Managing Security Investment
Part III Tyler Moore
Computer Science & Engineering Department, SMU, Dallas, TX
September 25, 2012
Gordon-Loeb model Baseline models
Outline
1
Gordon-Loeb model Breach probability function Decreasing marginal returns Optimal security investment
2
Baseline models Linear breach probability function Exponential breach probability function Investment models in R
2 / 31 Gordon-Loeb model Baseline models
Review of security investment so far
Metrics for quantifying security benefits
1
ALE0: expected loss without security investment
2
ALEs: expected loss with security investment
3
EBISs: ALE0 − ALEs
4
ENBISs: ALE0 − ALEs − c
High-level investment metrics
1
ROSI
2
NPV
3
IRR
3 / 31 Gordon-Loeb model Baseline models
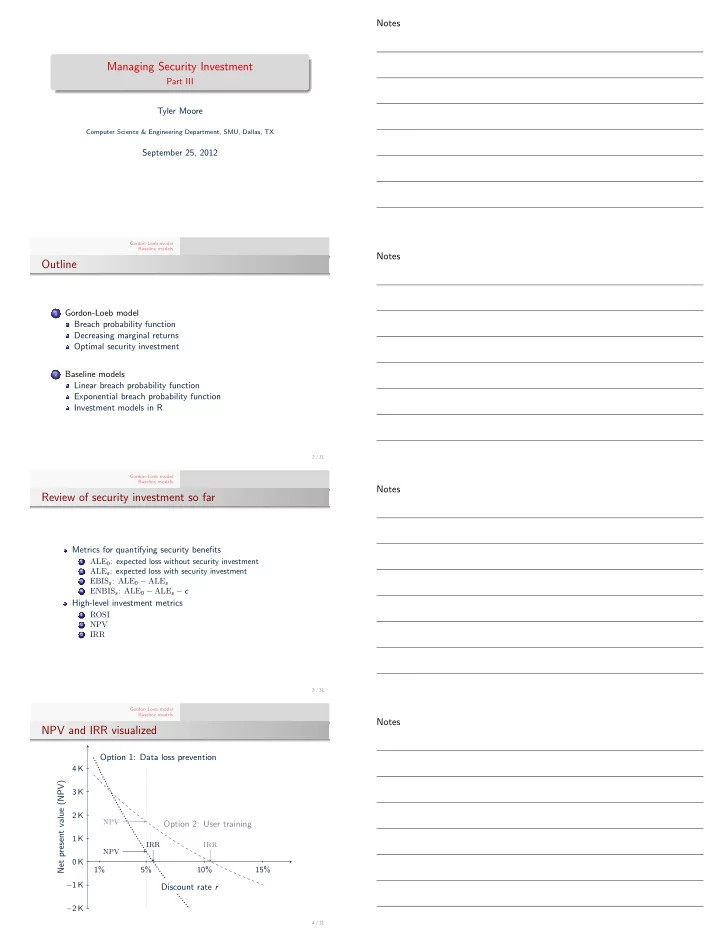
NPV and IRR visualized
Net present value (NPV)
−2 K −1 K 0 K 1 K 2 K 3 K 4 K
Discount rate r
1% 5% 10% 15%
Option 1: Data loss prevention Option 2: User training
NPV NPV IRR IRR
4 / 31