Introduction to Game Theory
Part II Tyler Moore
Computer Science & Engineering Department, SMU, Dallas, TX Slides are modified from version written by Benjamin Johnson, UC Berkeley
November 13, 2012
Miscellania Coordination games and information security Mixed strategies
Outline
1
Miscellania
2
Coordination games and information security
3
Mixed strategies
2 / 26 Miscellania Coordination games and information security Mixed strategies
H3
Median score: 86 Median time to complete: 12 hours (sorry!) H1 and H3 caused the most trouble
4 / 26 Miscellania Coordination games and information security Mixed strategies
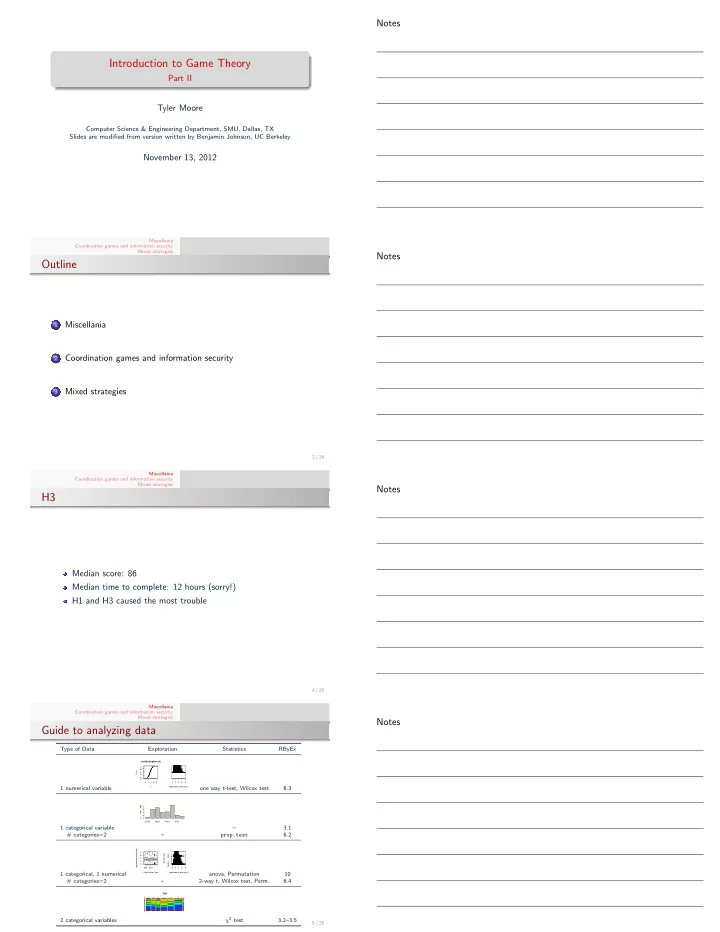
Guide to analyzing data
Type of Data Exploration Statistics RByEx 1 numerical variable
2 4 6 8 0.0 0.4 0.8 ecdf(br$logbreach) x Fn(x) 2 4 6 8 log(#records breached)
- ne way t-test, Wilcox test
6.3 1 categorical variable
CARD HACK PHYS STAT 400 800
– 3.1 # categories=2 – prop.test 6.2 1 categorical, 1 numerical
- BSF
EDU 2 4 6 8 Organization Type log(#records breached) 2 4 6 8 FALSE TRUE log(#records breached) Breach type
- ●
- anova, Permutation
10 # categories=2 – 2-way t, Wilcox test, Perm. 6.4 2 categorical variables
TOH
BSF BSO BSR EDU GOV MED NGO CARD DISC HACK INSD PHYS PORT STAT UNKN
χ2 test 3.2–3.5
5 / 26