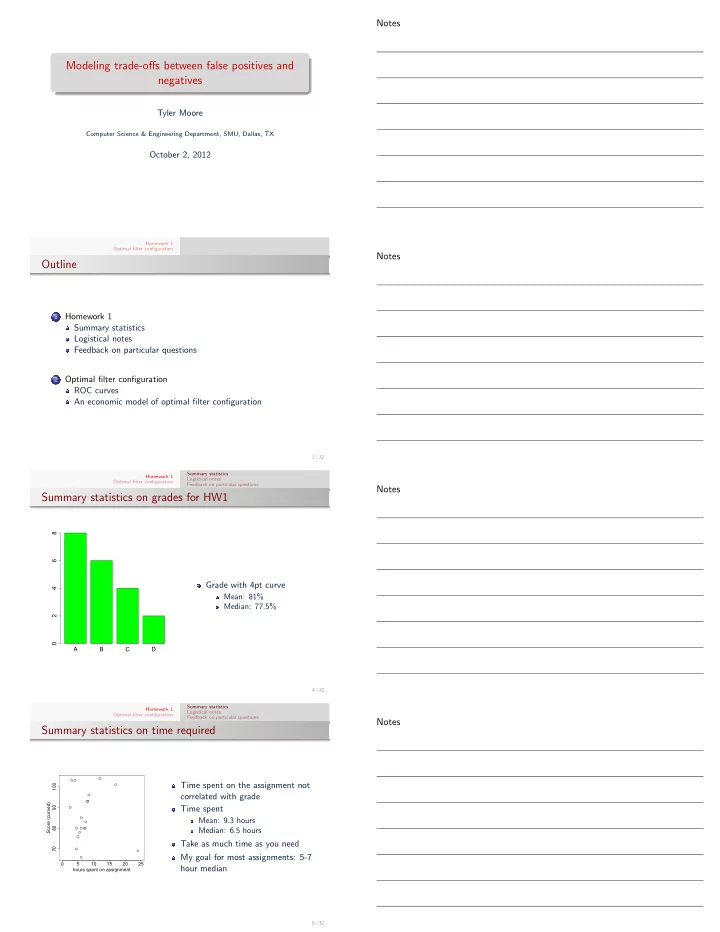
SLIDE 4 Homework 1 Optimal filter configuration Summary statistics Logistical notes Feedback on particular questions
Threat models
Sarah Palin’s email: http://www.schneier.com/blog/ archives/2008/09/sarah_palins_e-.html Matt Honan’s cloud deletion: http://www.schneier.com/ blog/archives/2008/09/sarah_palins_e-.html Middleperson bank fraud: http://www.schneier.com/ blog/archives/2012/09/man-in-the-midd_5.html
14 / 32 Homework 1 Optimal filter configuration Summary statistics Logistical notes Feedback on particular questions
Q7
One of the primary motivations for the failed Cybersecurity Act
- f 2012 was the view that many critical infrastructure
- perators weren’t investing enough to protect against the risk
- f attack. In particular, there were concerns that the industrial
control systems used to manage heavy industry such as power plants and refineries are inadequately protected against attacks seeking to disrupt operations. Your task is to briefly (in approximately 300 words) present both sides of the argument. First, present any available evidence that industrial control systems are being adequately
- protected. Second, present an economic argument that the
systems are not being protected enough. In particular, explain which market failures, if any, might explain why there has been underinvestment in security. Finally, conclude by briefly explaining which argument you find more convincing and why.
15 / 32 Homework 1 Optimal filter configuration Summary statistics Logistical notes Feedback on particular questions
Q7
Points in favor of adequate security:
1 Very few realized attacks 2 Reputational damage of an attack would be harsh
Points against adequate security:
1 Security is difficult for consumers to observe (even if they are
willing to pay for it)
2 Security as public good 3 Externalities (firm doesn’t pay the full cost) 4 Often critical infrastructures are run by natural monopolists
(water supply, electricity grid, etc.)
16 / 32 Homework 1 Optimal filter configuration Summary statistics Logistical notes Feedback on particular questions
Q5
false positive rate α false negative rate β
1 1 #1 #2 #3
Indifference curves
Suppose you are in charge
an intrusion detection system to balance false positives and false
negative rate is given by β ∈ (0, 1], while the false positive rate is given by α ∈ (0, 1].
17 / 32
Notes Notes Notes Notes