CS 526 Topic 5: Internal Representations University of Illinois at Urbana-Champaign
Intermediate Representation (IR)
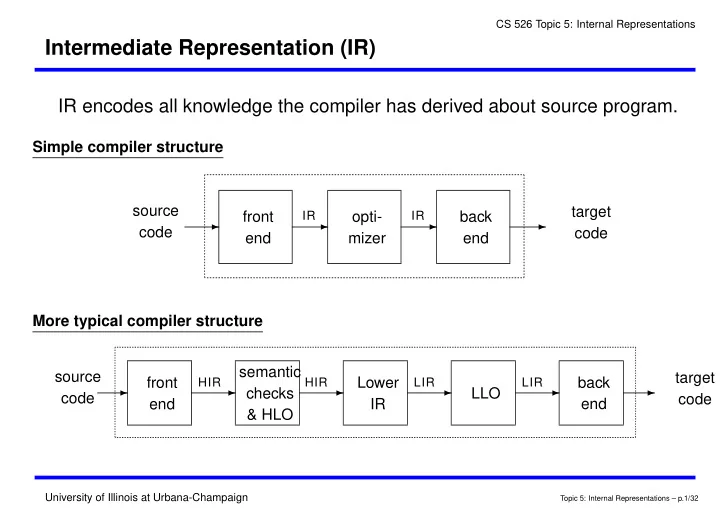
IR encodes all knowledge the compiler has derived about source program.
Simple compiler structure source code front end
- pti-
mizer back end
✲ ✲ ✲ ✲
target code
IR IR
More typical compiler structure source code front end semantic checks & HLO Lower IR LLO back end
✲ ✲ ✲ ✲ ✲ ✲
target code
HIR HIR LIR LIR
Topic 5: Internal Representations – p.1/32