1
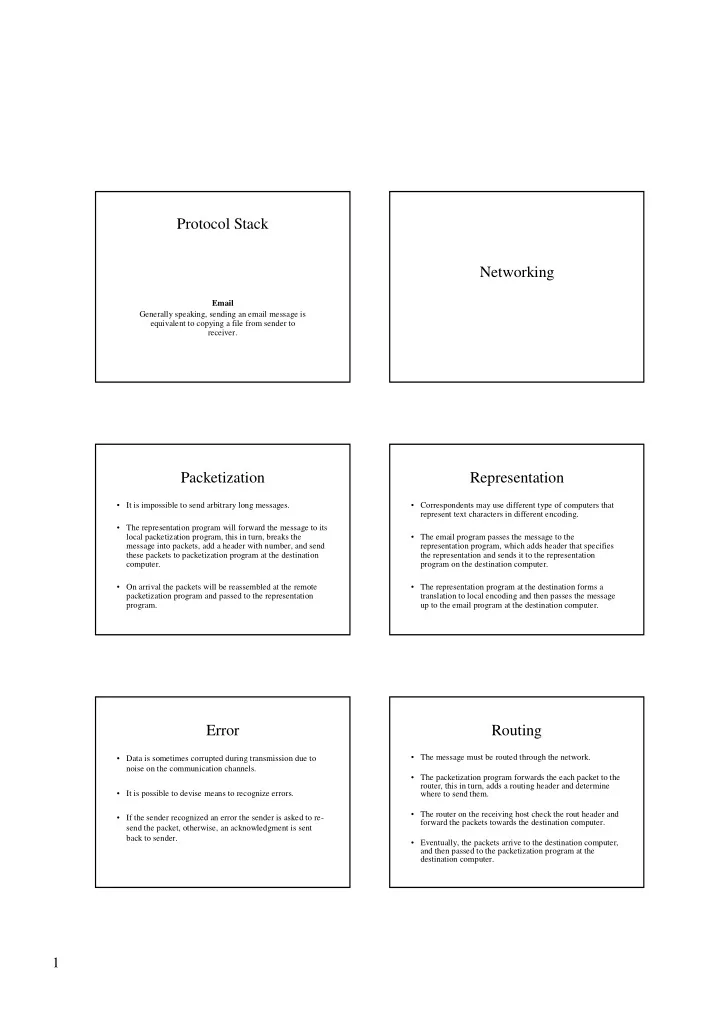
Networking Protocol Stack
Email Generally speaking, sending an email message is equivalent to copying a file from sender to receiver.
Representation
- Correspondents may use different type of computers that
represent text characters in different encoding.
- The email program passes the message to the
representation program, which adds header that specifies the representation and sends it to the representation program on the destination computer.
- The representation program at the destination forms a
translation to local encoding and then passes the message up to the email program at the destination computer.
Packetization
- It is impossible to send arbitrary long messages.
- The representation program will forward the message to its
local packetization program, this in turn, breaks the message into packets, add a header with number, and send these packets to packetization program at the destination computer.
- On arrival the packets will be reassembled at the remote
packetization program and passed to the representation program.
Routing
- The message must be routed through the network.
- The packetization program forwards the each packet to the
router, this in turn, adds a routing header and determine where to send them.
- The router on the receiving host check the rout header and
forward the packets towards the destination computer.
- Eventually, the packets arrive to the destination computer,
and then passed to the packetization program at the destination computer.
Error
- Data is sometimes corrupted during transmission due to
noise on the communication channels.
- It is possible to devise means to recognize errors.
- If the sender recognized an error the sender is asked to re-