1
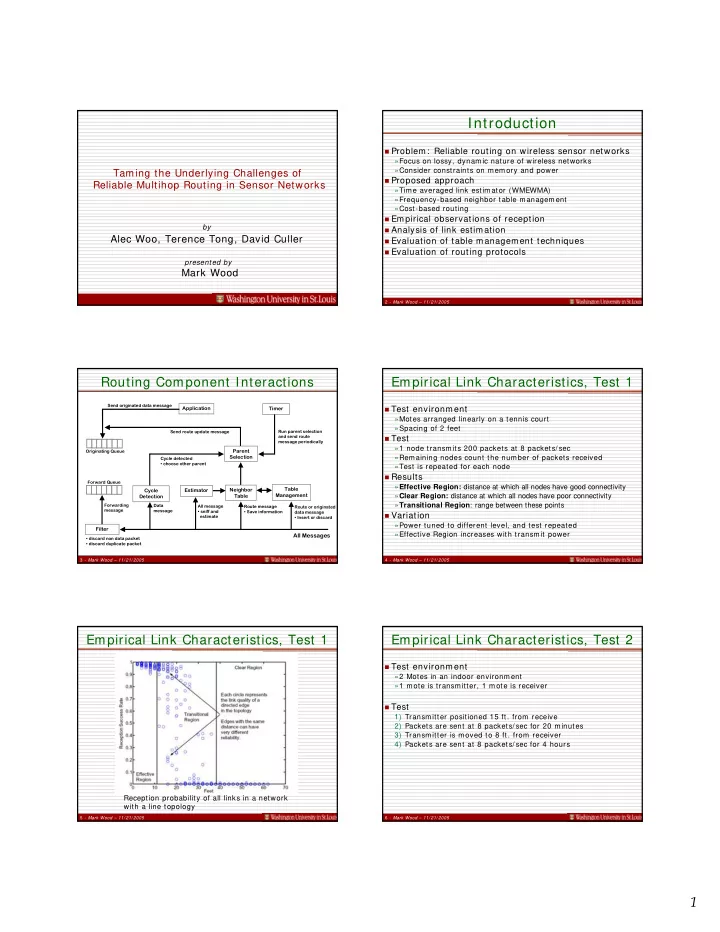
Taming the Underlying Challenges of Reliable Multihop Routing in Sensor Networks
by
Alec Woo, Terence Tong, David Culler
presented by
Mark Wood
2 - Mark Wood – 11/ 21/ 2005
Introduction
Problem: Reliable routing on wireless sensor networks
»Focus on lossy, dynamic nature of wireless networks »Consider constraints on memory and power
Proposed approach
»Time averaged link estimator (WMEWMA) »Frequency-based neighbor table management »Cost-based routing
Empirical observations of reception Analysis of link estimation Evaluation of table management techniques Evaluation of routing protocols
3 - Mark Wood – 11/ 21/ 2005
Routing Component Interactions
Application Parent Selection Table Management Neighbor Table Estimator Cycle Detection Timer
Originating Queue Forward Queue Run parent selection and send route message periodically Route or originated data message
- Insert or discard
Route message
- Save information
Filter
All message
- sniff and
estimate Data message Forwarding message
All Messages
- discard non data packet
- discard duplicate packet
Cycle detected
- choose other parent
Send route update message Send originated data message 4 - Mark Wood – 11/ 21/ 2005
Empirical Link Characteristics, Test 1
Test environment
»Motes arranged linearly on a tennis court »Spacing of 2 feet
Test
»1 node transmits 200 packets at 8 packets/ sec »Remaining nodes count the number of packets received »Test is repeated for each node
Results
»Effective Region: distance at which all nodes have good connectivity »Clear Region: distance at which all nodes have poor connectivity »Transitional Region: range between these points
Variation
»Power tuned to different level, and test repeated »Effective Region increases with transmit power
5 - Mark Wood – 11/ 21/ 2005
Empirical Link Characteristics, Test 1
Reception probability of all links in a network with a line topology
6 - Mark Wood – 11/ 21/ 2005
Empirical Link Characteristics, Test 2
Test environment
»2 Motes in an indoor environment »1 mote is transmitter, 1 mote is receiver
Test