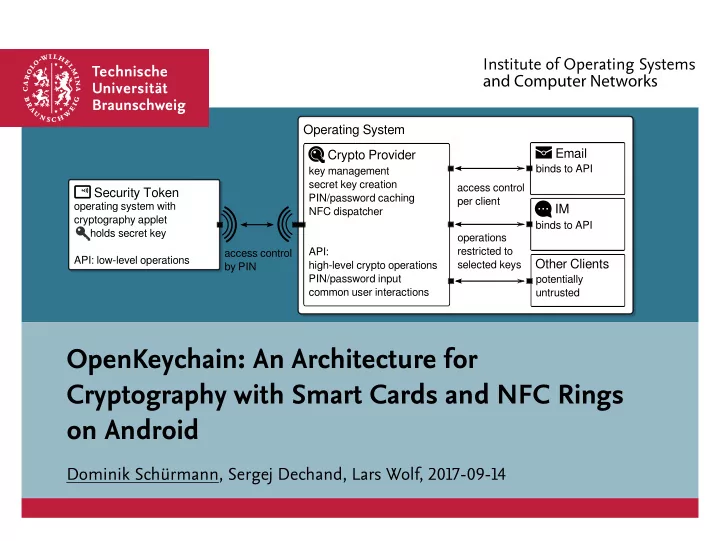
Operating System Crypto Provider Email IM
access control per client
Other Clients
access control by PIN key management secret key creation PIN/password caching NFC dispatcher API: high-level crypto operations PIN/password input common user interactions
Security Token
- perating system with
cryptography applet holds secret key API: low-level operations binds to API binds to API potentially untrusted
- perations
restricted to selected keys
OpenKeychain: An Architecture for Cryptography with Smart Cards and NFC Rings
- n Android