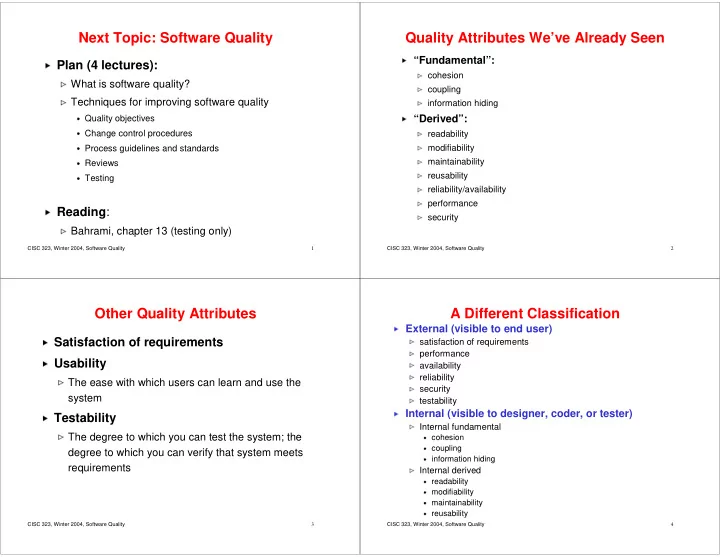
CISC 323, Winter 2004, Software Quality 1
Next Topic: Software Quality
- Plan (4 lectures):
What is software quality?
✁Techniques for improving software quality
✂Quality objectives
✂Change control procedures
✂Process guidelines and standards
✂Reviews
✂Testing
✄Reading:
☎Bahrami, chapter 13 (testing only)
CISC 323, Winter 2004, Software Quality 2
Quality Attributes We’ve Already Seen
✆“Fundamental”:
✝cohesion
✝coupling
✝information hiding
✞“Derived”:
✝readability
✝modifiability
✝maintainability
✝reusability
✝reliability/availability
✝performance
✝security
CISC 323, Winter 2004, Software Quality 3
Other Quality Attributes
✟Satisfaction of requirements
✟Usability
✠The ease with which users can learn and use the system
✟Testability
✠The degree to which you can test the system; the degree to which you can verify that system meets requirements
CISC 323, Winter 2004, Software Quality 4
A Different Classification
✡External (visible to end user)
☛satisfaction of requirements
☛performance
☛availability
☛reliability
☛security
☛testability
✡Internal (visible to designer, coder, or tester)
☛Internal fundamental
☞cohesion
☞coupling
☞information hiding
✌Internal derived
☞readability
☞modifiability
☞maintainability
☞reusability