May 12, 2005 ECS 153, Introduction to Computer Security Slide #1
Models
- Extreme programming
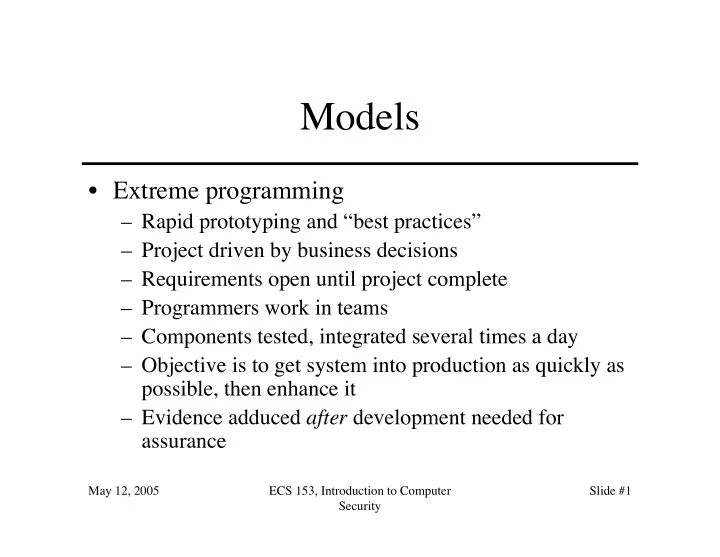
Models Extreme programming Rapid prototyping and best practices - - PowerPoint PPT Presentation
Models Extreme programming Rapid prototyping and best practices Project driven by business decisions Requirements open until project complete Programmers work in teams Components tested, integrated several times a
May 12, 2005 ECS 153, Introduction to Computer Security Slide #1
May 12, 2005 ECS 153, Introduction to Computer Security Slide #2
May 12, 2005 ECS 153, Introduction to Computer Security Slide #3
May 12, 2005 ECS 153, Introduction to Computer Security Slide #4
May 12, 2005 ECS 153, Introduction to Computer Security Slide #5
May 12, 2005 ECS 153, Introduction to Computer Security Slide #6
May 12, 2005 ECS 153, Introduction to Computer Security Slide #7
May 12, 2005 ECS 153, Introduction to Computer Security Slide #8
– SV/MLS added separate table for MAC labels, DAC permissions
– SVR4.1ES defined new inode structure
May 12, 2005 ECS 153, Introduction to Computer Security Slide #9
May 12, 2005 ECS 153, Introduction to Computer Security Slide #10
May 12, 2005 ECS 153, Introduction to Computer Security Slide #11
May 12, 2005 ECS 153, Introduction to Computer Security Slide #12
May 12, 2005 ECS 153, Introduction to Computer Security Slide #13
May 12, 2005 ECS 153, Introduction to Computer Security Slide #14
May 12, 2005 ECS 153, Introduction to Computer Security Slide #15
– Also called propagating Trojan horse – Early version of animal game used this to delete copies of itself
– 1976: Karger and Schell suggested modifying compiler to include Trojan horse that copied itself into specific programs including later version of the compiler – 1980s: Thompson implements this
May 12, 2005 ECS 153, Introduction to Computer Security Slide #16
May 12, 2005 ECS 153, Introduction to Computer Security Slide #17
login source correct compiler login executable user password login source doctored compiler login executable magic password user password or logged in logged in
May 12, 2005 ECS 153, Introduction to Computer Security Slide #18
compiler source correct compiler compiler executable login source compiler source doctored compiler compiler executable correct login executable login source rigged login executable
May 12, 2005 ECS 153, Introduction to Computer Security Slide #19
– Finally deleted when a new compiler executable from a different system
protect you from using untrusted code
– Also: having source code helps, but does not ensure you’re safe
May 12, 2005 ECS 153, Introduction to Computer Security Slide #20
action
– Insertion phase is inserting itself into file – Execution phase is performing some (possibly null) action
– Need not always be executed – Lehigh virus inserted itself into boot file only if boot file not infected
May 12, 2005 ECS 153, Introduction to Computer Security Slide #21
beginvirus: if spread-condition then begin for some set of target files do begin if target is not infected then begin determine where to place virus instructions copy instructions from beginvirus to endvirus into target alter target to execute added instructions end; end; end; perform some action(s) goto beginning of infected program endvirus:
May 12, 2005 ECS 153, Introduction to Computer Security Slide #22
– Overt action = infected program’s actions – Covert action = virus’ actions (infect, execute)
– Overt purpose = virus’ actions (infect, execute) – Covert purpose = none
– Defenses against Trojan horse also inhibit computer viruses
May 12, 2005 ECS 153, Introduction to Computer Security Slide #23
May 12, 2005 ECS 153, Introduction to Computer Security Slide #24
– Max time 60m, min time 5m, average 30m – Virus small, so no degrading of response time – Virus tagged, so it could be removed quickly
– Implemented simple security property of Bell-LaPadula – As writing not inhibited (no *-property enforcement), viruses spread easily
May 12, 2005 ECS 153, Introduction to Computer Security Slide #25
May 12, 2005 ECS 153, Introduction to Computer Security Slide #26
May 12, 2005 ECS 153, Introduction to Computer Security Slide #27
May 12, 2005 ECS 153, Introduction to Computer Security Slide #28
– Section of disk containing code – Executed when system first “sees” the disk
– Moves disk interrupt vector from 13H to 6DH – Sets new interrupt vector to invoke Brain virus – When new floppy seen, check for 1234H at location 4
May 12, 2005 ECS 153, Introduction to Computer Security Slide #29
Header Executable code and data 100 1000 Header Executable code and data 100 1000 1100 Virus code 200 First program instruction to be executed
May 12, 2005 ECS 153, Introduction to Computer Security Slide #30
– Checks if system infected
– Checks date
then run program
– Then: check all calls asking files to be executed
– Error: doesn’t set signature when .EXE executes
May 12, 2005 ECS 153, Introduction to Computer Security Slide #31
May 12, 2005 ECS 153, Introduction to Computer Security Slide #32
May 12, 2005 ECS 153, Introduction to Computer Security Slide #33
May 12, 2005 ECS 153, Introduction to Computer Security Slide #34
Virus code Enciphered virus code Deciphering routine Deciphering key
May 12, 2005 ECS 153, Introduction to Computer Security Slide #35
(* Decryption code of the 1260 virus *) (* initialize the registers with the keys *) rA = k1; rB = k2; (* initialize rC with the virus; starts at sov, ends at eov *) rC = sov; (* the encipherment loop *) while (rC != eov) do begin (* encipher the byte of the message *) (*rC) = (*rC) xor rA xor rB; (* advance all the counters *) rC = rC + 1; rA = rA + 1; end
May 12, 2005 ECS 153, Introduction to Computer Security Slide #36
May 12, 2005 ECS 153, Introduction to Computer Security Slide #37
the same effect:
– add 0 to register – subtract 0 from register – xor 0 with register – no-op
instructions