d e
◮ probe positions h1(x) and h2(x) ◮ probe random subset of aux positions
◮ solve linear system for the cycle items ◮ solution exists whp if k > [# cycle items] + λ ◮ can be found in [# cycle items]3 time
◮ remaining cuckoo graph is acyclic
s1 s2 s3 s4 s5 s6 s7 s8 s9 s10 s11 s12 . . . s10+k k
b c d e
◮ probe positions h1(x) and h2(x) ◮ probe random subset of aux positions
◮ solve linear system for the cycle items ◮ solution exists whp if k > [# cycle items] + λ ◮ can be found in [# cycle items]3 time
◮ remaining cuckoo graph is acyclic
s1 s2 s3 s4 s5 s6 s7 s8 s9 s10 s11 s12 . . . s10+k k
a b c d e
◮ probe positions h1(x) and h2(x) ◮ probe random subset of aux positions
◮ solve linear system for the cycle items ◮ solution exists whp if k > [# cycle items] + λ ◮ can be found in [# cycle items]3 time
◮ remaining cuckoo graph is acyclic
s1 s2 s3 s4 s5 s6 s7 s8 s9 s10 s11 s12 . . . s10+k k
a b c d e
◮ probe positions h1(x) and h2(x) ◮ probe random subset of aux positions
◮ solve linear system for the cycle items ◮ solution exists whp if k > [# cycle items] + λ ◮ can be found in [# cycle items]3 time
◮ remaining cuckoo graph is acyclic
whp: [# cycle items] is O(log n)
20 22 24 26 28 210 212 24 26 28 210 212 214
PRTY19 KKRT16 classic DH RR17b RR17a DKT10 this work
insecure hashing running time (s) communication (MB)
new approach for malicious PSI:
◮ fastest, least communication ◮ first O(n) from OT extension ◮ almost as efficient as
semi-honest PaXoS data structure:
◮ encode items into a vector ◮ lookup is XOR of some
positions
◮ first linear-time, constant rate
construction