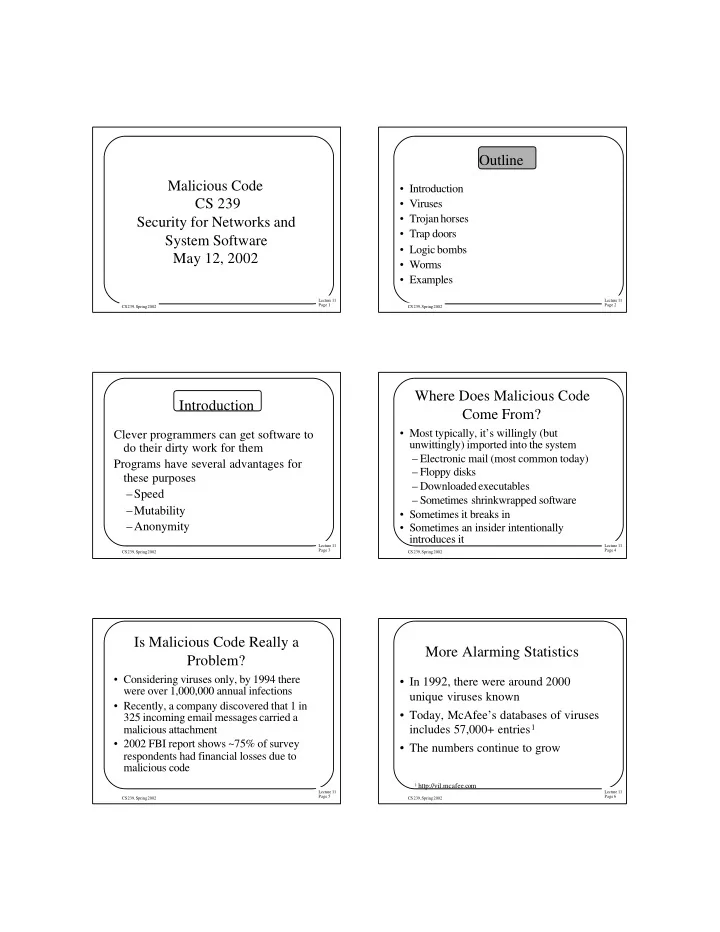
Lecture 11 Page 1 CS 239, Spring 2002
Malicious Code CS 239 Security for Networks and System Software May 12, 2002
Lecture 11 Page 2 CS 239, Spring 2002
Outline
- Introduction
- Viruses
- Trojan horses
- Trap doors
- Logic bombs
- Worms
- Examples
Lecture 11 Page 3 CS 239, Spring 2002
Introduction
Clever programmers can get software to do their dirty work for them Programs have several advantages for these purposes –Speed –Mutability –Anonymity
Lecture 11 Page 4 CS 239, Spring 2002
Where Does Malicious Code Come From?
- Most typically, it’s willingly (but
unwittingly) imported into the system – Electronic mail (most common today) – Floppy disks – Downloaded executables – Sometimes shrinkwrapped software
- Sometimes it breaks in
- Sometimes an insider intentionally
introduces it
Lecture 11 Page 5 CS 239, Spring 2002
Is Malicious Code Really a Problem?
- Considering viruses only, by 1994 there
were over 1,000,000 annual infections
- Recently, a company discovered that 1 in
325 incoming email messages carried a malicious attachment
- 2002 FBI report shows ~75% of survey
respondents had financial losses due to malicious code
Lecture 11 Page 6 CS 239, Spring 2002
More Alarming Statistics
- In 1992, there were around 2000
unique viruses known
- Today, McAfee’s databases of viruses
includes 57,000+ entries1
- The numbers continue to grow
1 http://vil.mcafee.com